Corporate KYC for Streamlined Business Verification and Onboarding

- 01 What is Corporate KYC?
- 02 What Are the KYC Requirements for Corporations?
- 03 What are the Documents Required for Corporate KYC?
- 04 Difference Between Individual KYC and Corporate KYC
- 05 What Type of Businesses Need Corporate KYC
- 06 Benefits of Doing Corporate KYC
- 07 Achieving Corporate KYC with Automation
- 08 How Shufti’s Corporate KYC Helps Make Trusted Business Relationships
Considering a corporate entity for a partnership means asking the question: “How well do you truly know them?”
Before starting a business partnership, it is important to know and have a full understanding of your potential partner. Being the key part of anti-money laundering regulations, corporate Know Your Customer (KYC) is essential in today’s business landscape, and all organizations must satisfy these standard principles to ensure regulatory compliance and mitigate risk.
Corporate KYC focuses on both the individuals who control a business and the business entity itself. It safeguards the global banking system and fills the security gaps in business relationships. KYC for corporate clients helps businesses ensure:
- Adherence to legal and regulatory compliance as enforced by the financial institutions and regulatory authorities.
- Prevent the financial risks (money laundering, fraud, and terrorist financing).
- Identify and mitigate both businesses’ and customers’ activities that may harm businesses and others.
What is Corporate KYC?
Corporate KYC, also known as KYB, is the process of verifying corporate entities. Unlike simple Know Your Customer (KYC), this process includes the verification of the business as well. It is the way an enterprise takes time to conduct essential due diligence procedures to ensure that the business entity it partners with is compliant with the regulations.
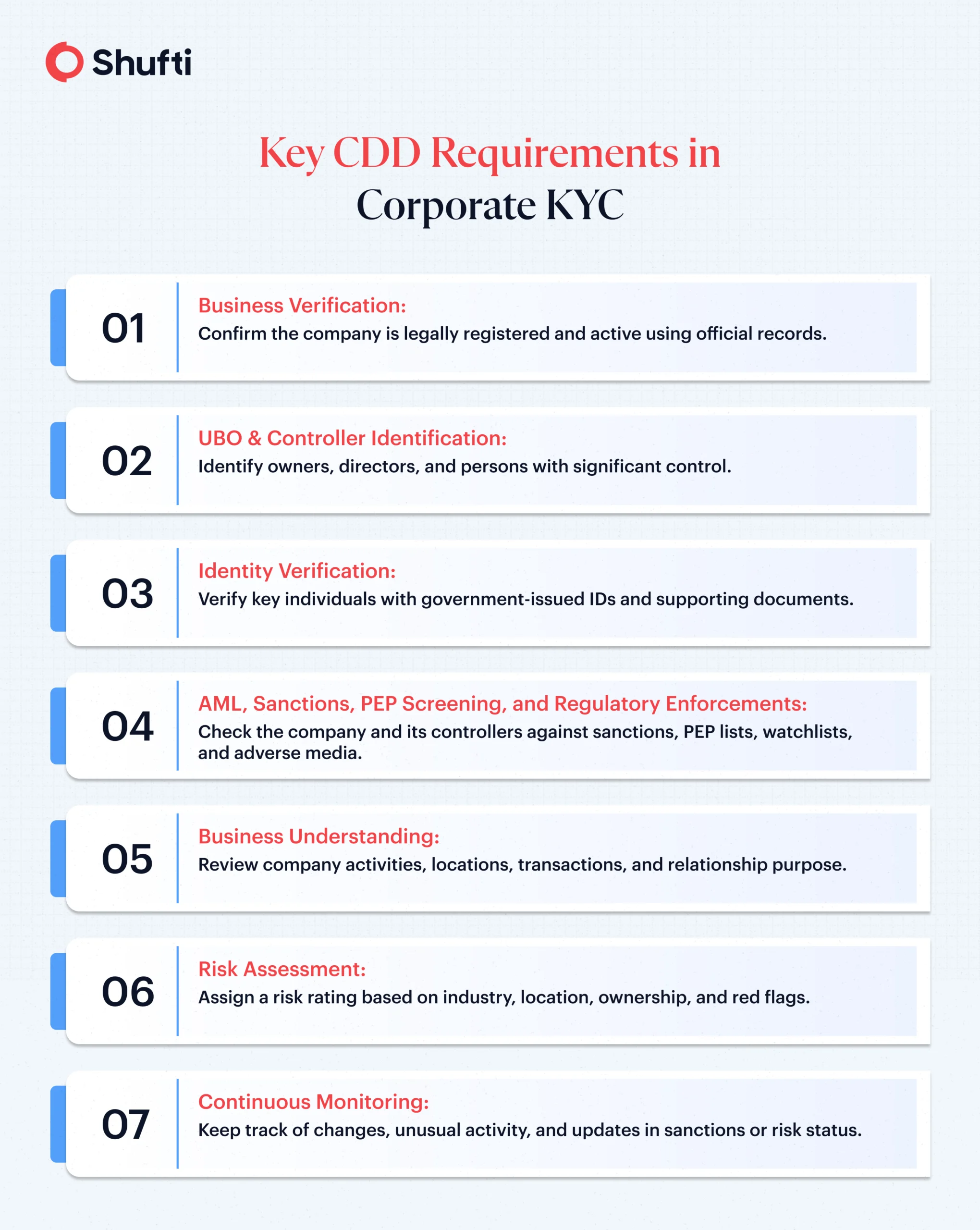
What Are the KYC Requirements for Corporations?
Globally, the anti-money laundering regulations mandate that businesses and financial institutions must verify the important details about the organization. This includes verifying:
- Name of business entity
- Business registration number
- Registered business address
- Key persons (directors and managers)
- UBOs and shareholders
- Screening the entity against government databases (watchlists, sanctions lists, PEP lists, adverse media, and regulatory enforcements)
What are the Documents Required for Corporate KYC?
Verifying a corporate entity is important for understanding the business entity you wish to partner with. During a KYB check, the following corporate KYC documents are required:
-
Business registration documents
A business should legally exist and should be registered with the relevant authority. This means that the business should be authentic and not a shell company. To certify the authenticity, the following documents are important:
- Certificate of incorporation
- Business license
- Articles of Association
- Articles of incorporation
- Partnership agreement
-
Proof of Address and Legal Status
Verifying a company’s proof of address (PoA) ensures that it exists physically and has legal operations. Relevant documentation includes:
- Registry extract
- Certificate of good standing
- Official PoA document with a registered address
- Utility bills (not older than 3-6 months)
- Lease agreements
-
UBO and Ownership Information
This information helps to understand the way ownership is structured and the key people who control the business. Verifying the identity of these individuals allows companies to know who has the most authority and to assess any potential involvement in illegal activities. Key documents are:
- Shareholder/UBO register
- Business activities & ownership percentages
- List of directors
- National ID and passport
-
Financial Information
Checking a corporate entity for its financial and tax history is another requirement during the corporate KYC process. These records confirm the company’s legal and financial standing. Documentation to evaluate is:
- Tax identification number (TIN)
- Annual financial statements
- Bank statements and transaction receipts
Difference Between Individual KYC and Corporate KYC
The nature, scope, and sophistication are the elements that differentiate a simple KYC check from business KYC. While individual KYC focuses on verifying a single person’s identity, corporate KYC goes further and addresses the entire business entity.
| Individual KYC | Corporate KYC |
| Verifies the customer’s identity and background | Verifies an entire business entity, structure and financial standing |
| Simple and straightforward | Relatively complex and with multiple layers of verification |
| Limited to personal information and risk profile | Extends to business details, ownership structure, activities, and associated risks |
| Require ID, proof of address and background checks | Requires incorporation documents, UBO details, shareholder data, and tax info |
| Does not involve UBO checks | Mandatory UBO checks and verification |
| Risk assessment of the customer’s occupation, location, and source of funds | Risk evaluation based on business model, industry risk, region, and UBOs |
| Needs monitoring of the customer | Ongoing monitoring of business changes, ownership updates, sanctions status and suspicious activity |
What Type of Businesses Need Corporate KYC
Any organization onboarding a new client should perform KYC for a corporate entity to ensure compliance. Policies encompassing corporate KYC are for companies that have a business-to-business relationship. Each jurisdiction may define its corporate KYC differently, but generally, the industries include:
- Banks/Financial Institutions
- Securities Brokers/Dealers
- Cryptocurrency Companies
- Fintech Companies
- Credit Unions
- Asset Management Firms/Mutual Fund Companies
- Marketplaces or platforms with B2B Vendors
- Payment Service Providers or MSBs
Benefits of Doing Corporate KYC
Corporate KYC provides banks with many advantages and allows organizations to safeguard their clients’ financial security while creating substantial value for banks through the overall KYC process of verification and onboarding. Some benefits of corporate KYC are:
- A bank’s compliance with regulations at both the national and global levels.
- Reduction of risk associated with non-compliance, such as fines, penalties, or sanctions.
- Identifying and mitigating potential risks, specifically high-risk activities that would pose a threat to other customers.
- Increasing the quality and reliability of data used in screening corporate entities, especially when verified through reliable sources and proper tools.
- Building and maintaining solid relationships and credibility with clients, partners, and other stakeholders by leveraging responsible compliance methods.
- Improved ability to combat fraud and other types of financial crime through the implementation of solid security protocols.
Achieving Corporate KYC with Automation
Manual KYC for businesses is extensive and tedious. Advanced KYB solutions automate the laborious steps required for a comprehensive process. From collecting documents to reviewing evaluations, automation helps cut the additional tasks, resources, and time.
An automated KYB solution should have advanced features such as machine learning to identify patterns and suspicious activities indicating suspicious activities related to the business entity. Moreover, it should also be able to pull data from official registries and sources and also screen UBOs and other key persons against government databases (sanctions lists, watchlists, adverse media, regulatory enforcements, and PEP lists).
How Shufti’s Corporate KYC Helps Make Trusted Business Relationships
As business structures grow more complex and fraud tactics evolve, relying on limited or outdated KYB methods exposes companies to serious compliance and reputational risks.
Shufti solves this by delivering a unified, AI-powered KYB framework built for modern global verification. With access to official registries in over 240 jurisdictions, advanced ownership mapping, and continuous monitoring, the solution empowers businesses to uncover hidden risks and make informed decisions with confidence.
It also verifies a company’s legitimacy, ownership, and risk profile in one seamless workflow, which means businesses can strengthen trust and reduce risk exposure by leveraging:
- Global registry intelligence: Instantly retrieve official business filings, registration details, and ownership structures from 240+ countries and territories using continuously updated data.
- Deep UBO and director verification: Identify real stakeholders beyond surface-level shareholders, uncovering multi-layered or offshore ownership networks in seconds.
Sanctions and media screening: Screen entities and controllers against PEP lists, sanctions databases, and global adverse media with high precision to avoid false positives. - Continuous monitoring: Track regulatory status, sanctions changes, and updates to ownership records in real time for ongoing compliance assurance.
Request a demo to discover how Shufti transforms KYB from a one-time check into a continuously reliable business trust layer.