Card Cloning: What it is, How it works, and How to stop it

- 01 What is Card Cloning?
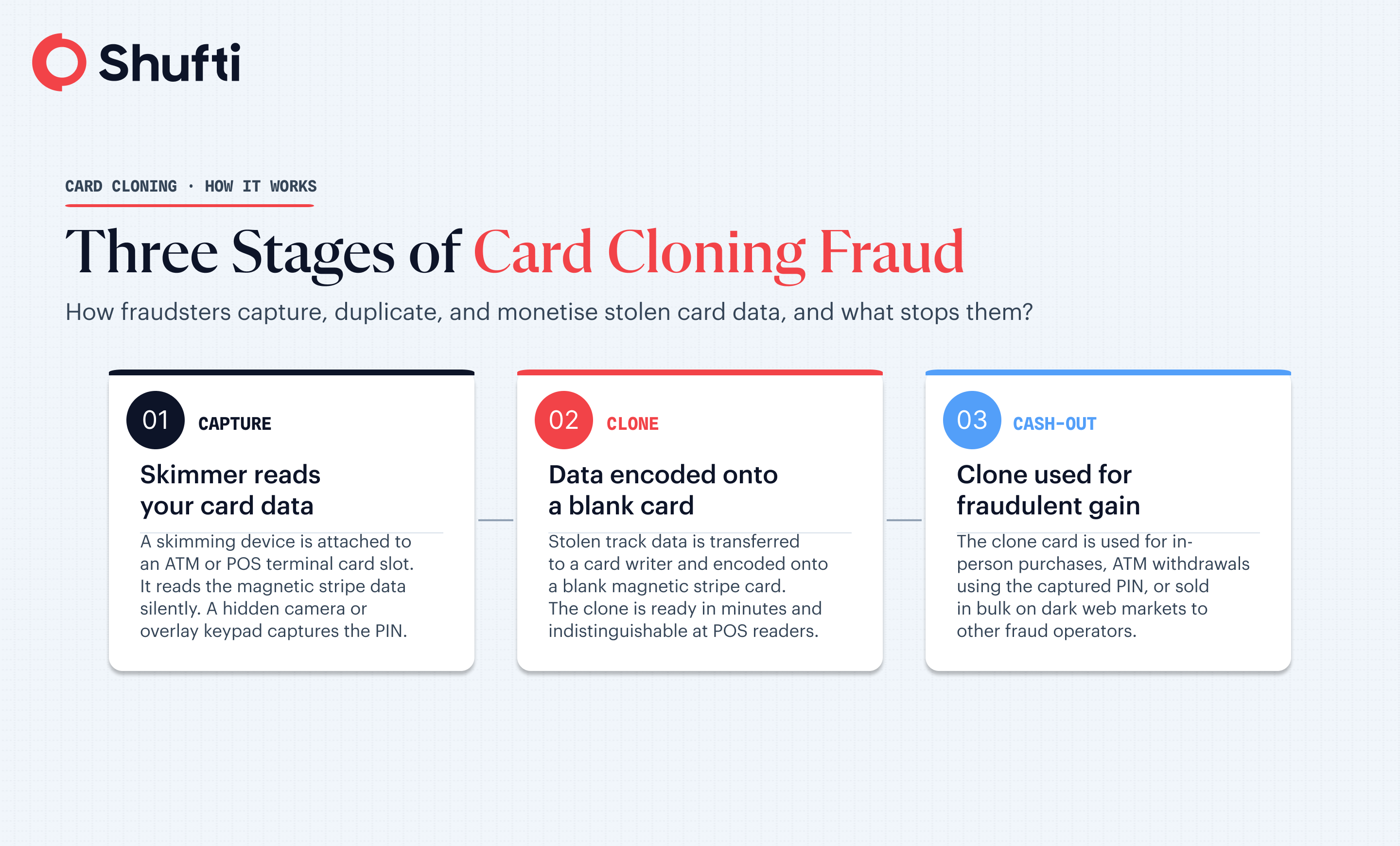
- 02 The Three-Stage Consistent Process for Card Cloning Fraud
- 03 What is the difference between card skimming and card shimming?
- 04 How can I tell if my card has been cloned?
- 05 Can cloned cards be traced?
- 06 How to Prevent Card Cloning?
- 07 How Shufti helps financial institutions catch card fraud at the source
- The payment card skimming market has grown significantly with market size escalating from 3.99 billion USD in 2025 to 4.49 billion in 2026.
- Card cloning copies your card’s magnetic stripe data onto a blank card; your physical card never needs to leave your wallet.
- Skimmers and shimmers installed at ATMs and point-of-sale terminals are the most common capture method.
- EMV chip adoption cut counterfeit card-present fraud substantially, but criminals responded by shifting to card-not-present channels.
- Cloned card transactions leave a traceable digital trail banks and law enforcement regularly track and prosecute them.
The FBI puts card skimming losses in the United States at roughly $1 billion a year. The payment card skimming market has grown significantly with market size escalating from 3.99 billion USD in 2025 to 4.49 billion in 2026 a compound annual growth rate of 12.5%. The persistence of that figure points to something important: one of the oldest card fraud methods is still very much alive. Card cloning, the process of duplicating a payment card’s data onto a blank card and using it to make fraudulent transactions, continues to cause significant losses to consumers and financial institutions, even as card security has evolved.
This article explains what card cloning means, how the cloning process works from capture to cash-out, how it differs from card shimming, and what both cardholders and institutions can do to stop it.
What is Card Cloning?
Card cloning meaning, is copying the data stored on a payment card’s magnetic stripe and writing that data onto a new, blank card. It is also called card skimming fraud or credit card cloning. The resulting clone card carries the same account information as the original and can be used wherever magnetic stripe transactions are accepted.
The key fact that makes card cloning particularly dangerous is this: your physical card never has to leave your possession. A fraudster only needs a few seconds of access to your card’s data or a device that reads it without any direct contact at all. By the time you notice anything is wrong, the clone may already have been used across multiple transactions.
The Three-Stage Consistent Process for Card Cloning Fraud
Card cloning follows a consistent three-stage process: capturing the card data, encoding it onto a blank card, and converting that card into cash or goods.
The Capture Stage
The most common method is a skimming device, a small piece of hardware attached to or placed inside a legitimate card reader at an ATM, petrol station pump, or retail terminal. When a card is inserted or swiped, the skimmer reads the magnetic stripe data and stores it. A hidden camera or false keypad overlay captures the PIN simultaneously. Some operations use social engineering instead: a fraudster poses as a merchant or service worker and manually swipes the card through a handheld skimmer.
The Cloning Stage
Once captured, the data is transferred to a card writer, a widely available piece of hardware that encodes the stolen information onto a blank white card with a fresh magnetic stripe. The resulting clone carries the same track data as the original, making it indistinguishable at point-of-sale terminals that rely on magnetic stripe reads. This step can be completed in minutes, and fraudsters operating at scale run entire batches of clone cards in a single session.
The Cash-Out Stage
Clone cards are used in three main ways. The first is in-person purchases at retailers that still accept magnetic stripe transactions, particularly in regions with lower EMV adoption. The second is ATM withdrawals, using the captured PIN alongside the cloned card. The third is resale: stolen card data is sold on dark web marketplaces, often in bulk, to other fraudsters who carry out the cash-out themselves. A single skimming device, left in place for 48 hours at a busy ATM, can yield hundreds of card records.
What is the difference between card skimming and card shimming?
Card skimming and card shimming are both card cloning methods, but they target different parts of a payment card and require different hardware.
|
Attribute |
Card skimming |
Card shimming |
|
Target |
Magnetic stripe |
EMV chip contacts |
|
Device type |
External overlay on card slot |
Thin shim inserted inside card slot |
|
Card type exploited |
Magnetic stripe cards |
Chip-and-PIN cards |
|
Detection difficulty |
Moderate device is external and sometimes visible |
High shim sits inside the terminal slot, invisible to the user |
|
Fraud output |
Full cloned mag-stripe card |
Partial chip data (used for mag-stripe fallback transactions) |
Card skimming targets the magnetic stripe and produces a fully functional clone card. Card shimming goes one step further: a paper-thin device is inserted inside the chip card slot and reads the chip’s data as it flows during a transaction. While EMV chips generate a unique transaction code each time and cannot be directly cloned for chip-on-chip use, the data captured through shimming can be used to produce a magnetic stripe clone that initiates transactions at terminals running in stripe-fallback mode. This is why the shift to chip cards reduced but did not eliminate card cloning fraud.
How can I tell if my card has been cloned?
The clearest signal is unfamiliar transactions on your statement purchases you do not recognise, in locations you have not visited, or at merchants you have never used. A more specific warning sign is geographic impossibility: your card appearing to make a transaction in a foreign city while you are demonstrably elsewhere. Some banks flag this automatically through velocity checks and location-based alerts.
Other signs include small test transactions, often under one pound or one dollar, that appear before larger withdrawals. Fraudsters frequently run a micro-charge first to confirm the clone card works before committing to a higher-value purchase. You might also notice your account balance dropping without a corresponding transaction appearing immediately in your app, a lag that can indicate a cloned card being used at a terminal that batches its settlement.
The harder reality is that many people discover their card has been cloned only after their bank contacts them, or after a transaction declines unexpectedly. Enabling real-time transaction alerts on every card you hold remains the most reliable early-warning system available to individual cardholders.
Can cloned cards be traced?
Yes. Cloned card transactions leave a digital trail that banks, card networks, and law enforcement can follow. Every transaction carries metadata terminal ID, merchant location, timestamp, and the type of card read used. When a chip-enabled card initiates a magnetic stripe transaction (a fallback read), the bank’s fraud systems flag it immediately, because it is inconsistent with that card’s normal profile.
Card networks maintain velocity and geolocation models that can identify a cloned card within hours of first use. Banks share fraud intelligence through schemes such as Visa and Mastercard’s fraud reporting programmes, allowing a card flagged in one country’s network to be blocked globally. In the United States, the Secret Service launched a nationwide crackdown on card skimming in 2025, and the FBI has successfully prosecuted organised skimming rings including a Romanian crime network that targeted ATMs across multiple US states. The enforcement trail starts with the transaction data.
How to Prevent Card Cloning?
Prevention operates at two levels: what individual cardholders can do, and what businesses and card issuers must do.
For cardholders
Inspect any card terminal before inserting your card in order to timely restrict credit card cloning.. At ATMs, look for overlays on the card slot, loose fascia panels, or cameras positioned toward the keypad. Cover your hand when entering your PIN this defeats the PIN-capture component even if a skimmer has already been installed. Use chip-and-PIN rather than magnetic stripe wherever possible, and prefer contactless for low-value transactions, since contactless does not expose the static stripe data. Set real-time transaction alerts on every card, and review your statements weekly. If your bank offers virtual card numbers for online purchases, use them as they are single-use and cannot be cloned.
For businesses and card Issuers
The single most effective institutional control is EMV enforcement: disabling magnetic stripe fallback at POS terminals removes the most accessible clone-card vector. Terminals should be physically secured, tamper-evident, and checked regularly by trained staff. Card issuers should run velocity checks, geolocation anomaly detection, and behavioral models that flag fallback transactions on chip-capable cards. Tokenization in payment processing replaces the static card number with a dynamic token for each transaction, meaning stolen data has no replay value.
How Shufti helps financial institutions catch card fraud at the source
Card fraud rarely starts at the terminal. It often starts earlier when a fraudster opens a mule account, loads cloned card details onto a new digital wallet, or attempts to register a payment instrument under a synthetic identity. By the time a cloned card is declined at an ATM, the account-level fraud has already happened upstream.
Shufti’s fraud prevention layer applies identity verification and behavioural analytics at the account-opening and onboarding stage, the point where most card fraud supply chains are assembled. Anomalous device signals, velocity patterns across registrations, and identity-document forensics catch fraudulent account creation before a cloned card ever becomes an active instrument. For institutions that need to close the gap between card issuance and card compromise, the fix starts at identity.
|
See how Shufti’s fraud prevention handles account-level card fraud on real onboarding data request a demo |
Frequently Asked Questions
Is it possible to clone a card?
Yes. Magnetic stripe cards can be cloned using widely available skimming hardware and card-writing equipment. EMV chip cards are harder to clone directly, but shimming attacks can capture partial chip data used to produce magnetic stripe fallback clones. Physical possession of your card is not required.
Can cloned cards be traced?
Yes. Every card transaction carries a terminal ID, merchant location, timestamp, and card-read type. Banks and card networks run velocity and geolocation models that flag anomalies within hours. Law enforcement, including the FBI and US Secret Service, has successfully traced and prosecuted organised cloning operations using this transaction data.
What is the difference between card cloning and card skimming?
Card skimming is the data capture method, stealing magnetic stripe information using a hidden device at an ATM or POS terminal. Card cloning is what happens next: that stolen data is written onto a blank card to create a usable duplicate. Skimming is the first step in the card cloning process.
How can I tell if my card has been cloned?
Look for unfamiliar transactions, especially small test charges under one dollar or one pound, geographic impossibilities (transactions in cities you have not visited), and unexpected balance drops. Enable real-time transaction alerts on all cards. Many cloning cases are identified by the bank and first respond immediately to any fraud alert you receive.