Healthcare is the New Target of Criminals – What’s the Solution?

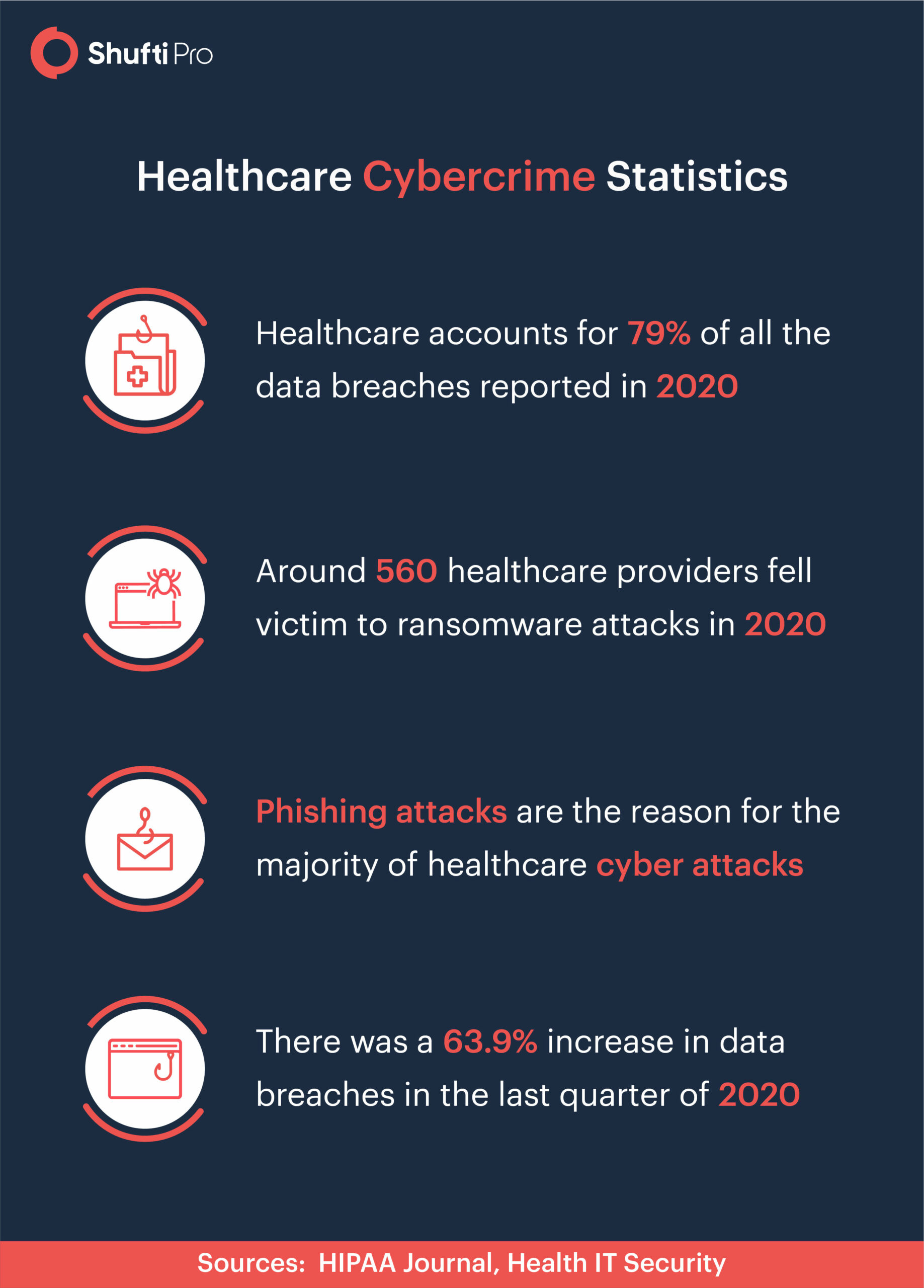
The healthcare sector has been facing many challenges due to coronavirus pandemic. Cybercrimes have significantly increased and this industry has become the primary target of fraudsters. Modern technology has brought several conveniences in the healthcare sector. However, criminals are also using advanced technology to fulfil their malicious intent. The rate of cybercrime rate has skyrocketed in 2020 and the predictions for 2021 are not very satisfying either. According to BBC, healthcare will be on the frontline of cybersecurity in 2021. Different reports have revealed that there is an approximately 50% increase in cyberattacks on the healthcare sector. Fraudsters will figure out better ways to execute their plans but there is a way that can help the health sector in combating them.
Let’s take a look at some of the cybercrimes that have been reported repeatedly, a solution to combat these fraudulent activities, and the regulations to enhance the security of the sector.
What are the Crimes in the Healthcare Sector?
Criminal activities in the healthcare sector are more or less the same as in any other industry. However, the results of these crimes are more severe than what one could expect. Some major crimes in this sector include:
- Data breach
- Ransomware
- Medical identity theft
- Phishing attacks
Ransomware in Healthcare
In a ransomware attack, the criminal injects a virus using three methods; phishing attack, clickbait, malvertising (user clicks on a malicious advertisement). The tactics, techniques, and procedures (TTP) keep evolving with time but the healthcare facility has to bear with the loss. By sending a phishing email or using another ransomware method, the fraudsters gain access to the facility’s database and acquire all the patient records. Many cases of healthcare ransomware were reported in 2020. One of them was the GBMC’s case.
GBMC Healthcare Under Ransomware Attack
As reported on December 9, 2020, by Healthcare IT Security, GBMC healthcare in Maryland was under a ransomware attack on December 6, 2020. The malware was injected in the facility’s IT systems and the hospital claimed that they have been maintaining robust security measures to protect patients’ data. However, there were some procedures scheduled for Monday that had to be postponed.
Data Breach in Healthcare
The average cost of a data breach in healthcare is $158 per record. The staggering numbers make Protected Healthcare Information (PHI) even more valuable than PII. A data breach is an incident in which fraudsters illegally acquire access to the company’s database and use the available information for other illegal activities like identity theft. Only at the end of 2020, the healthcare data breaches rose up to 45% and the healthcare sector overall accounts for 79% of the data breaches reported annually. The top 10 data breaches reported last year exposed millions of records and DCA alliance data breach won the race.
DCA Alliance Breach Exposed 1,000,000 Records
This data breach was reported in early December. DCA is a third-party vendor that supports over 320 affiliated facilities across 20 states. On October 11, some suspicious activity was reported that spurred an investigation. Upon inquiring, it was found out that hackers gained access on September 18 that lasted until October 13. The reports reveal that patient names, billing details, bank account numbers, and health insurance data may have been compromised.
Medical Identity Theft
Medical identity theft is a crime that occurs when fraudsters acquire information of patients and use it for claiming health insurance and other benefits. This fraud results in erroneous entries in the facility’s records and a list of fictitious medical records is created in the victim’s name. Data breaches and ransomware attacks generally result in identity theft and the staggering numbers are raising concerns for regulatory authorities now.
Laws for Countering Crime in the Healthcare Sector
Certain rules and regulations have been structured to ensure the security of all the stakeholders in the healthcare sector. Let’s take a look at some of the regulations that are assisting the health industry in securing facilities.
NHS Good Practices Guidance
NHS Good Practices Guidance provides guidelines about patient verification and their representatives for online services. This guideline provides three identity verification methods; vouching, vouching with confirmation, and identity documents, authorisation guidelines, details of the identity verification process, record keeping, etc.
HIPAA Act 1996
The act has five rules as security measures of patients’ identity; privacy rule, transaction and set rule, security rule, employer identifier rule and enforcement rule. On December 10, 2020, the US Department of Health and Human Services (HHS) released changes to the HIPAA privacy rule. These changes emphasize on strengthening the access of individuals to their information, greater caregiver involvement, and improving access to PHI.
How to Secure the Healthcare Sector?
Securing the healthcare sector is the utmost need of the hour and the industry requires robust identity verification measures to secure patients from medical identity theft. Know Your Patient verification is one solution for ensuring that every patient that requires your facility’s attention is legitimate. KYP is recommended by state laws and in case not employing this ID verification check, hefty penalties have been settled as well. According to the aforementioned regulations, the healthcare facilities must follow the patient identification protocols. With KYP, you can ensure:
- Medical identity fraud prevention
- Responsible selling of prescription drugs
- Better compliance with regulations
- Maintain updated patient records
To protect your facility from data breaches, you need a secure data storage service like on-premises service. This does not store any patient’s information over third-party cloud storage and only the hospital or clinic’s personnel can access it.
Summing It Up
All in all, healthcare has become the primary target of fraudsters and protecting healthcare service providers is the need of the hour. Ransomware, data breaches, phishing attacks, and identity theft are on the rise. Due to the pandemic, the rate of these frauds significantly increased. In 2021, the majority of predictions are threatening for all the hospitals, clinics, and pharmacies. Fraudsters will be using the COVID-19 pandemic in their phishing attacks, whereas other frauds will become more sophisticated. Hence, a robust solution that can fight fraudsters is what this sector needs and KYP is one of the best options. It verifies the identities of all the patients who reach out to you and ensures the legitimacy of patients as well.
Get in touch with us and learn everything about Know Your Patient (KYP) verification today.