Difference Between Deepfake Presentation and Injection Attacks

When FinCEN issued a formal alert in November 2024 warning that financial institutions were filing rising numbers of suspicious activity reports tied to deepfake media used to bypass identity checks, it marked a shift from theoretical risk to documented, recurring fraud pattern. The question compliance and fraud teams now face is not whether these attacks will reach their onboarding flows, but whether their current verification stack can detect both categories.
This piece covers how deepfake presentation attacks and injection attacks work, why they require different detection layers, and what a defence capable of stopping both actually looks like.
What are Deepfake Presentation Attacks?
A presentation attack happens at the sensor level. The attacker presents false biometric material directly to the camera, physically or digitally, and the capture device sees it as it would any other input. Early versions involved printed photographs or video replays on a screen. Modern presentation attacks use AI-generated deepfake video streamed live in front of the lens, real-time face-swap software applied over a live camera feed, or high-fidelity masks designed to defeat depth and texture analysis.
The international testing standard for this category, ISO/IEC 30107-3:2023, defines how biometric systems should be evaluated against known attack instruments and classifies presentation attacks by the physical media and technique used. Systems tested against this standard must demonstrate measurable resistance to these attack instruments across defined scenarios.
Presentation attack detection (PAD) analyses what the camera actually sees, checking skin texture, depth cues, light reflections, and micro-movements that distinguish a live face from a replayed one. Passive liveness checks do this without requiring any user gesture, running the analysis silently on the captured frames.
How Injection Attacks Differ from Presentation Attacks?
Injection attacks do not interact with the camera at all. Instead of fooling the sensor, the attacker bypasses it entirely by inserting fabricated data into the software pipeline between the capture device and the verification engine. A virtual camera driver, a compromised API call, or a manipulated data stream feeds a synthetic image or pre-recorded deepfake video directly into the identity verification system as though it originated from a legitimate camera session.
This distinction carries a practical consequence that has emerged clearly in the industry over the past two years. Standard PAD mechanisms are built to analyse what the camera captures. When the camera is bypassed entirely, those mechanisms receive data that looks, to them, like a genuine camera feed. The injection has already happened upstream. The PAD check inspects the injected data and, in many cases, passes it.
Injection attacks are also easier to industrialise than presentation attacks. A presentation attack requires physical setup for each attempt. An injection attack, once the tooling is established, can be scripted and repeated at volume. According to Deloitte’s Center for Financial Services, gen-AI-enabled fraud losses in the US could reach $40 billion by 2027, up from $12.3 billion in 2023. That trajectory reflects the scalability of AI-assisted attacks, injection methods included.
The industries facing concentrated exposure are financial services, crypto exchanges, and any platform running remote onboarding at volume. They process high-value transactions, operate under strong identity verification obligations, and rely on remote digital flows for their entire customer acquisition model.
How Are Standards and Regulations Responding?
The identity verification industry now has separate standards frameworks for each attack category, and regulators are starting to reference both.
For presentation attacks, the PAD testing standard ISO/IEC 30107-3:2023 remains the controlling framework. It defines the testing methodology, sets out what constitutes a presentation attack instrument (PAI), and specifies how detection rates should be measured and reported. Vendor certifications against this standard, such as iBeta Level 1 and Level 2, provide third-party validation of PAD effectiveness across a defined set of attack types.
For injection attacks, the European Committee for Standardization published CEN/TS 18099 in 2024, the first formal technical specification dedicated to injection attack detection testing. It covers both the delivery pathway, known as the Injection Attack Method, and the synthetic media content itself, known as the Injection Attack Instrument. Regulators including ENISA, France’s ANSSI, and Germany’s BSI have all flagged injection attacks as an emerging identity fraud threat, and CEN/TS 18099 gives evaluators a concrete framework for testing whether biometric systems hold up against them.
The FinCEN alert of November 2024 is notable because it does not distinguish between attack types. It asks financial institutions to file SARs when deepfake media is detected during customer due diligence, regardless of the delivery mechanism. That positions both presentation attacks and injection attacks within existing BSA/AML reporting obligations.
Defending Against Both Attack Types
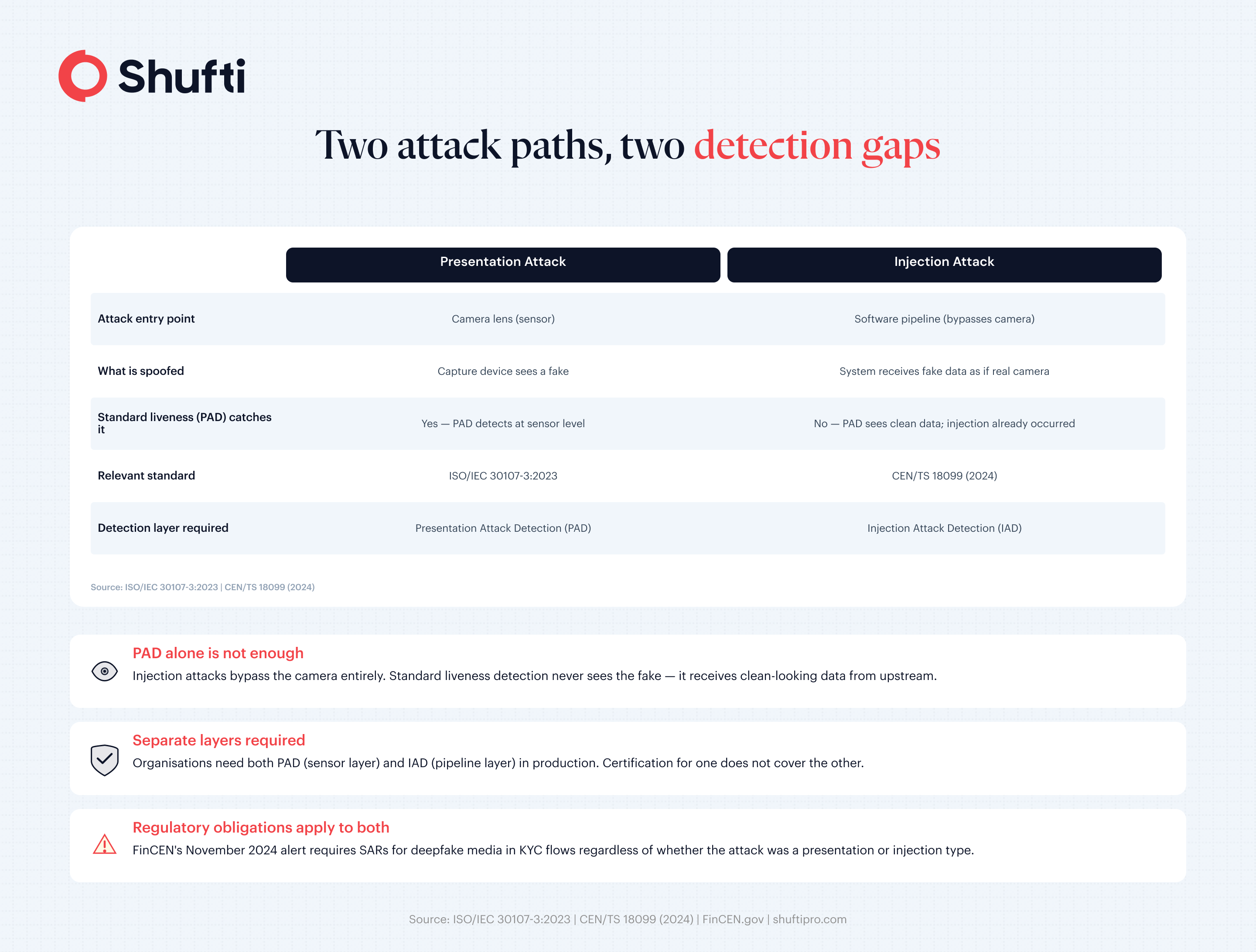
The two attack categories require separate detection layers, and neither substitutes for the other.
PAD handles the sensor layer. It analyses captured biometric data for signs that the input is not a live human face, including texture inconsistencies, frequency-domain artefacts that deepfake generation models introduce, and depth patterns inconsistent with a real three-dimensional face. Systems with certified PAD performance, tested to ISO/IEC 30107-3, demonstrate measurable resistance across the documented presentation attack types.
Injection attack detection (IAD) handles the pipeline layer. It checks the integrity of the data stream before the verification engine processes it, looking for signals that the input did not originate from the expected capture device in the expected way. Effective IAD looks at factors including the technical metadata of the incoming stream, indicators of virtual camera drivers, and consistency checks between the declared device context and what is actually observed.
For organisations running remote identity verification across high onboarding volumes, the practical question is whether the verification solution they use has both layers in production and whether either has been independently tested. A PAD certification alone does not address injection attacks. An IAD capability that has not been tested against a defined instrument set provides less assurance than one that has been evaluated against CEN/TS 18099.
The operational implication for compliance and fraud teams is that the fraud prevention stack needs to cover both the camera-facing and pipeline-facing attack surfaces. A face verification solution built only on liveness certification leaves the injection pathway unaddressed.
Organisations building or reviewing their deepfake detection capability should ask vendors to demonstrate their IAD approach, not just their PAD certification, and to specify whether their injection detection has been evaluated against CEN/TS 18099 or an equivalent framework.
Final Thoughts: Stay Ahead of Deepfake-Driven Threats
When an injection attack clears a standard PAD check, the breach leaves no liveness alert, only downstream fraud and account loss that compliance teams discover far too late. Shufti’s face verification covers 56+ anti-spoofing attack vectors, including both sensor-level presentation attacks and pipeline-level injection attacks, with performance independently validated at DHS RIVR 2025. Request a demo to see both detection layers applied to your own verification flow.
Frequently Asked Questions
How are injection attacks different from presentation attacks?
Presentation attacks fool the camera directly by showing it a fake face. Injection attacks bypass the camera entirely and feed fabricated data into the verification system further down the software pipeline, which is why standard liveness detection does not catch them.
Are deepfake presentation and injection attacks increasing?
Yes. The US FinCEN issued a formal alert in November 2024 documenting rising SAR filings tied to deepfake media used in identity fraud, and Deloitte projects gen-AI-enabled fraud losses in the US will reach $40 billion by 2027.
How do deepfake injection attacks bypass liveness detection?
Injection attacks insert synthetic media upstream of the liveness check, so the PAD system receives data that looks like a legitimate camera feed and passes it. Detection requires a dedicated pipeline integrity layer that operates before the liveness check, not PAD alone.
What is ISO/IEC 30107-3 and how does it relate to presentation attacks?
ISO/IEC 30107-3:2023 is the international standard for biometric presentation attack detection testing. It defines attack categories, testing methodology, and how detection rates are measured and reported. Third-party certifications against this standard, such as iBeta Level 1 and Level 2, validate PAD performance.
What industries are most at risk from deepfake presentation and injection attacks?
Financial services, crypto exchanges, and any platform that runs remote onboarding and depends on digital acquisition face the highest exposure because they handle high-value transactions, carry strong identity verification obligations, and rely entirely on digital flows to verify customers.