Injection Attack Types, Impacts, and Mitigation Strategy in IDV Systems

- 01 What Are Injection Attacks and Why Do They Target IDV Systems
- 02 How Injection Attacks Work in IDV: Understanding the Core Exploitation Mechanism
- 03 Injection Attack Types and Mitigation Strategies for IDV Systems
- 04 Injection Attacks Impact on Businesses, Compliance, and Customer Trust
- 05 Shufti Strengthens Identity Verification Against Injection Attacks
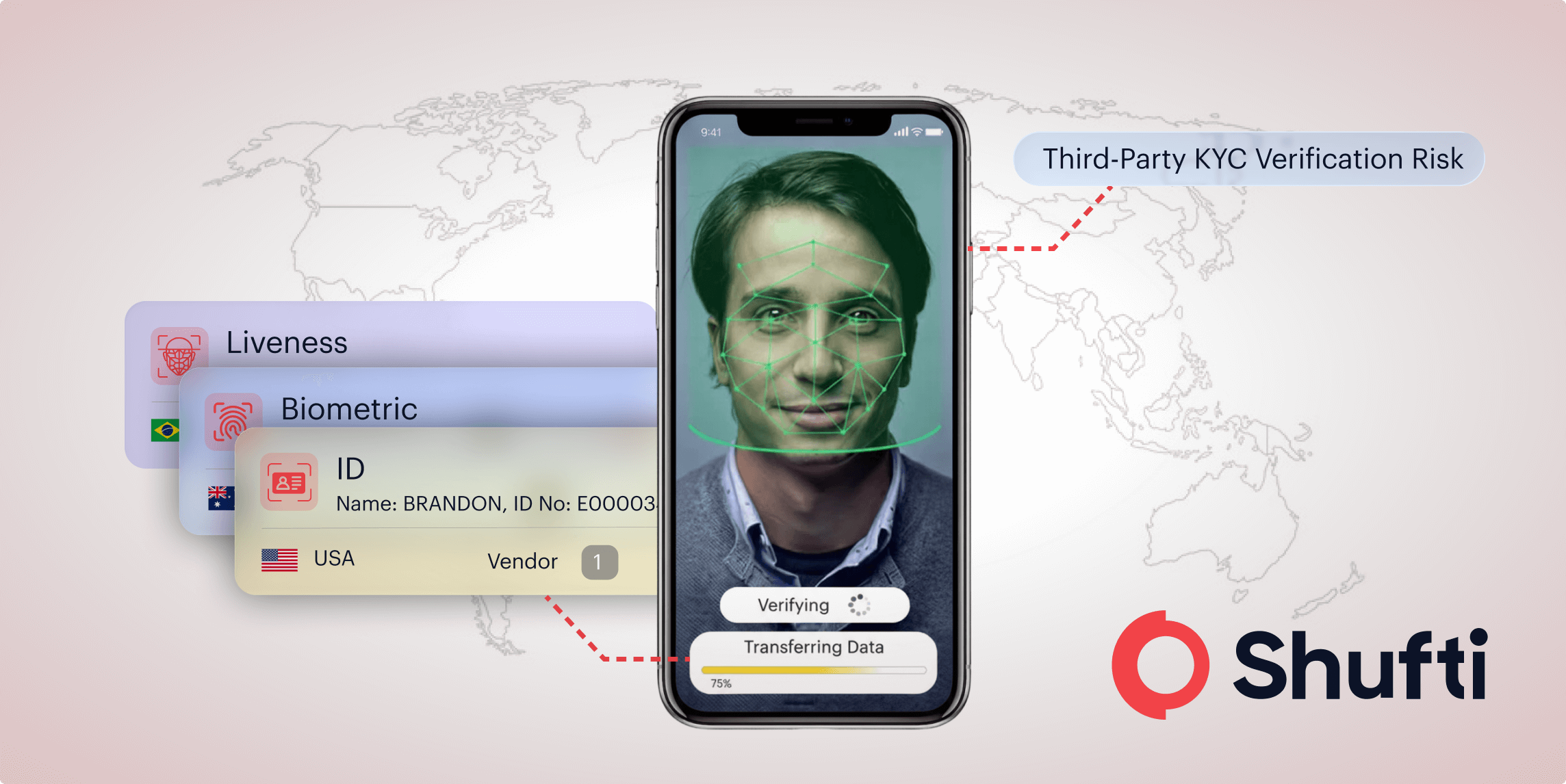
Financial institutions, fintech platforms, and digital businesses all routinely rely on identity verification (IDV) systems to onboard users securely. Among these and other online industries, injection attacks remain a primary security concern. That too happens even within modern IDV frameworks that enforce input validation and secure data processing practices.
The effectiveness of such attacks is due to the fact that it takes advantage of the implicit trust verification systems that depend on user-provided identity data, be it documents, videos, or maps, or API payloads. They enable non-authorized alteration of verification processes, validity of documents, biometric identity matches, and decision logic.
The impact goes beyond mere technical breaches. As, it also exposes organizations to regulatory fines, compliance failures (KYC/AML), identity fraud, and large-scale onboarding risks.
Prior to the discussion of the intricacies of the injection attack, such as its mechanisms, and the way to alleviate them. Let’s start by understanding the concept of injection attacks.
What Are Injection Attacks and Why Do They Target IDV Systems
In simpler terms, injection attacks in IDV occur when unverified or manipulated input interferes with identity verification processes. It allows harmful data, scripts, or media to alter the system’s decision-making.
Though injection attacks have been a well-known concept within application security models such as OWASP Top 10, within the IDV context, these attacks pose several threats related to biometric systems, OCR engines, and real-time verification pipelines.
This negligence enables the attacker to compromise the verification results and identity controls. Some of the common vulnerability points in IDV systems are:
- Document uploads (OCR pipelines)
- Selfie and video verification streams
- API-based identity submissions
- Liveness detection systems
- Authentication workflows
- Third-party data integrations
It implies that injection attacks may take place in any interface where identity data interacts with verification engines.
Therefore, effective injection attacks in IDV may result in:
- Identity fraud and synthetic identity creation
- Unauthorized account creation
- Biometric spoofing and liveness bypass
- Data exfiltration of sensitive identity records
- Verification decision manipulation
- Remote system compromise in verification pipelines
In the regulated industry, these events can also result in the violation of the KYC/AML requirements and data protection regulations and cause penalties, legal liability, and loss of reputation.
Consequently, it is important to be aware of the consequences, but finding out how injection attacks in IDV work can result in the knowledge of why they are so successful.
How Injection Attacks Work in IDV: Understanding the Core Exploitation Mechanism
Injection attacks in identity verification follow a predictable but dangerous pattern that exploits untrusted identity inputs to manipulate verification engines and backend systems. The fundamental mechanism may be construed in the following way:
- The attacker provides distorted identity data (data in documents, pictures, video stream, or API payloads).
- The system receives the input without due validation or integrity checks.
- Malicious payloads interfere with OCR parsing, biometric analysis, or decision logic
- The verification system produces a false positive or executes unintended actions
With the core mechanics clear, it is time to look at some of the IDV-specific attack vectors and the defenses guarding identity verification systems.
Injection Attack Types and Mitigation Strategies for IDV Systems
Injection attacks in IDV target vulnerabilities in document processing, biometric verification, and identity workflows based on APIs. Using unverified identity-feeds, they exploit verifiable identity-feeds to bypass or compromise results.
OCR Injection (Document-Based Attacks)
The verification systems are injected with pre-recorded or synthetic video streams of virtual cameras rather than real ones. This enables impersonation and gets around liveness detection. Mitigation involves the identification of virtual environments, provision of challenge-response, and the implementation of controls on device integrity.
Video Injection & Virtual Camera Attacks
Pre-recorded or synthetic video streams are injected into verification systems using virtual cameras instead of real-time capture. Bypasses liveness detection and enables impersonation. Virtual camera environments can be detected, real-time challenge-response can be enforced, and device integrity checks can be used.
Face Swap & Deepfake Injection
Facial data generated or manipulated by AI is inserted into biometric authentication procedures. This compromises the facial recognition systems and facilitates identity theft. In order to reduce risks, companies are advised to use sophisticated liveness detection, deepfake detection models, and multi-mode biometric verification.
API Payload Injection in IDV Workflows
False requests sent to the API or other JSON manipulation, modification verification, or bypass checks. This leads to falsifying identities or missed verification procedures. For this, control is required in the form of strong schema validation, authenticated requests, and strict input validation.
Session Injection in Verification Flows
In identity verification, attackers alter the session tokens so that they can hijack the active session or reuse the authenticated identities. Hijacks verification sessions or reuses approved identities. Mitigation strategies that are critical include secure session handling, token rotation, and binding sessions to particular devices.
Template Injection in Verification Engines
The user-controlled inputs disrupt the templates in verification workflows or reporting systems. This has the ability to change outputs or cause unintentional backend execution. Such exploitation can be prevented by limiting dynamic rendering and providing complete input sanitization.
Data Injection in Identity Databases
Verification references and decision logic are manipulated by entering malicious identity records into databases. This corrupts identity records and facilitates fraud on a large scale. Companies have to authenticate data sources, implement integrity checks, and track anomalies on a regular basis.
Injection Attacks Impact on Businesses, Compliance, and Customer Trust
Injection attacks in IDV are menacing business continuity, financial sustainability, and reputation. The breaches may damage onboarding pipelines, facilitate massive fraud, and interfere with regulatory alignment.
Regulatory sanctions under GDPR, CCPA, and KYC/AML products and services have the effect of increasing the risks, and multiple verification failures indicate lax identity controls. The strong validation mechanisms, constant monitoring, and secure identity workflow can be used to minimize the threats.
Shufti Strengthens Identity Verification Against Injection Attacks
Identity verification in injection attacks is rapidly evolving, frequently targeting biometric systems, document-handling pipelines, and API-driven workflows.
To enhance the security of identity systems, organizations should be aware of the types of attacks that IDV attackers target, detection, impact, and prevention strategies.
Shufti assists companies to enhance identity trust and reduce the exposure to fraud by protecting verification processes, spotting spoofing, and adhering to international standards.
Request a Demo to proactively mitigate injection attack risks and enhance identity verification security.

 Explore Now
Explore Now