Why the “Traditional Utility Bill” is Failing POA Verification

Traditional POA verification was built for a world where everyone received paper correspondence, which was difficult to manipulate. Neither of those statements is true today.
Digital-first customers (renters, neobank customers, etc.) struggle to produce physical address documents because they do not rely on physical copies of utility bills, bank statements, or any other document bearing an address. Meanwhile, easily accessible generative AI can now convincingly fabricate a digital POA document in minutes.
For banks and other financial institutions (FIs), the result is an address verification model that creates friction for legitimate digital-first customers, while digital documents offer diminishing resistance to fraud.
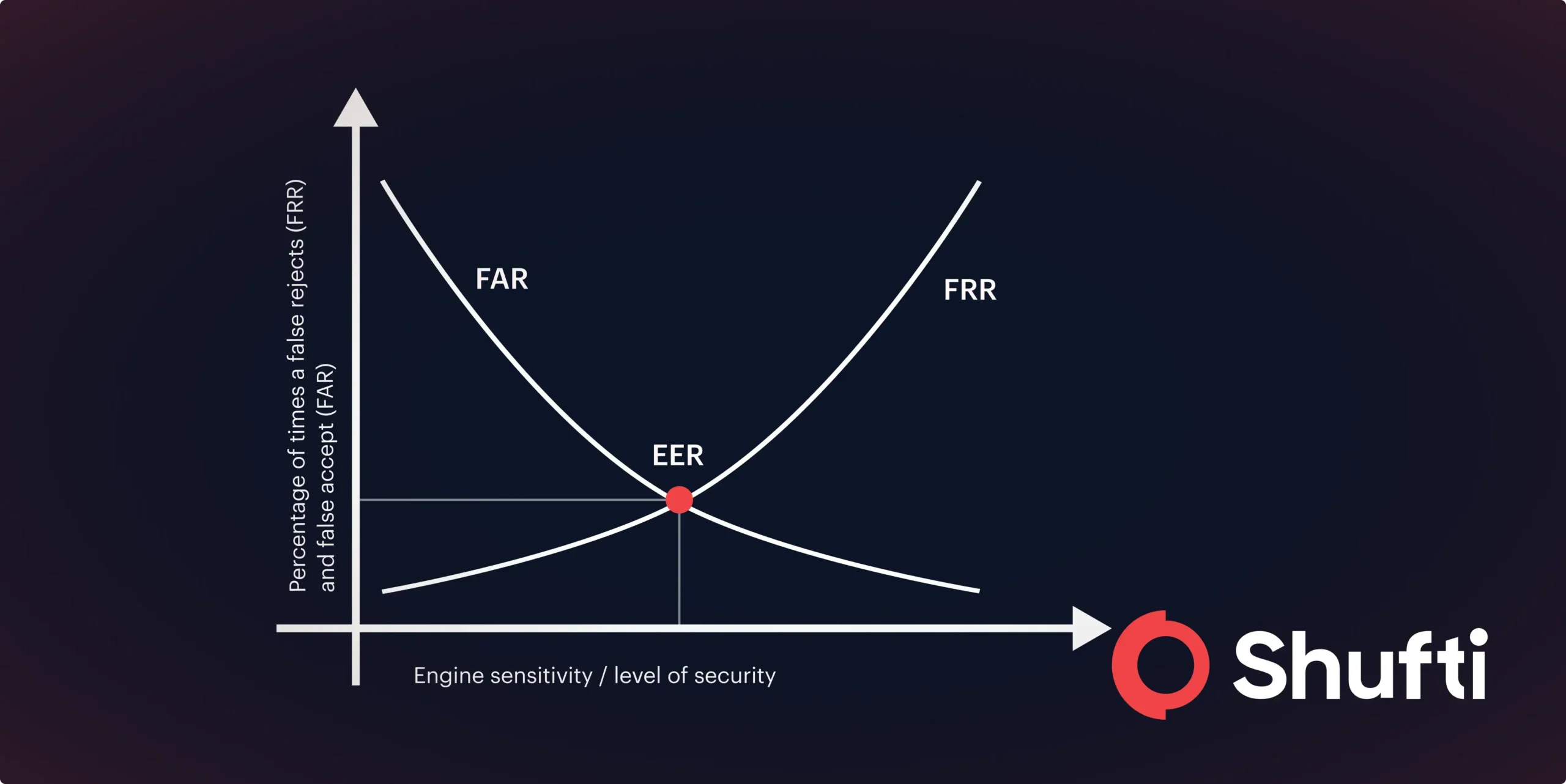
Broader document acceptance (physical and digital) increases conversion but widens the fraud surface. Tighter document requirements reduce fraud exposure but accelerate drop-off.
What is the solution?
How Does Traditional POA Verification Lead to Increased Customer Drop-Off?
Drop-off at the POA step is one of the most ignored causes of revenue leaks in digital onboarding. This is because customers facing friction rarely submit a complaint or call support; they simply abandon the verification process, which is recorded as an incomplete verification rather than a lost customer.
In this sense, the demographic reality is blunt. A growing share of the onboarding funnel is paperless by design, including:
- Digital natives who switched to paperless billing years ago and have no archived PDFs.
- Renters whose utilities are registered in their landlord’s name, not theirs.
- Neobank users who use digital-only financial services that require no physical correspondence.
These groups are not anomalies anymore. In many regulated industries, such groups represent the majority of the onboarding funnel. Traditional POA verification flows that assume paper documents exist are betting against their own conversion rates.
The other problem is that tightening the document requirements to reduce fraud simultaneously increases the drop-off rate for legitimate digital-first customers.
How Gen AI Renders Digital POA Documents: A Flawed Solution
While legitimate digital-first customers struggle to produce physical documents, fraudsters have never found it easier to produce convincing fake ones.
Gen AI has fundamentally changed the effort required to fabricate a POA document. This is because the skills, software expertise, and time required to produce fabricated POA documents have been significantly reduced/made accessible as Gen AI technology has developed. In fact, utility bill templates are readily available online for free, and bad actors could replicate branding and logos in seconds.
The result is a clean, well-formatted PDF that carries none of the pixel-level manipulation signals that traditional fraud checks are designed to detect. This is because the document was never manipulated; it was built from scratch.
This is demonstrated by the increase in POA fraud attempts in recent years. Shufti’s internal telemetry across more than 230 million global checks revealed that
- POA fraud attempts rose 18% YOY in H1 2025.
- Synthetic addresses now account for 42% of high-risk POA cases.
- AI-generated documents trigger 31% of high-risk verification alerts.
This reality puts fraud teams under pressure on two fronts simultaneously: the volume of fraud attempts is increasing, and the quality of those attempts is constantly improving. A robust AI-powered document fraud detection layer- one that goes beyond surface-level forensics to analyze document authenticity – is no longer optional for banks and FIs across the board.
Why Docless POA Verification is the Way Forward:
The document-first model of POA verification makes two assumptions: everyone has a physical document and that producing one is sufficient proof of authenticity.
A growing number of compliance and fraud teams are moving towards a model that verifies addresses directly from databases that hold them on record, such as telecom companies, financial institutions, government registries, and authoritative databases, rather than relying solely on a single POA document.
This direct-from-source approach is a docless verification method that does not require the customer to produce anything. The customer’s name and address information is cross-referenced in real time against live trusted data sources. This docless verification format allows banks and other FIs to verify POA with a significantly reduced fraud threat.
However, docless verification is not appropriate for every risk tier. For high-risk customer segments, it eliminates an entire group of fraud vectors while removing friction for legitimate digital customers.
How a Tiered POA Verification Flow Reduces Fraud?
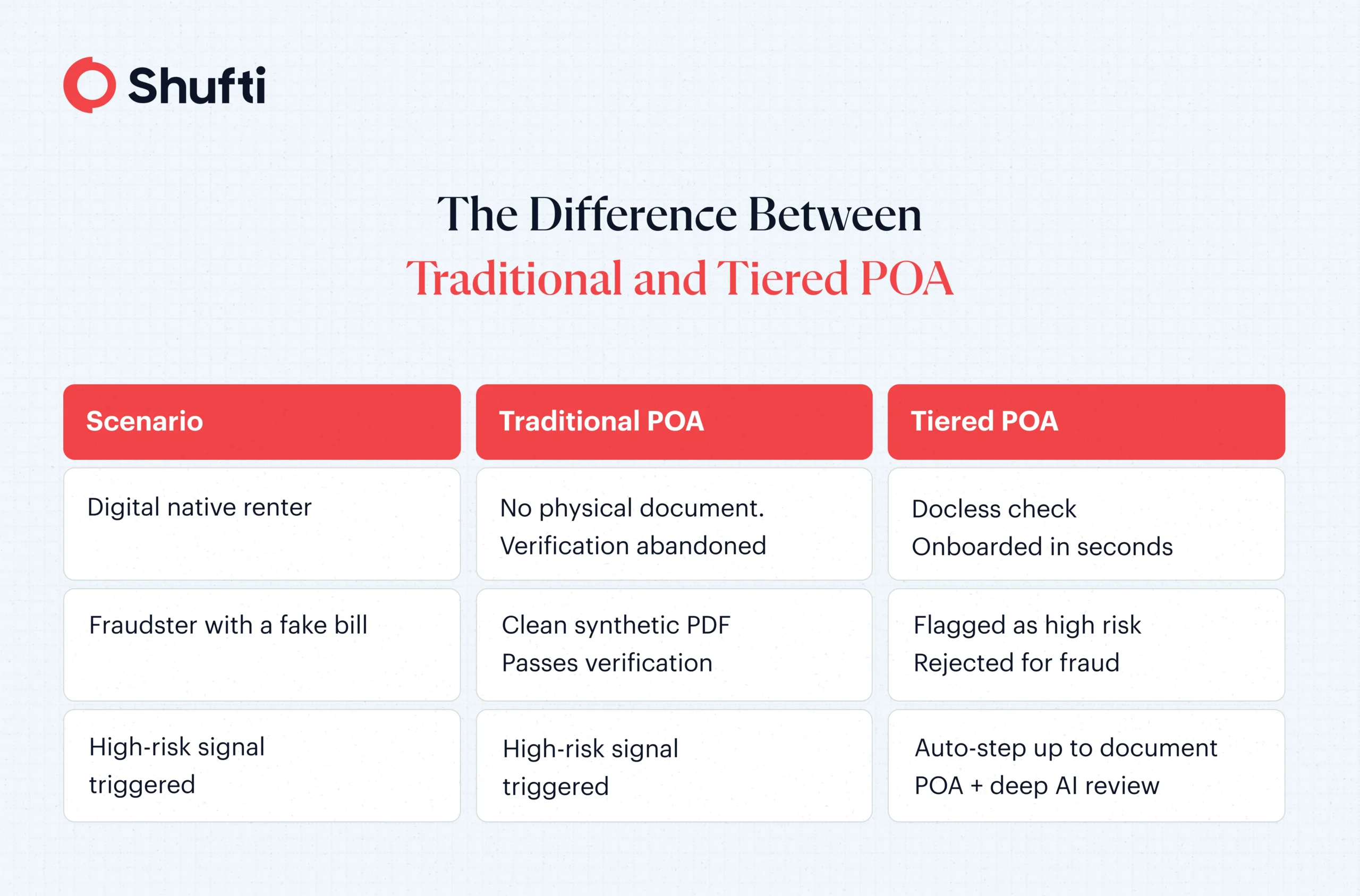
The most effective POA framework is not a single universal method. It is a tiered, risk-based flow that balances fraud prevention and user experience. Here is how a tiered POA verification flow works in practice:
1. Background Docless Check:
The customer inputs their name and address, which the verification system cross-references against trusted data sources. For example, the system could access trusted government data sources to verify the address from the customer’s utility company. This process can be completed in the background in under 3 seconds and requires no action from the customer. Most legitimate customers are verified at this stage.
2. Risk Signal Evaluation:
If confidence in cross-referencing is high and no high-risk signals are present, the check passes. If the system detects a VPN, a geolocation mismatch, or a flagged IP, it routes the customer to the next stage.
3. Document POA with a full forensic layer:
Customers who do not clear the docless check are asked to upload a document for POA. The document goes through deep-AI-powered authenticity analysis (synthetic generation patterns, digital fingerprints, cross-referencing against other submitted documents).
4. Audit-ready results at every layer:
Whether the customer’s POA is verified through docless checks or document review, the verification system assigns a risk score, provides a decision rationale, and creates an audit-ready trail.
The result is targeted friction. The customers most likely to be legitimate will be verified through frictionless, docless verification, while high-risk customers will be asked to upload documents that will be thoroughly analyzed for fraud.
What Modern POA Verification Requires?
Reliance on physical documents for POA, where paper correspondence has decreased and fabricating them is easier, is no longer sustainable.
For compliance and fraud teams evaluating whether their POA stack is catching fraud and clearing legitimate users, an API-based direct-from-source docless layer and a deep AI document fraud detection engine that repels fraud attempts is the perfect solution that caters to every type of customer.
Shufti’s Address Verification Suite enables businesses to adopt this approach with real-time data checks and AI-powered fraud detection. Request a demo to explore how to implement modern POA verification effectively.

 Explore Now
Explore Now