How Deepfakes Threaten Age Verification and What Stops Them

Gartner’s February 2024 analysis found that 30% of enterprises will stop treating standalone identity verification as reliable by 2026, with AI-generated deepfakes named as the primary cause. For platforms running age verification, that is not a forecast. Deepfake selfies, AI-generated identity documents, and video replay injections are already reaching live verification queues.
Age verification carries a specific vulnerability that general identity checks do not. The attacker is often a minor trying to access gambling, adult content, or alcohol purchasing rather than a sophisticated fraud ring. That lower-stakes goal makes the attacks cheaper to mount and the tools more widely available. This article explains how those attacks work, why document scanning alone cannot catch them, and what a deepfake-resistant age check actually requires.
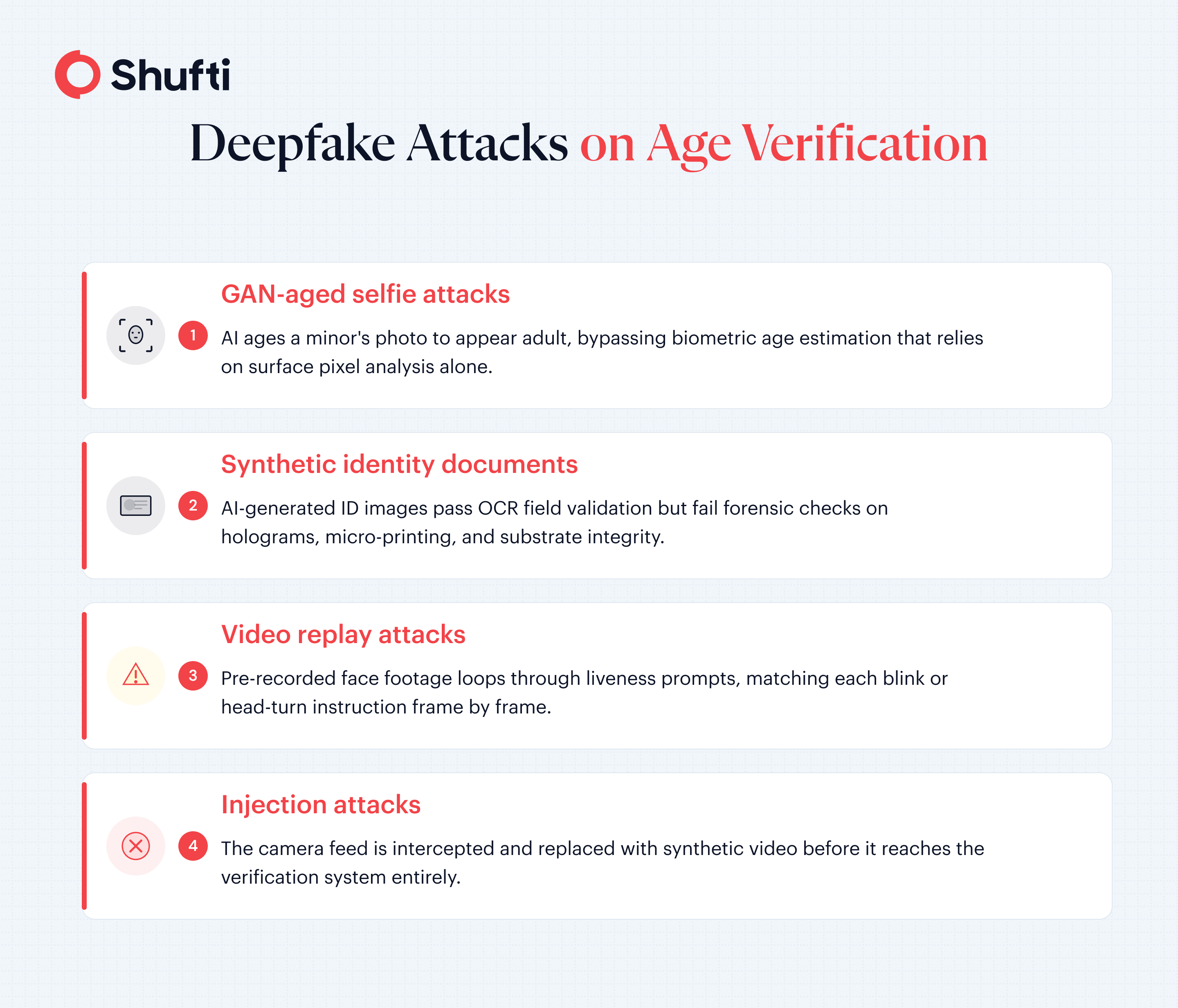
A deepfake, in the age verification context, is any AI-generated or AI-manipulated media artifact used to misrepresent a person’s age or identity during a check. The category covers generative adversarial network (GAN)-aged selfies, synthetic identity documents, and pre-recorded video streams substituted for a live camera feed.
Why Deepfakes are the Fastest Growing Threat to Age Verification
Age verification systems were designed for a simpler attack surface. A teenager borrowing a parent’s driving licence, a date-of-birth field left unchecked. Those were the original threat models. Generative AI has changed economics entirely. The tools needed to age a selfie convincingly, generate a synthetic passport image, or replay a pre-recorded liveness session are now commercially available and, in several cases, free to download. What has emerged is a class of attacks that document scanning and basic photo matching were never built to detect.
How GAN-aged Selfies Defeat Age Estimation
Generative adversarial networks can age a minor’s photograph convincingly in under a minute using tools readily available online. The output presents to age estimation models as a mid-30s adult face. Age estimation that relies on pixel-level surface features visible to a red-green-blue (RGB) camera is the first control to fail. The manipulated image passes because GAN output specifically optimises to fool statistical classifiers. What GAN-generated images do not replicate cleanly are the spectral artefacts visible under frequency-domain analysis. Pupil-ring noise, hairline bleed, and the micro-texture patterns that appear under infrared or three-dimensional depth scanning are all biological signals that a trained detection model identifies and an RGB-only system misses entirely.
How Synthetic Identity Documents Expose OCR-only Checks
A second attack pairs a GAN-aged selfie with an AI-generated identity document. Optical character recognition (OCR) validates the text fields on a submitted ID, including name, date of birth, and document number. OCR does not analyse whether the document’s substrate, holograms, micro-printing, or colour gradients are genuine. An AI-generated passport image containing a correctly formatted date of birth will pass field validation while failing every physical forensic check. Deloitte’s analysis on banking deepfake fraud projects that generative AI could drive fraud losses to $40 billion in the US by 2027, up from $12.3 billion in 2023. Age-gated platforms account for a growing share of that exposure, particularly those relying on OCR as their primary defence. For a broader look at how minors bypass age gates, see how weak age verification is being exploited.
How do attackers use deepfakes to bypass age checks?
The attack surface for deepfake fraud on age verification divides into two categories, each requiring different detection controls. The first operates at the presentation layer, meaning what the camera actually sees. The second operates below it, at the data transport layer, where what gets sent to the verification system is substituted in place of a real camera feed. A system that defends one while ignoring the other remains open to the other vector.
Presentation attacks: what arrives at the camera
A presentation attack occurs when an attacker presents something other than their live face to the camera. For age verification, the most common forms are printed photographs of an older person, a screen displaying another face, a three-dimensional mask, or a GAN-generated selfie of an artificially aged version of the attacker. iBeta Quality Assurance, a National Institute of Standards and Technology (NIST) National Voluntary Laboratory Accreditation Program (NVLAP)-accredited biometric testing laboratory, classifies artefacts under ISO/IEC 30107-3 into Level 1 items (static and inexpensive, such as printed photos and screen displays) and Level 2 items (dynamic and engineered, including three-dimensional masks and deepfake video). Both types exploit systems that check for a face but not for biological liveness signals.
Injection attacks: bypassing the camera entirely
Injection attacks do not involve the camera at all. The attacker intercepts the data stream between the device camera and the verification system, substituting a pre-recorded or synthetically generated video feed. Liveness prompts that rely on user interaction, such as a blink, smile, or head turn, are defeated by a video loop cut to match each instruction. Purely software-based injection attacks require no physical hardware and are invisible to red-green-blue-based Presentation Attack Detection (PAD) systems. Gartner’s 2024 analysis recorded a 200% rise in injection attacks in 2023, driven by the growing availability of deepfake video generation tools. Age verification systems without injection attack detection are structurally blind to this vector.
What does a deepfake-resistant age verification system look like?
Deepfake-resistant age verification requires controls at three separate layers. The first is the biometric capture stage. The second is document forensics. The third is the signal integration stage that combines both outputs into a single verdict. No single technology addresses all three layers. The certification that most directly tests resistance to the current generation of synthetic media attacks is the ISO/IEC 30107-3 Presentation Attack Detection standard, which underlies iBeta Level 1, Level 2, and Level 3 testing.
Passive and active liveness detection
Passive liveness checks analyse biological signals during a normal selfie capture without asking the user to take any action. The model looks for three-dimensional depth, skin texture micro-patterns, infrared reflectance, and spectral frequency artefacts that AI-generated images consistently fail to replicate. Active liveness adds a real-time challenge. The user blinks, turns their head, or reads a randomised string. That combination defeats both static presentation attacks and pre-recorded video replays. Passive liveness handles most age verification flows without adding friction; active liveness is the escalation path for higher-risk sessions or ambiguous signals. For a closer look at the specific techniques fraudsters use to defeat individual controls, see how scammers bypass face verification.
Document forensics beyond field validation
Document deepfake detection goes beyond text extraction. Forensic AI models analyse the document’s visual security features, including hologram placement, micro-printing integrity, colour gradient accuracy, and the presence of printer artefacts invisible to the human eye but detectable through trained classification models. An AI-generated passport may pass OCR field validation because the date of birth is correctly formatted, but it fails substrate analysis because the security features are absent or geometrically inconsistent. As of July 2025, UK Online Safety Act obligations require age-gated platforms to go well beyond a simple document scan, with Ofcom empowered to impose fines of up to 10% of qualifying worldwide revenue for non-compliance.
Shufti’s approach to deepfake-resistant age verification
Shufti’s age verification and deepfake detection capabilities run on a proprietary multi-layer stack that addresses both the presentation and injection attack classes described above.
The liveness engine covers 56 anti-spoofing attack vectors, combining passive and active modes with three-dimensional depth analysis and frequency-domain artefact detection. These controls directly address GAN-aged selfies and video replay attacks at the biometric capture stage. Document forensic analysis goes beyond OCR to examine substrate integrity, hologram placement, and micro-printing patterns, catching AI-generated identity documents that pass text field validation.
The full stack holds iBeta Level 1, Level 2, and Level 3 certification under ISO/IEC 30107-3, the standard that specifically tests resistance to artefacts including three-dimensional masks and deepfake video. Shufti also received Department of Homeland Security (DHS) RIVR 2025 top performer status, an independent government validation rather than a vendor self-assessment, and operates at a false acceptance rate below 0.001 across diverse demographic groups.
For platforms operating under the UK Online Safety Act’s highly effective age assurance standard or equivalent regional obligations, the combination of biometric liveness and document forensics produces a verification event with an auditable evidence trail at each stage.
Deepfake attacks on age verification, from GAN-generated selfies to synthetic identity documents and injection-based video substitution, are reaching live verification queues now, and systems that rely on document scanning alone cannot detect them. Shufti’s deepfake detection covers 56 anti-spoofing attack vectors with iBeta Level 2-certified liveness and document forensic analysis, so age-gated platforms can confirm genuine biological presence before granting access. Book a demo to run a deepfake sample through the age verification pipeline and see the detection result.
Frequently Asked Questions
Can deepfakes fool age verification systems?
Basic systems relying on OCR or simple photo checks are vulnerable. AI-generated selfies and synthetic identity documents can bypass age gates that lack multi-layer liveness detection and document forensic analysis.
What is a presentation attack in age verification?
A presentation attack is any attempt to spoof a biometric sensor using a non-live artefact, including printed photographs, screens displaying another face, three-dimensional masks, or AI-generated images presented to the verification camera.
What is iBeta Level 2 certification and how does it address deepfakes?
iBeta Level 2, tested under ISO/IEC 30107-3, assesses resistance to advanced artefacts including three-dimensional masks and deepfake video, going beyond Level 1's basic photo and screen display tests.
What is passive vs active liveness detection?
Passive liveness silently analyses depth, texture, and spectral signals during normal selfie capture. Active liveness requires the user to perform a real-time gesture to confirm physical presence.
How do synthetic IDs get used to bypass age verification?
Fraudsters combine AI-generated document images with correctly formatted personal data. The document passes OCR field validation because the text is accurate, but fails document forensic analysis because security features like holograms and micro-printing are absent or geometrically inconsistent. CMS Note: FAQPage schema markup required.