A Guide to Reusable Age Verification

- 01 What is Reusable Age Verification?
- 02 The Problem with Repeated Age Checks
- 03 How Reusable Age Verification Works?
- 04 Regulatory momentum behind reusable approaches
- 05 What are the advantages of reusable age verification?
- 06 How Shufti helps businesses with reusable age verification?
- 07 Next Steps for Businesses Looking to Opt for Reusable Age Verification Solutions
Repeated age checks frustrate users, making them reconsider whether or not to visit the same platform again, which keeps them asking for their age on each visit. At the same time, somewhere a business loses prospective customers and revenue, and the reason is cumbersome age verification steps that deter repeat engagements.
These real-world frustrations highlight the growing challenges in onboarding as traditional one-time age verifications create hurdles, frustrate returning users, and impose significant data management burdens. At the same time, the pressure from authorities on social media, adult content, gaming and gambling platforms is mounting to adapt age verification controls whose effectiveness can be demonstrated.
Reusable age verification helps resolve this tension. A single strong age check produces a privacy-friendly credential which could be used again in revisits or even on partner platforms with consent from the user.
Before we discuss further why reusable age verification matters, let’s understand what it means for businesses and how it works.
What is Reusable Age Verification?
The digital age verification process works by confirming if an individual meets the minimum required age to access a product or service online or an experience.
Modern solutions work by cross-checking identity data such as names and birthdates, official documents like government-issued IDs, and biometrics, including face verification or fingerprints. For example, these providers can quickly match government ID details against trusted databases in seconds to help platforms enforce age limits and protect minors in online environments.
The reusable age verification process revolves around the concept of “privacy by design, which means it works in a way that ensures personal details of users remain confidential.
On the first visit of a user on a platform, an age credential or token is created after a successful age verification check. Hence, this token is a secure digital proof that confirms the person meets the required age. This age credential or token works similarly to a boarding pass at an airport.
Just as a boarding pass allows a person to board a plane without repeatedly showing their ID, the age credential confirms the age of a user without divulging personal details each time. This credential records whether the individual is over or under a given age limit without mentioning other identifiable details.
With appropriate consent and security controls, the same credential can be used again for:
- Future logins on the same platform
- Repeat purchases that require age checks.
- Partner platforms that trust the same verification provider
The result is a model where age is checked once at a high level of assurance, then reused as a privacy-preserving age proof within a defined period rather than repeating the full Identity Verification workflow every time.
The Problem with Repeated Age Checks
Industries that rely on age controls already feel pressure from two directions.
On one side, regulators are updating age verification rules. The UK’s Online Safety Act, French age verification decree (SREN Law), and similar frameworks in other countries expect platforms to implement highly effective checks and can impose heavy fines where minors still reach restricted content.
On the other side, users expect digital journeys to be quick. Whereas the older methods usually involve manually uploading a document or filling out forms by typing the details, many users abandon the sign-up process midway. Studies indicate that up to 40% of users abandon sign-up processes if they encounter repeated age checks, which highlights the need for smoother verification methods.
Moreover, repeated age checks result in:
- Support tickets when checks fail or time out
- Friction each time a returning customer completes an age-restricted purchase.
Consequences of Older Systems
Older systems also tend to collect and store large volumes of personal data. That adds additional obligations under GDPR or other privacy-related regulations because age checks often involve copies of identity documents, face images, as well as details like DOB, residential address, etc.
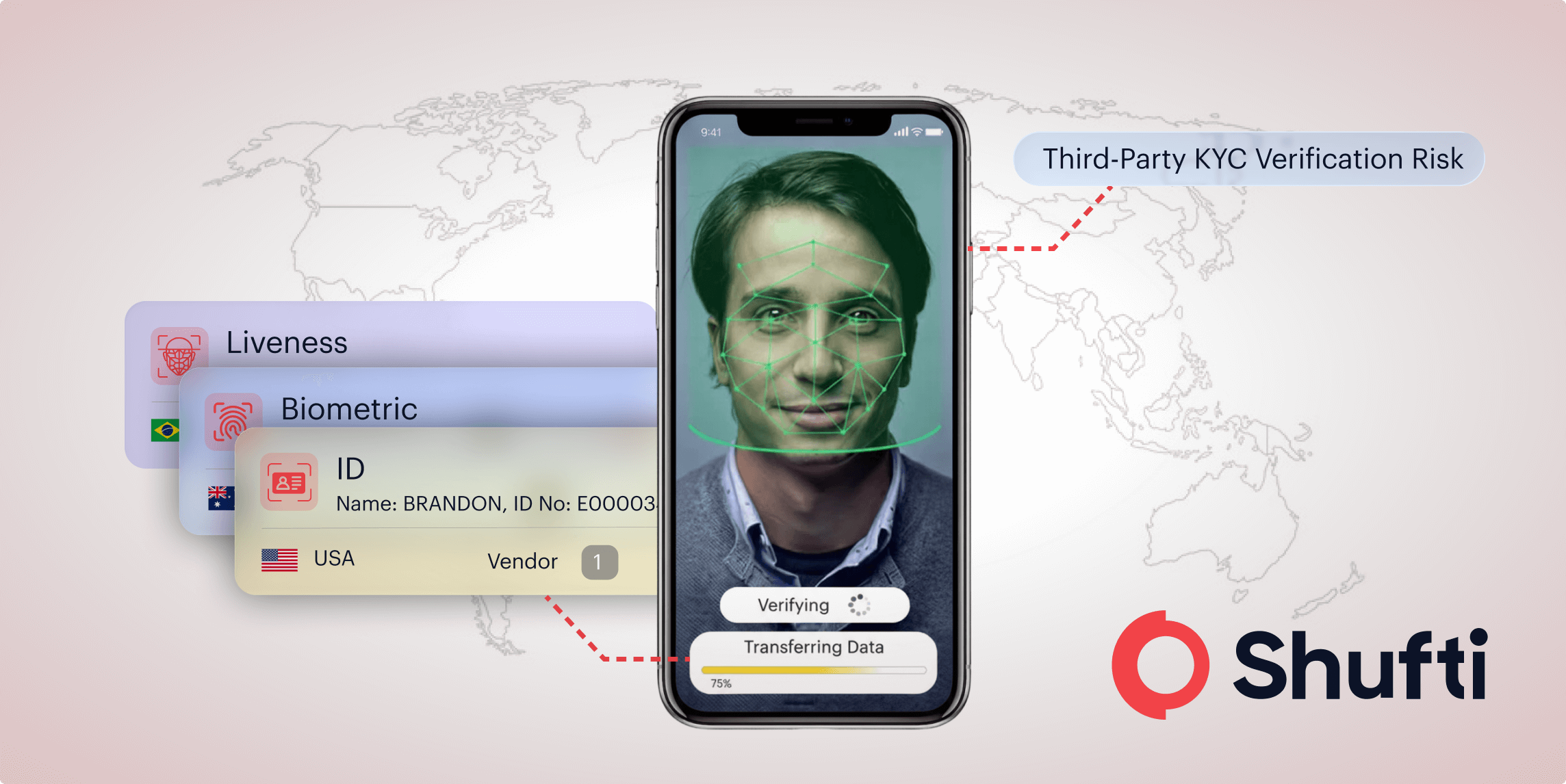
Fraud adds a further problem. Research and industry commentary show that minors use VPNs, borrowed IDs, and low-cost synthetic identities to bypass weak age gates. Businesses now need age verification systems that do not risk both action from authorities and reputational crises.
These are reasons that businesses should seek IDV providers that are capable of providing high assurance without creating friction for users or exposing their personal details. Reusable age verification answers this need and is a practical solution to the issues faced by customers and businesses.
How Reusable Age Verification Works?
Depending on the applicable laws in a jurisdiction and the approach used by the IDV solution, steps involved in reusable age verification can differ; however, the process would normally require the following steps:
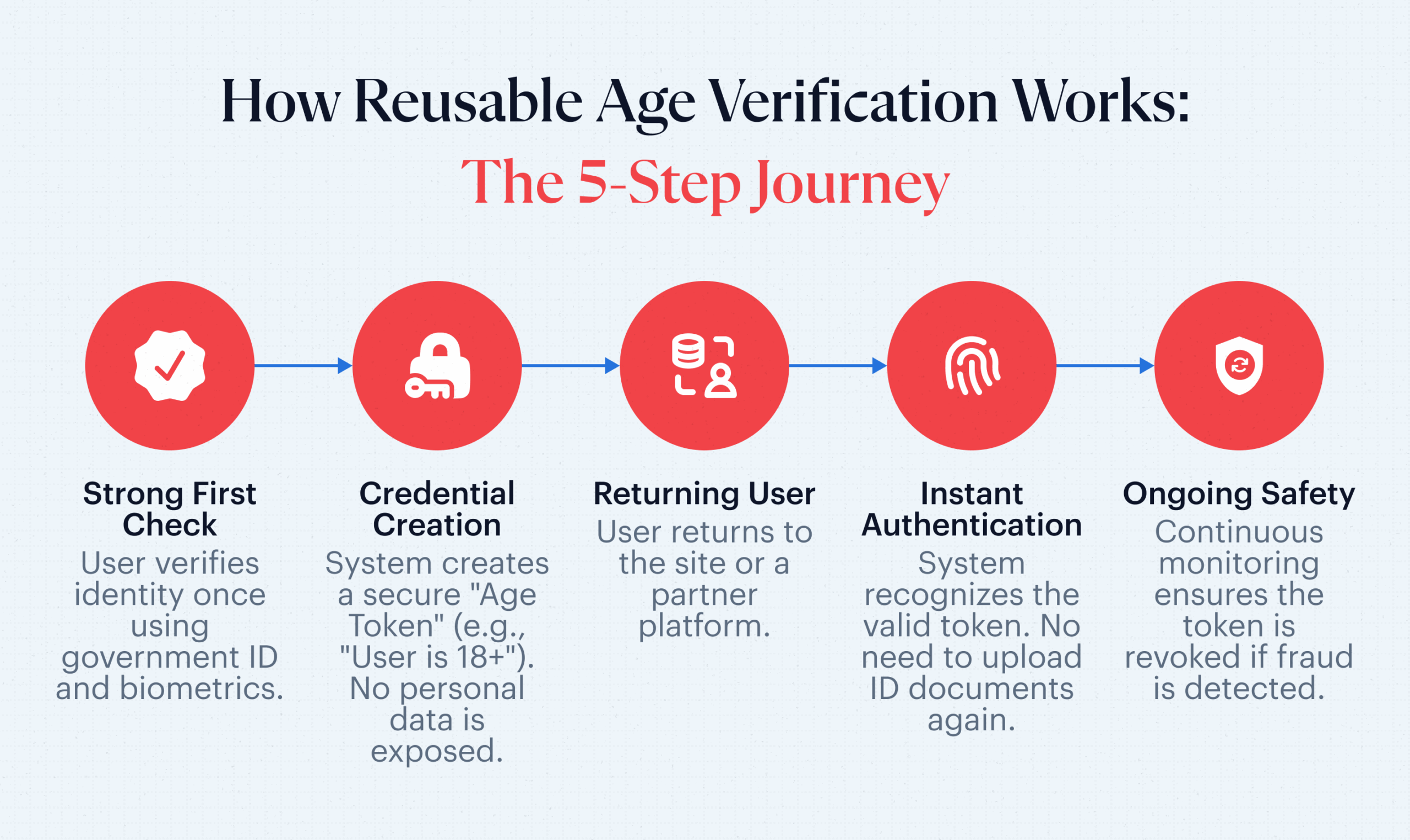
1. Strong first-time verification
The first interaction between a user and the platform uses a high assurance workflow. IDV solutions with advanced capabilities use the following steps:
- Identity document verification with authenticity checks
- Biometric face matching with liveness
- Data cross-checks against official & trusted sources
Where regulations allow, facial age estimation can also be used as an alternative to document verification. Especially in cases where the result is clearly above or below a certain age threshold, age estimation can provide a high level of assurance. This means that personal details of the user are preserved even on the first time verification.
2. Creation of an age credential
Once the check passes, the system creates an age credential. This is not a copy of the identity document. Instead, it records if the person meets a set rule, such as “18 plus” or “21 plus.”
Newer methods use standards for digital identity, which define how identity information is shared online. They may also use device-based keys, which are unique codes stored on a person’s device, or verifiable credentials, which are secure digital versions of certificates. These methods are the key to ensuring the platform learns only what is necessary, not more.
The credential can be held in a user account, a device wallet, or a secure server with access management. In all cases, the goal remains the same, which is a reusable age token that answers the question “is this person old enough” without exposing full identity data.
The initial setup of reusable age verification should include a prominently displayed opt-in toggle for users. This will enable users to decide whether or not to allow the reuse of their details, as well as compliance with GDPR or any other similar privacy laws.
3. Authentication of returning user
When the individual returns, the platform checks whether a valid credential already exists. If the credential is still within its allowed lifetime, only a light touch step is required, such as device biometrics like FaceID or a reusable age verification code on SMS. The system confirms the age status without repeating the full KYC documentation process.
4. Cross-platform interoperability of age checks
Where regulations permit it, the same credential will be used again across partner services that trust the underlying identity provider. Industry initiatives, including the work of the Age Verification Providers Association, explore exactly this kind of interoperable and reusable age proof so that adults can move between compliant services with fewer repeated checks.
5. Ongoing monitoring and revocation
Reusable age check does not mean static, because risk-based controls still apply. Providers can:
- Set expiry dates based on regulation, product type, or internal risk policy
- Re-trigger full checks when documents expire or risk signals change
- Revoke credentials when fraud, chargebacks, or abuse are detected.
Therefore, businesses achieve greater efficiency without having to compromise on required monitoring for age verification checks.
Regulatory momentum behind reusable approaches
Reusable age verification sits within a wider shift toward trustworthy digital identity. FATF digital ID guidance recognises that a well-designed digital identity solution can support remote customer due diligence and lower risk for non-face-to-face onboarding when assurance levels are appropriate.
Regulators and standard-setting bodies mainly emphasize three themes for age controls.
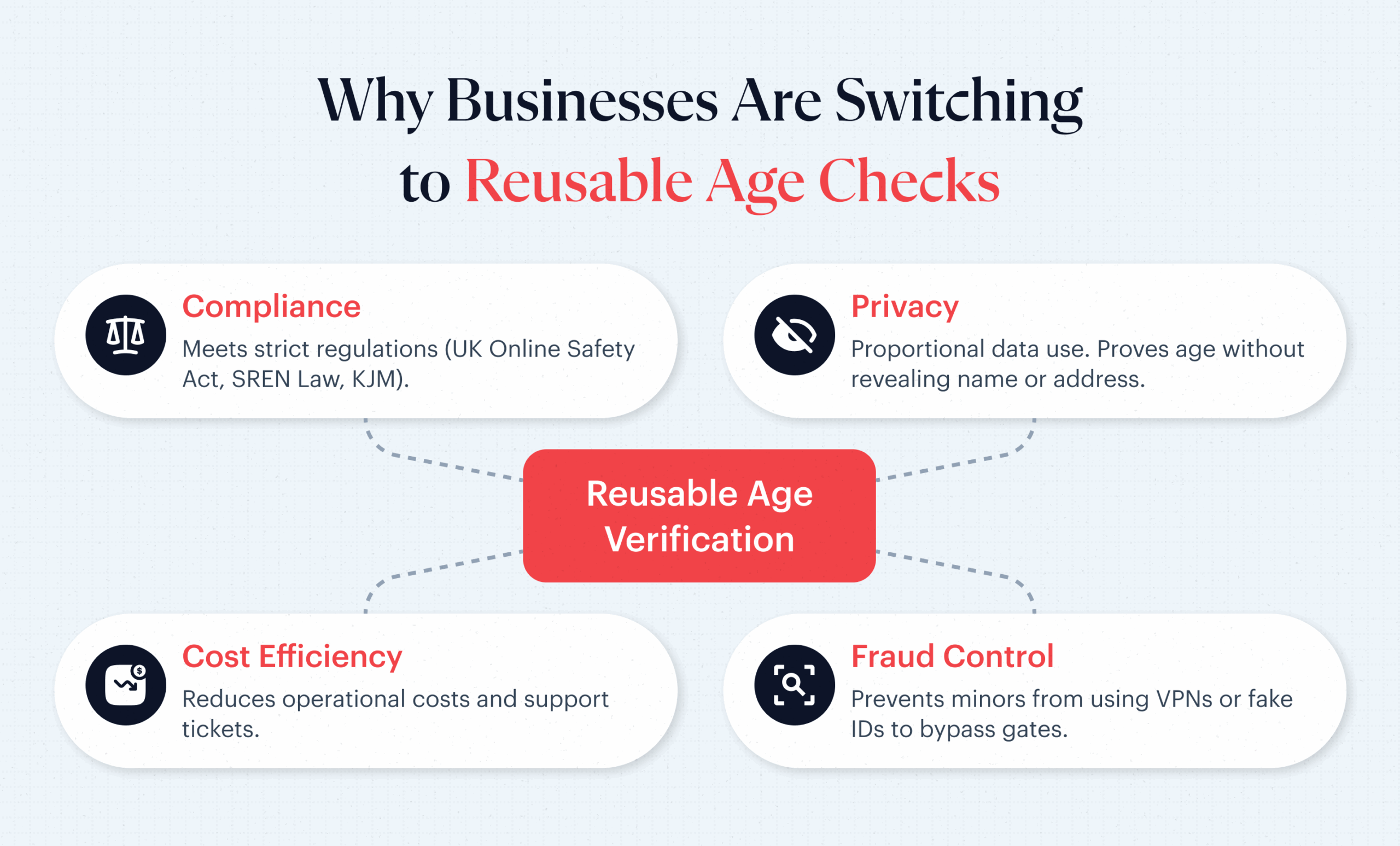
Proportional data use
Laws and privacy regulators expect age-check systems to collect only the minimum personal data required. Reusable age tokens, which only disclose a person’s age status (above or below a set threshold), satisfy the proportional data use requirement as well as the narrative of privacy-by-design.
Higher assurance for high-risk content
Sectors such as online pornography, gambling, and some social platforms face stricter expectations and heavier penalties. Reusable models allow these sectors to maintain high-assurance checks for first-time verification while improving the experience for frequent users through credential reuse.
Future-proof technical standards
Membership of industry bodies, such as the Age Verification Providers Association, and meeting requirements of national standards, such as KJM in Germany, help providers shape and follow good practices for protecting minors online. Shufti participates in these discussions and already delivers KJM-compliant age verification in line with German youth protection rules.
Reusable age verification is, therefore, not simply a convenience feature. It aligns with long-term regulatory direction toward privacy by design, risk-based KYC, and standardised, interoperable digital identity.
What are the advantages of reusable age verification?
Reusable age verification apps support both compliance and commercial goals across sectors such as fintech, iGaming, e-commerce, and social platforms.
-
Faster onboarding & higher conversion
When returning customers skip repeated document uploads and complex forms, abandonment rates fall. Payments complete faster, session time increases, and genuine adults reach the services they are legally allowed to use with far less friction.
-
Lower operational & vendor costs
Each full age check carries a cost, whether internal or external. A reusable model spreads that cost across many sessions. Contact centre and compliance teams handle fewer routine queries, such as “why is my ID being checked again,” which frees resources for higher-value investigations.
-
Stronger privacy posture
Holding fewer copies of IDs and face images reduces exposure under data protection laws and shrinks the damage from future potential data leakages. Age tokens that answer only the question “is this user old enough” support privacy by design and help privacy teams respond to regulators and customer advocates in a credible way.
-
Better fraud control
Reusable credentials also support stronger fraud controls. Providers can link behaviour patterns to a verified age token rather than a fragile cookie or just an email address. When abuse or chargeback patterns are detected, the credential can be revoked and future attempts flagged for enhanced scrutiny.
How Shufti helps businesses with reusable age verification?
Shufti focuses on digital identity, Know Your Customer, and age verification for global digital businesses. The platform combines document verification, liveness checks, biometric authentication, database checks, and risk analysis into a single API that supports high-assurance age checks across a wide range of industries.
Existing capabilities already address key requirements for online reusable age verification, including:
- Instant document and biometric checks for first-time verification
- Flexible workflows that adapt to sector-specific rules, such as gambling, gaming, or e-commerce
- Support for strict regimes, including KJM-compliant age verification for German youth protection laws
- Privacy-focused processes that avoid unnecessary data retention and stay compliant with data protection rules
Shufti is an active member of industry bodies that promote interoperable and reusable age credentials. Moreover, businesses that already partner with providers who offer reusable age verification solutions can quickly adapt in case regulations standardize, and make it a mandatory practice.
Next Steps for Businesses Looking to Opt for Reusable Age Verification Solutions
Many platforms face a difficult trade-off between protecting minors, satisfying regulators, and offering a smooth digital experience. New age checks each time create friction and heavy data obligations, yet regulators around the world demand stronger evidence that underage users do not reach restricted products. Therefore, reusable age verification is emerging as a practical path forward.
A robust first-time age check, followed by privacy-friendly age credentials which can be used again in different sessions and services, helps businesses increase conversion, lower costs, and adopt a more sustainable approach to data protection.
Businesses that want to move toward reusable age verification need a partner with strong verification technology and experience in strict regulatory environments. Shufti is already helping organisations across fintech, gaming, e-commerce, and social platforms to upgrade their age controls while staying compliant with online safety and privacy laws.
Request a demo from Shufti’s team to explore how reusable age verification can fit into current onboarding and trust and safety strategies.

 Explore Now
Explore Now