What Is Identity Assurance? Levels, Frameworks & Requirements Explained (2026)

- 01 Identity Assurance vs Identity Verification vs Authentication
- 02 IAL1, IAL2, and IAL3: NIST Identity Assurance Levels Explained
- 03 eIDAS Levels of Assurance: Low, Substantial, and High
- 04 UK DIATF: Identity Assurance in the British Market (2026)
- 05 Which Identity Assurance Level Does Your Business Need?
- 06 What Evidence Is Required to Achieve Identity Assurance Level 2?
- 07 Identity Proofing vs Identity Assurance
Identity assurance is among the leading causes of fraud in digital onboarding, as per the UK Department for Science, Innovation, and Technology. And despite that, many compliance teams and experts still don’t focus on it enough and treat it as if it’s something similar to a basic ID check.
Identity assurance is the degree of confidence that a claimed digital identity actually belongs to the person presenting it. It includes covering everything from how teams collect and verify evidence to ensure they comply with the necessary regulations. Doesn’t matter if it’s during onboarding new customers under the NIST SP 800-63 or the UK Digital Identity and Attributes Trust Framework (DIATF), the assurance level should be high because that’s what will determine where you stand when it comes to complying with regulations and safeguarding against fraud.
Identity Assurance vs Identity Verification vs Authentication
People often use these three terms in place of each other, but they serve different functions:
Identity verification is the process of checking whether an identity document or biometric is genuine.
Identity assurance is a more comprehensive term that covers how strong the entire proofing process is. It includes what evidence was collected during the process, how compliance and relevant teams validated it, and how reliably it can be trusted over time.
Authentication refers to the process that comes after proofing. It confirms the same verified individual is returning to a session, not that their identity was correctly established in the first place.
Knowing the difference between these three matters, especially for businesses that are regulated, because, let’s say, a financial institution achieves strong customer authentication, but has weak proofing at the start, it won’t be able to satisfy the auditors and regulators.
IAL1, IAL2, and IAL3: NIST Identity Assurance Levels Explained
The NIST Digital Identity Guidelines (SP 800-63A) define three Identity Assurance Levels (IALs). These are the global benchmark for how rigorously an identity has been proofed:
|
Level |
What It Means |
Typical Use Case |
|
IAL1 |
Self-asserted identity only. No verification of real-world existence required. |
Low-risk accounts, newsletter sign-ups, social login |
|
IAL2 |
Identity must be linked to a real person using either remote or in-person proofing. Supporting documents and biometric confirmation required. |
Fintech onboarding, crypto KYC, regulated lending, insurance |
|
IAL3 |
In-person proofing with trained personnel required. Physical or supervised biometric binding. Highest fraud resistance. |
Government benefits, national ID issuance, high-value banking |
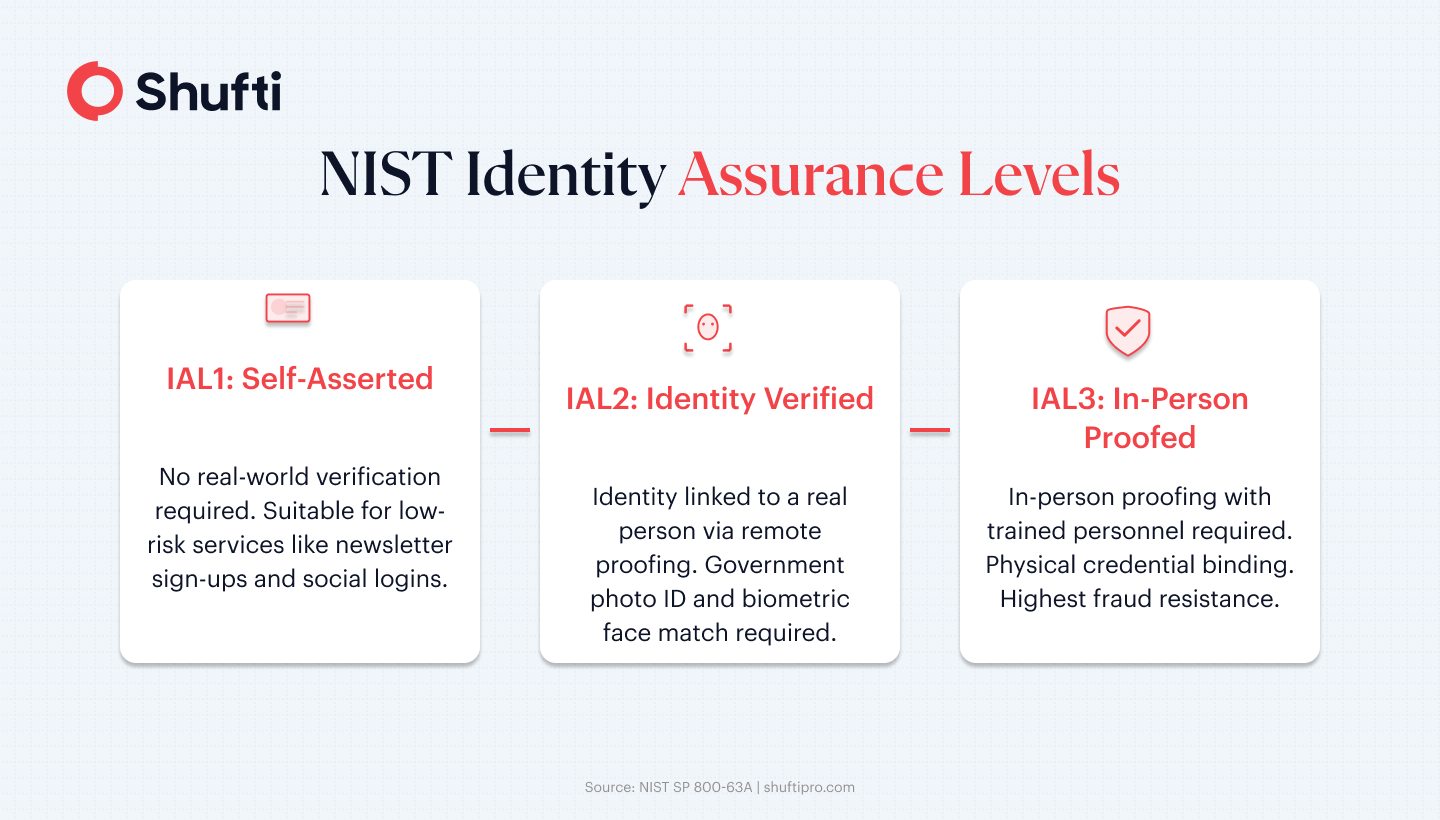
In our observation, most of the financial services typically achieve IAL2. To reach that level, your business or organization must have a reliable way to perform document verification, biometric face matching, and liveness detection when needed.
eIDAS Levels of Assurance: Low, Substantial, and High
The eIDAS Regulation (EU 910/2014) and its revised eIDAS 2.0 framework provide three levels of assurance that you can use as a reference for electronic identification across all of the EU member states:
- Low: This has the minimal risk of identity misuse and is suitable for most of the basic digital services.
- Substantial: This one significantly reduces the risk of your customer’s identity being misused. It also requires a series of multi-factor authentication with verified credentials.
- High: It’s the strongest level of assurance, and Identity is typically bound to a physical or cryptographic credential that is verified in-person or via equivalent methods that are pre-approved. It’s usually used to access high-risk public and private services.
For cross-border services operating across the EU, eIDAS Substantial or High assurance is the baseline expectation for financial services. eIDAS 2.0 extends this framework to include digital wallets, bringing identity assurance requirements directly into consumer onboarding flows.
UK DIATF: Identity Assurance in the British Market (2026)
The UK Digital Identity and Attributes Trust Framework (DIATF) was published by DIST and now it’s in the beta certification phase. It provides a certification-based approach for businesses to ensure the identity of their customer base. Here’s what it says:
- Medium confidence: Equivalent to IAL2. This would require a document and biometric check, which must be cross-checked against a single strong source.
- High confidence: Equivalent to IAL3. This would require businesses to perform multiple independent source checks. These can include factors like activity history and biometric binding.
UK businesses using certified identity service providers under the DIATF gain a legal basis to rely on those checks for right-to-work, right-to-rent, and DBS verification.
For financial services firms under Financial Conduct Authority oversight, medium confidence checks are the minimum for customer onboarding under existing AML rules.
Which Identity Assurance Level Does Your Business Need?
It totally depends on your regulatory environment, risk exposure, and the nature of the transaction:
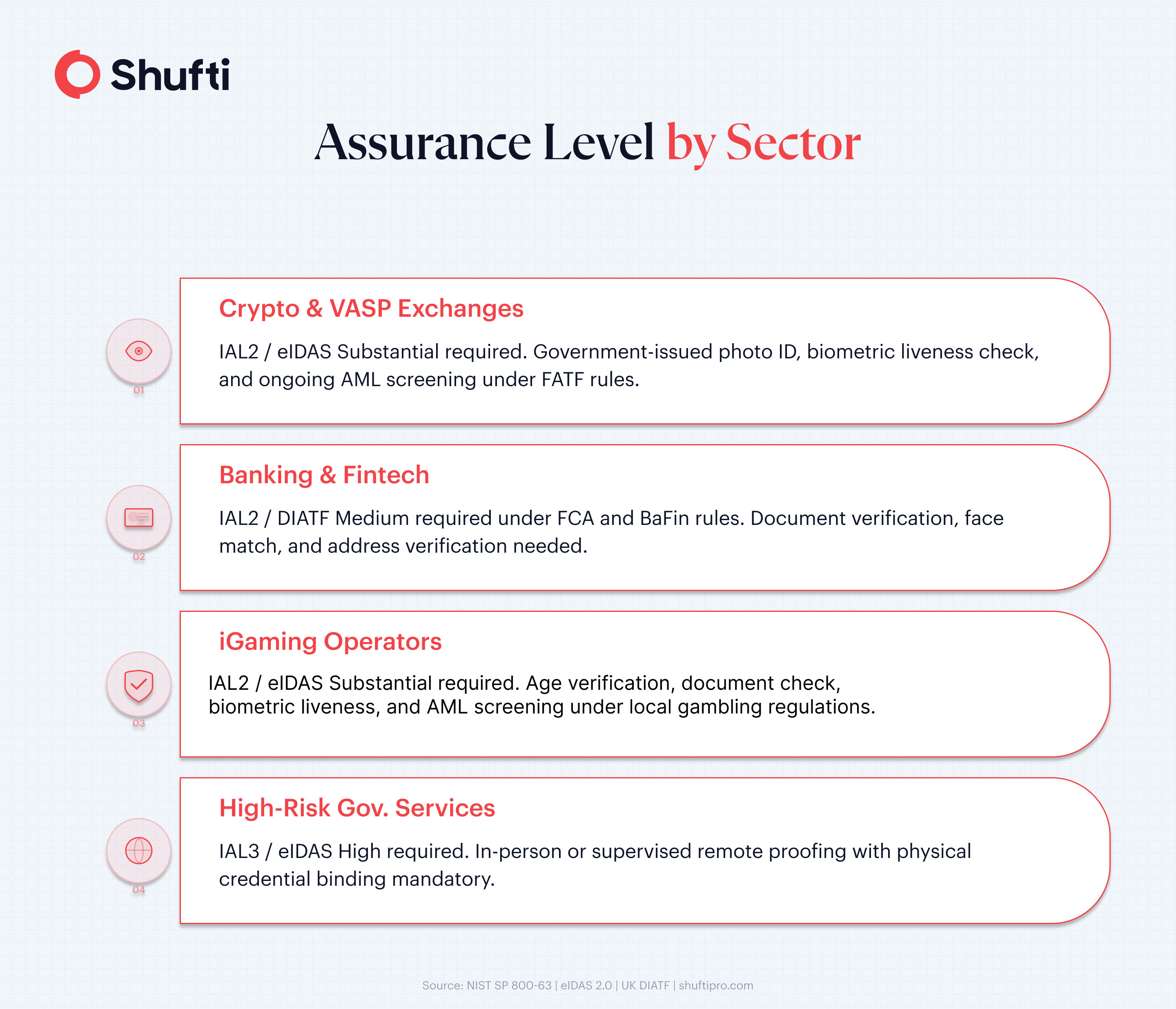
IAL2 is the main standard that most fintech, crypto, and iGaming operators need to worry about. Shufti’s document verification, face verification, and AML screening combine to deliver IAL2-equivalent assurance at scale, with full-session audit trails to satisfy regulatory review.
What Evidence Is Required to Achieve Identity Assurance Level 2?
IAL2 requires businesses to prove identities against identity evidence linked to a real person in credible, authoritative records. Under NIST SP 800-63A, this typically include:
- One piece of STRONG evidence: This is when a government-issued photo ID (passport, national ID, or driving licence) that’s also been verified for tampering is used by an organization.
- Biometric binding: This process involves taking a face match between the ID portrait and a live selfie of the customer. It should also be an ISO 30107-3-compliant liveness detection to ensure all sorts of presentation attacks are blocked.
- Address or record corroboration: This one’s optional but is highly recommended, especially for financial services, via utility bill, bank statement, or electronic record matching.
Identity Proofing vs Identity Assurance
Identity proofing is the operational side of the process that involves businesses collecting documents, running biometric checks, and screening customer identities against watchlists.
Whereas Identity assurance is the regulatory output that is the result of that process. It is the confidence level that gets assigned to that proofing process based on the quality of evidence and how rigorous the procedure was.
A business might be able to conduct a thorough proofing, but it still might only achieve a low level of assurance if it decides not to document its methodology, use approved evidence types, and retain audit logs.
That’s why the KYC platform provided by Shufti generates structured and well-organized audit trails for each of the verification your organization performs. It provides the documented evidence chain that businesses like yours can use to show regulators when they assess whether your assurance level is up to the mark or not.
If your current verification stack cannot demonstrate IAL2-equivalent assurance, it is worth reviewing before your next compliance audit. Request a demo to see how Shufti maps to NIST, eIDAS, and UK DIATF requirements.
Frequently Asked Questions
What is the difference between IAL1, IAL2, and IAL3?
IAL1 is self-asserted only. IAL2 requires government ID and biometric verification. IAL3 adds in-person proofing with physical credentials.
Is identity assurance the same as authentication?
No. Identity assurance establishes who you are at signup; authentication confirms you're returning.
What does eIDAS say about identity assurance?
eIDAS has three levels: Low, Substantial, and High. Financial services need Substantial multi-factor verification with a validated credential.
Which identity assurance level is required for crypto exchanges?
IAL2 or eIDAS Substantial: verified government ID plus biometric liveness, plus ongoing AML screening.
What is the UK Digital Identity and Attributes Trust Framework?
A UK government certification scheme with confidence levels aligned to IAL2 and IAL3, covering right-to-work, right-to-rent, and AML checks.












