Blog, Reg Tech
How does CDD effectively help with AML Compliance?
CDD or customer due diligence in the banking sector and other financial firms is an important asp...
 Explore More
Explore More
Blog
AML Screening for Luxury Items Industry – The Role of Shufti in Ensuring Compliance
Money laundering is a global issue, and with emerging technologies, criminals are also using more...
 Explore More
Explore More
Blog
How can you prepare for AML Compliance – Ultimate AML Guidelines For Starters
Anti Money Laundering Compliance, commonly known as AML Compliance, is something that banks and f...
 Explore More
Explore More
Blog
Top 4 Reasons that will Increase Money Laundering Risks in 2022
Unlike other frauds, like like tax evasion, drug trafficking, extortion, and misappropriation of ...
 Explore More
Explore More
Blog
Identity Verification with Liveness Detection: The Key to Preventing Spoofing Attacks
Spoofing attacks are not limited to just emails and fake websites. Hackers and cybercriminals hav...
 Explore More
Explore More
Blog, Reg Tech
3 Reasons why RegTech is the Future of Innovation?
Regulatory Technologies, commonly referred to as RegTech, is an innovative use case of Financial ...
 Explore More
Explore More
Blog
E-Signature Verification | Why Businesses Should Consider Adopting It
Physical paperwork is a thing of the past now. It is a time and labour-intensive task that requir...
 Explore More
Explore More
Blog
5 Ways Facial Biometric Technology Elevates Customer Retention
Today, biometric technology is known for its ease of use and reliability. Facial biometrics have ...
 Explore More
Explore More
Blog
Synthetic Identity Fraud: Fake Identities for Criminal Activity
An increase in financial crime has been predicted by economic downturns during the previous two d...
 Explore More
Explore More
Blog
International Tax Body to curb Cryptocurrency based Tax Evasion
Tax enforcement authorities from Australia, Canada, the Netherlands, the United Kingdom and the U...
 Explore More
Explore More
Blog
KYC | How to perform KYC verification in three simple steps
Know Your Customer (KYC) is an identity verification process that plays a critical role in the pr...
 Explore More
Explore More
Blog
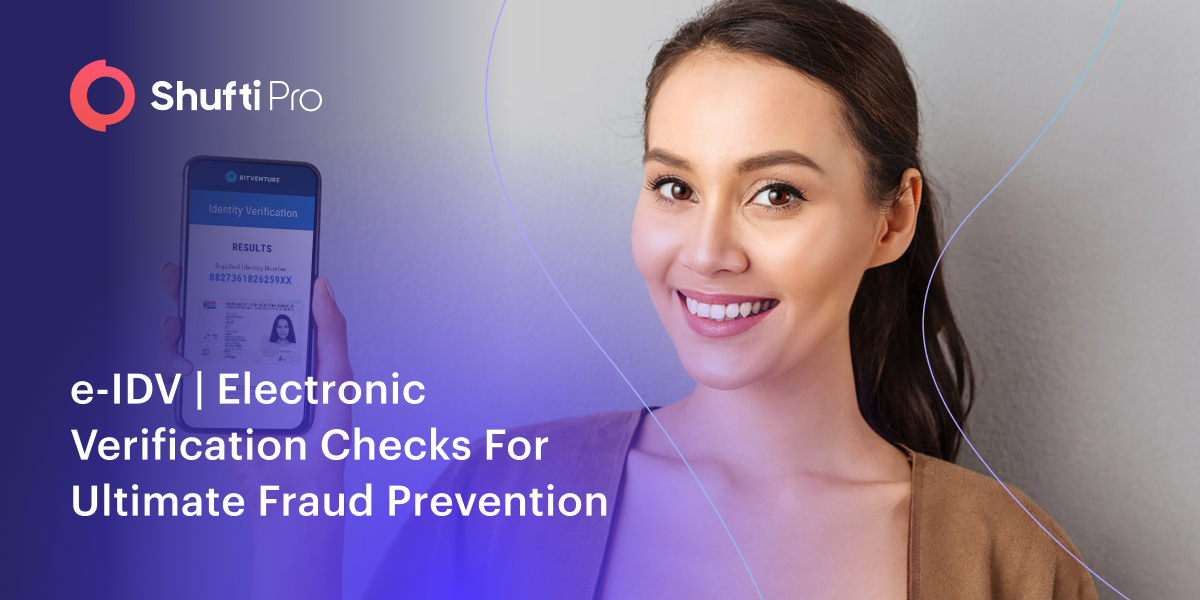
e-IDV | Electronic Verification Checks For Ultimate Fraud Prevention
The first paper-based photo identity document was in May 1876, developed by William Notman for th...
 Explore More
Explore More
Blog
Impact of COVID-19 on disruptive Fintech industry
The economy and society worldwide are affected by the corona crisis. The effects of COVID-19 on b...
 Explore More
Explore More
Anti Money Laundering, Blog, Reg Tech
RegTech facilitates effortless AML Compliance
The latest report by Research and Markets states that RegTech industry is expected to grow...
 Explore More
Explore More
Blog
CCPA: A Real Roller Coaster for Business Entities
One huge change in 2020 is the new data privacy law called the California Consumer Privacy Act or...
 Explore More
Explore More
Blog
On-Premises Identity Verification – A Solution to Prevent Data Breaches
From virtual modes of communication to digitised solutions for operating efficiently, the perks o...
 Explore More
Explore More
Blog
Establishing a KYC/AML Compliance Regime for the FinTech Sector
Today, more than 60% of the financial institutions in the market consider Fintech startups to be ...
 Explore More
Explore More
Blog
The Role of KYC Protocols in Safeguarding the Future of Cryptocurrency
Despite volatility in the crypto sector, millions of individuals access their services worldwide....
 Explore More
Explore More
Blog
7 Fascinating Facts about Face Verification Technology
Technology is a fundamental part of our day-to-day lives, from checking the weather and connectin...
 Explore More
Explore More
Blog
Avoid Non-Compliance Fines with AML Transaction Monitoring
Cybercriminals in the realm of fraud and financial crime are constantly revising exploitation met...
 Explore More
Explore More
Blog, Identity & KYC
KYC and AML Compliance can help cryptocurrencies to earn legitimacy
Cryptocurrencies are currently limited in use by virtual currency enthusiasts or by lottery bidde...
 Explore More
Explore More
Blog
Top 5 Non-banking Industries in the Crosshairs of Financial Criminals
The first half of 2021 saw significant disruption in the financial world as traditional criminal ...
 Explore More
Explore More
Blog, Online Marketplace
How API-based Technologies Can Transform the Future of Online Marketplace
API Based Technologies: Application Programming Interfaces (APIs) are giving advanced ways of dig...
 Explore More
Explore More
Blog
Top 5 Cryptocurrency Trends to Look Out for in 2023
2022 has been one of the most turbulent years for the cryptocurrency sector. For starters, Bitcoi...
 Explore More
Explore More
Blog
A Comprehensive Guide to AML Compliance [2020]
Anti-money laundering (AML) laws are the primary target of regulatory authorities. These regimes ...
![A Comprehensive Guide to AML Compliance [2020] A Comprehensive Guide to AML Compliance [2020]](https://shuftipro.com/wp-content/uploads/AML-Compliance-2.jpg) Explore More
Explore More
Blog
Fintech 2021: KYC/AML Bringing New Innovation to the Table
2020 was all about surviving the pandemic, but it has also kickstarted a new wave of innovation. ...
 Explore More
Explore More
Blog
GDPR Checklist – Practices to adopt as Business Norms
It’s been a little over eight months since the GDPR came into effect on 25 May 2018. From that po...
 Explore More
Explore More
Blog
A Guide to Understanding KYC in Banking
2022 has witnessed a rise in the number of fraudulent cases by 18% compared to 2021, damaging bus...
 Explore More
Explore More
Artificial Intelligence, Blog
How Augmented Intelligence is next stop in ID Verification Services?
Augmented intelligence (AI), also referred to as intelligence augmentation (IA) and cognitive aug...
 Explore More
Explore More
Blog, Business Technology, Online Marketplace
Asian Banks push for greater Fintech to cut down AML Compliance cost
Asian Banks are now asking their regional and national regulators to allow more fintech in order ...
 Explore More
Explore More
Blog, Online Marketplace
How AI is Transforming Fraud Prevention in the Healthcare Industry
KYC For HealthCare: Fraud is so common that there is hardly any industry that hasn’t had to bear ...
 Explore More
Explore More
Blog, Online Marketplace
What is Open Banking & Why Does it Matter in 2019?
Open banking is surely one of those trends that have the potential to change the banking and fina...
 Explore More
Explore More
Blog
A Brief Insight into the AML and CFT Framework of Thailand
Thailand has become quite a popular and well-reputed financial hub, attracting investors worldwid...
 Explore More
Explore More
Blog
A Deep Dive into Know Your Business Verification
Customer verification is essential for all businesses to onboard legitimate customers, but what a...
 Explore More
Explore More
Blog
KYC Trends To Watch Out For In 2024
Within the last year, there has been significant transformation in the global identity verificati...
 Explore More
Explore More
Blog
Strategic KYC/AML Checks for the Financial Industry – Staying a Step Ahead of Fraudsters
In recent times, the financial industry has witnessed significant technological changes which hav...
 Explore More
Explore More
Blog
5 Ways How AI Is Uprooting Recruitment Industry
Artificial Intelligence is strengthening its position in many industries and the recruitment indu...
 Explore More
Explore More
Blog
KYC | How to perform KYC verification in three simple steps
Know Your Customer (KYC) is an identity verification process that plays a critical role in the pr...
 Explore More
Explore More
Blog
The EU’s New AML Proposal, What’s in Store?
To strengthen the EU’s Anti-Money Laundering and Countering the Financing of Terrorism (AML/CFT) ...
 Explore More
Explore More
Blog
5 Reasons to Invest in Intelligent Character Recognition Services
Businesses deal with a plethora of documents, ranging from accounting and finance to sales and ma...
 Explore More
Explore More
Blog
Know Your Investor (KYI) – Onboarding the Right Investors for Your Business
In today’s tech-driven world, financial operations are being transformed by emerging digital solu...
 Explore More
Explore More
Blog
Money Laundering in the Real Estate Sector – How Shufti’s AML Services Help
Purchasing luxurious mansions is always an attractive way for money launderers to legitimize thei...
 Explore More
Explore More
Blog
5 Types of ID Fraud Skyrocketed in the First Half of 2021 – Shufti
Last year, Shufti’s AI-powered identity verification system captured a 3.36% increase in iden...
 Explore More
Explore More
Blog
Combating Identity Theft in On-Demand Services with Shufti’s KYC Solution
Transition is the only thing that is inevitable in the universe. Every passing day is changing ou...
 Explore More
Explore More
Blog
CCPA: A Real Roller Coaster for Business Entities
One huge change in 2020 is the new data privacy law called the California Consumer Privacy Act or...
 Explore More
Explore More
Blog
Know Your Investor | Sophisticated Investor Verification in Real-Time
In today’s data-driven digital world, organized crime groups and fraudsters have developed more s...
 Explore More
Explore More
Blog
AI face recognition for total automation
Face recognition is everywhere but still we’re unable to say goodbye to document, maybe because w...
 Explore More
Explore More
Blog
The Digital Black Market for Identity Data
The collection, purchase, or trade of customer data is big business. Unless organizations and ind...
 Explore More
Explore More
Blog
AML Screening | Fighting the War Against Terrorist Financing & Money Laundering
Money laundering and terrorist financing have become a global concern. In the US alone, approxima...
 Explore More
Explore More
Anti Money Laundering, Blog, Business Technology, Financial Crime / AML, Identity & KYC
Global Economies are joining forces with FATF against money laundering
Financial Action Task Force (FATF) has been very keen on eliminating financial crime (money laund...
 Explore More
Explore More
Blog, Financial Crime / AML, Identity & KYC
Fighting Financial Crime: Why KYC and AML Compliance Is Essential for the Global Finance Sector
Banks and other financial institutions are often the first line of defense against financial crim...
 Explore More
Explore More
Blog
Forensic Document Verification Solutions – A Key Step in Eliminating Identity Fraud
With emerging technologies, the demand for online services and products is skyrocketing, raising ...
 Explore More
Explore More
Blog
All You Need to Know About Facial Recognition
Rapid digitisation over the past few years has led to the adoption of facial recognition for many...
 Explore More
Explore More
Blog
4 Ways How Technology Can Simplify KYC and AML Workflow Management
While the terms AML and KYC are used interchangeably, there is a huge difference between the two....
 Explore More
Explore More
Blog
Shufti’s AML Screening Solution – How to Comply with Germany’s AML Regulations
The stability of the global economy is at risk pertaining to the rapidly growing issues of money ...
 Explore More
Explore More
Blog
Shufti’s ID Fraud Report: Reviewing 2022 and a Preview of 2023
Twenty years back, “identity theft” was imagined as pictures of shady figures rifling through gar...
 Explore More
Explore More
Blog
Hazards of Ransomware are real for Cryptocurrency Miners
Cryptocurrency may well be the future of economic landscape and it has the potential of taking th...
 Explore More
Explore More
Blog, Online Marketplace
KYC for Financial Institutions
E-KYC for Financial Institutions
Imagine you’re the owner of a brokerage firm. You’re not exactly...
 Explore More
Explore More
Blog
KYC & AML Regulations in the UK: An Ultimate Guide
Financial crimes have been around since the invention of money. Some argue that their origins are...
 Explore More
Explore More
Blog
Intelligent Security Systems & Digital ID Verification
Most technology solutions present a compromise between convenience and security to their users. I...
 Explore More
Explore More
Blog
UK Watchdogs Hit Financial Institutions with Record AML Fines in 2021
A dramatic increase in Anti-Money Laundering (AML) fines was seen in 2021 as financial watchdogs ...
 Explore More
Explore More
Blog
Crypto Regulations in the US and UK | A Comprehensive Overview
Financial regulators struggle to understand how to categorise and regulate cryptocurrency that do...
 Explore More
Explore More
Blog
Top 10 Real-World Scenarios Where Shufti’s IDV Can Help
Whether you’re an e-commerce store that needs to verify delivery addresses or a bank that has to ...
 Explore More
Explore More
Blog
Combating 8 Prevalent Biometric Fraud Through a Single AI Solution
Considering how criminals are attempting new strategies to “steal a face”, companies are no longe...
 Explore More
Explore More
Blog
AML Screening for Online Gambling Platforms – Placing the Bets on Regulatory Compliance
With technology evolving every day, online gambling is one of the sectors that has revolutionized...
 Explore More
Explore More
Blog, Identity & KYC, Online Marketplace
Importance of Identity Proofing for Facebook & Social Media
For years, social media has been used as a tool for increased connectivity. Both businesses, as w...
 Explore More
Explore More
Artificial Intelligence, Blog, Fraud Prevention
The Role of Artificial Intelligence in the Future Of Financial Fraud Detection
Until a few years ago Artificial Intelligence seemed like a thing from sci-fi movies. The whole c...
 Explore More
Explore More
Blog
E-Signature | Digitise and Verify Agreements in Compliance
The use of electronic signature, or e-signature, has transformed business dealings. The days of s...
 Explore More
Explore More
Blog
Understanding Risk Assessment in the Gambling Sector – 2025 Edition
Online gambling revenue is on track to exceed $150 billion globally by 2025, with Europe alone ge...
 Explore More
Explore More
Blog
Know Your Investor | Simplify the Onboarding Process
Businesses at any stage need to onboard credible partners and investors who bring in capital and ...
 Explore More
Explore More
Blog
The Expected No-Deal Brexit and AML/CFT Laws in the UK
The current prime minister of the UK Mr. Boris Johnson made a statement that the UK should be rea...
 Explore More
Explore More
Blog
Facial Recognition: A Technology for Online Businesses to Prevent Fraud
Today, biometric technology has traditionally established itself and has become an integral part ...
 Explore More
Explore More




























![A Comprehensive Guide to AML Compliance [2020] A Comprehensive Guide to AML Compliance [2020]](https://shuftipro.com/wp-content/uploads/AML-Compliance-2.jpg)