Proof of Address Fraud: How Documents Are Forged and How to Prevent It

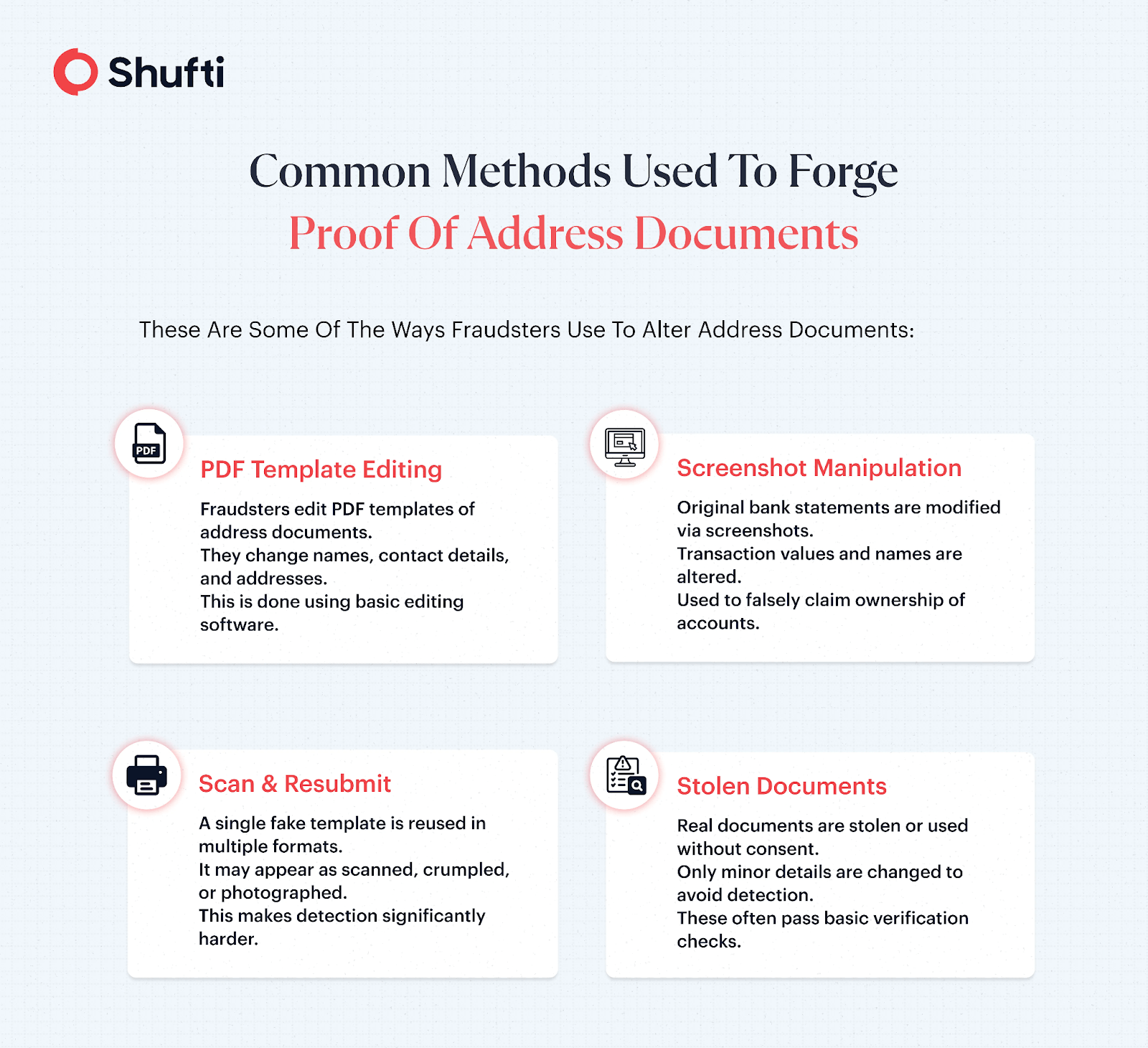
Most proof of address documents can easily be forged and manipulated. It is mainly because of the fact that they weren’t primarily designed to be used for security and verification checks.
Instead, they were designed for billing and correspondence and often are in the form of PDFs and scanned images that have predictable layouts. These documents also lack strong security features that make them more susceptible to fraud in most cases.
Industries Most Affected by PoA Fraud
Proof of address fraud is prevalent in a number of industries. Businesses in these industries often rely on remote onboarding, have strict compliance requirements, and require customers to provide access to their location. These characteristics of the businesses mean that even a small verification gap can lead to major financial losses.
-
Fintech & Digital Banks
Fintechs and digital banks are among the industries that are most affected by digital fraud. Fraudsters use reused and forged POA documents to open multiple accounts and then use them for illicit activities, such as money laundering.
-
Crypto Exchanges
Crypto platforms have to depend on POA to make sure their users are from and reside in jurisdictions that are not restricted. Not just that, they also have to rely on POA to ensure fraudsters don’t manipulate region-based bonuses. If the address verification software they’re using is weak, they’re at risk of large-scale fraud.
-
iGaming Platforms
iGaming platforms use address verification mainly for licensing and region control. Just like crypto exchanges, they too have to make sure users are from the right jurisdictions and are not exploiting the bonus system that is often set region-wise.
-
E-commerce Marketplaces
Marketplaces usually face PoA fraud during seller onboarding. Fraudsters create fake accounts on e-commerce platforms using fake and forged address documents. This poses a huge problem for the business, as it could lead to seller fraud and counterfeit product listings.
-
Forex & Trading Platforms
Trading platforms are also targeted through multiple forged accounts that are used for bonus abuse and exploiting regulatory loopholes. Businesses have to make sure they have strong address checks in place to prevent these frauds from happening.
How Shufti Prevents Proof of Address Document Fraud?
To address these evolving fraud techniques, Shufti uses a combination of advanced AI models and document forensics to detect manipulation patterns that are often invisible to manual review.
Detecting Font Mismatch Attack
The system carefully analyses if the font is consistent throughout the document. Apart from the font, it also looks for differences in typography, how characters are formed, and the spacing between letters and words. Doing so helps identify parts of the document where text or images may have been altered.
Preventing Image Overlay Attack
When an image is altered or replaced in a document, it leaves similar traces to when text is altered. Shufti detects these traces by looking at inconsistencies in how the image is put together on a document. It looks for unnatural edges that are hard to notice with the naked eye. The system also looks for pixel irregularities and mismatched background textures and colours to detect image overlay attacks.
Detecting Multiple Sequential Edits
Document forgery requires multiple edits. This leaves a trace of edits that can be reviewed to see which parts of the documents were altered and to what extent. The platform identifies all the instances where edits were made and then classifies them based on their associated risks.
Performing AI Image Analysis
Some users prefer to submit their address documents in the form of images instead of a PDF or a doc. To detect changes, the system performs a deep pixel-level analysis of the image. Once the analysis is completed, the system generates a ‘manipulation heatmap’ that shows businesses parts of the image with inconsistent lighting, texture, and compression.
Identifying Documents with Different Identities
The software cross-checks the submitted address data with previously submitted documents to detect if a document or a template is being reused. It helps flag documents that have the same structure but different personal details and prevents fraudsters from using one document across multiple identities.
Detecting AI-Generated POA Batch
Documents generated using AI often have common patterns like repeated layouts and subtle inconsistencies that are there due to the synthetic nature of the documents. The platform analyses similarities across multiple submissions and detects bulk-generated documents that are generated from the same source.
Conclusion
Most verification systems weren’t built to check if the document itself is real or not. That means just relying on basic checks or manual review probably won’t save you from fraud, especially when you want to scale. If your current PoA verification can’t spot things like template reuse, sequential edits, or AI-generated batches, it’s probably being bypassed by fraudsters easily without you knowing it.
To effectively prevent these risks, businesses need a more advanced approach to Address Verification that goes beyond surface-level checks and identifies deep manipulation patterns.
Now is the time to take action. Audit your existing workflows, identify blind spots, and move toward a system that can proactively detect manipulation. If you’re ready to strengthen your fraud prevention strategy, you can request a demo to see how Shufti can help secure your onboarding processes.












