Digital Fraud Prevention: How Technology Is Reshaping the Fight Against Online Crime

Fraud now sits among the top five global crime threats tracked by INTERPOL, with financial fraud alone linked to an estimated $442 billion in losses in 2025 (INTERPOL Global Financial Fraud Threat Assessment). Behind that number sit bank customers who lost money to scams, online retailers hit by stolen-card chargebacks, and compliance teams watching fraud rings open accounts faster than human reviewers can close them.
Digital fraud prevention refers to the practices, controls, and technologies businesses use to detect and stop fraudulent activity across digital channels. It spans identity checks at account opening, biometric and device signals during login, and transaction monitoring after a customer is active. The discipline draws on cybersecurity, compliance, and data science, and it now looks very different from the rules-based filters of five years ago.
This guide walks through the scale of the problem today, how the attacker playbook has shifted, and what the modern digital fraud prevention stack actually looks like. The goal is practical. That means a clear-eyed view of what the technology can do, where it struggles, and how fraud teams can build defenses that hold up in 2026.
How Big Is the Digital Fraud Problem Today?
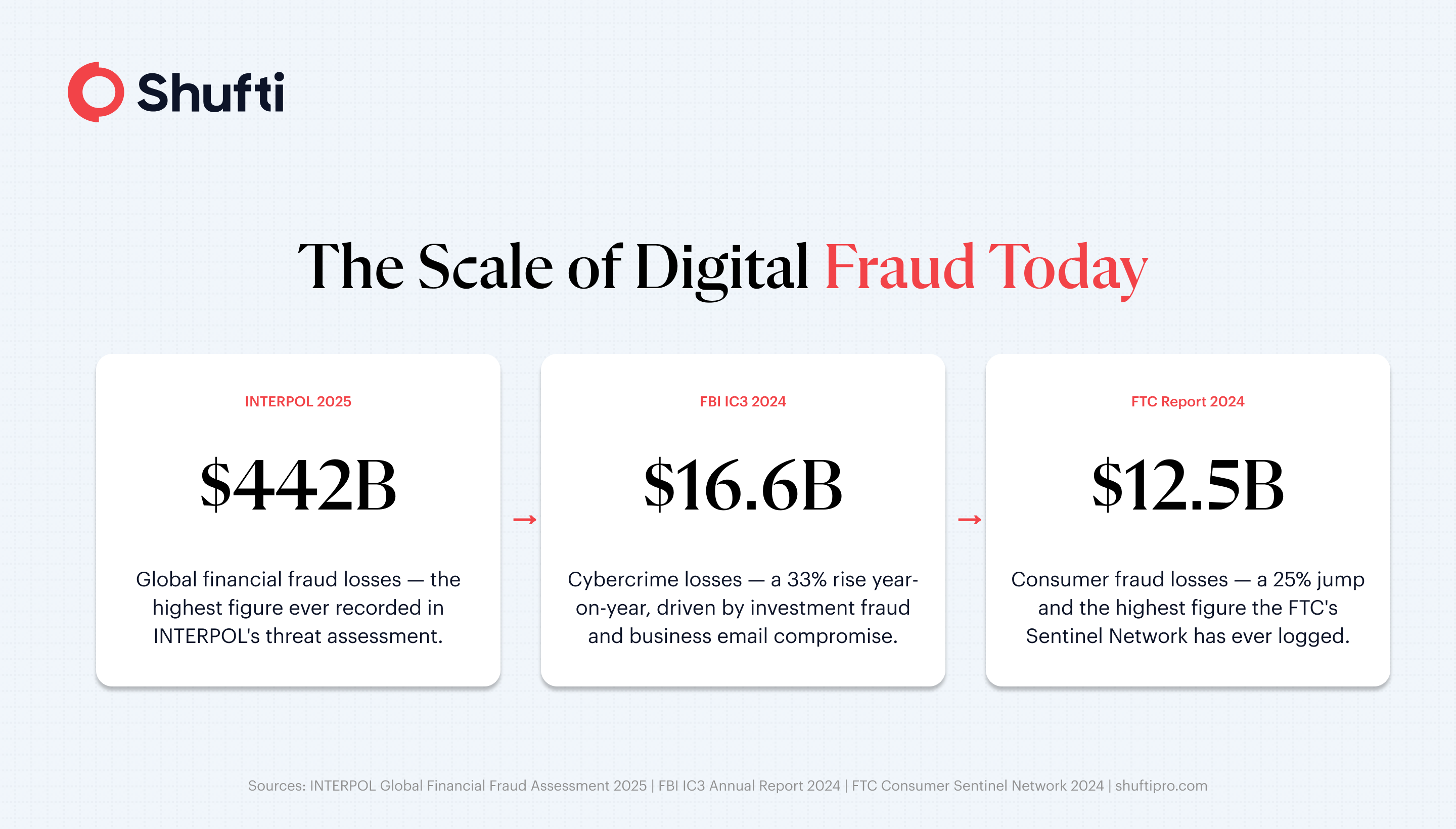
The headline numbers from government agencies tell a consistent story. US consumers reported losing $12.5 billion to fraud in 2024, a 25% jump on the prior year and the highest figure the FTC’s Consumer Sentinel Network has ever recorded. The FBI’s Internet Crime Complaint Center logged $16.6 billion in cybercrime losses over the same period, up 33% year on year, with investment fraud and business email compromise accounting for the largest share (FBI IC3 2024 Annual Report).
Europe shows the same pattern. Finance was the third most-targeted sector in the ENISA Threat Landscape 2024, with roughly 9% of observed incidents aimed at banks, payment providers, and insurers. Analysts at the European agency linked the jump to AI tools that lower the technical bar for attackers, along with fraud-as-a-service kits that sell ready-made scam infrastructure on dark-web marketplaces.
These figures matter because they frame what digital fraud prevention is up against. Fraud is no longer a niche problem handled at the edges of operations. It is a board-level cost centre, a regulatory focus, and a customer-trust issue that sits on the same dashboard as growth metrics.
How the attacker playbook has shifted
Five years ago, most online fraud prevention tools were built to catch stolen credit cards and basic phishing. The attack surface has broadened since. Fraud rings now operate like software companies, with specialised roles covering document forgery, social engineering, money mule recruitment, and cash-out logistics.
Three shifts stand out. First, synthetic identity fraud has moved from a US consumer-credit problem to a global account-opening problem, with fraudsters combining real and fabricated data to create convincing new personas. Second, generative AI has industrialised phishing, deepfake voice calls, and convincing fake documents at a scale manual reviewers cannot match. Third, account takeover attacks now chain credential stuffing, SIM swaps, and session hijacking, which means static login checks no longer carry the weight they used to.
The INTERPOL assessment notes that large language models and crypto payments have combined with phishing-as-a-service and ransomware-as-a-service business models, letting criminals run professional fraud campaigns with relatively little technical skill. Defences built for the old playbook tend to miss this. Rule lists age quickly, and every new rule risks blocking legitimate customers alongside the bad ones.
The technology stack reshaping digital fraud prevention
Modern digital fraud prevention rests on a handful of connected layers. No single tool solves fraud on its own. The point of the stack is that each layer catches something the layer before it missed, and together they produce a picture confident enough to approve, review, or decline.
AI and machine learning for pattern detection
Machine learning models now sit at the heart of most digital fraud detection tools. Unlike static rules, these models weigh hundreds of signals at once, from transaction velocity and device fingerprint to IP reputation, behavioural patterns, and session history. They score risk in real time and improve as they see more fraud, which means a well-tuned model gets sharper over months, not worse.
The trade-off is explainability. Regulators expect fraud teams to show why a customer was flagged, and black-box models make that difficult. Most practical deployments pair a machine learning engine with a rules layer that enforces hard controls such as sanctions screening, jurisdictional blocks, and velocity caps.
Biometrics, liveness, and deepfake defence
Passwords and one-time codes lost their edge as credential dumps became commodity items. Facial biometrics and fingerprint checks tie a login or a new account to a physical person, not a memorable string. Liveness detection then confirms the person is present in front of the camera, not a photo, a video replay, or a deepfake.
Deepfake injection attacks have made liveness the harder problem of the two. Attackers feed synthetic video directly into the verification stream, bypassing the camera. Current defence relies on forensic signals such as texture consistency, micro-motion, and reflection patterns, which change as generator models improve. Fraud teams should treat liveness as a capability to audit, not a checkbox to tick.
Digital identity verification as the foundation
Most fraud losses begin at account opening. If a fraudulent account never gets onboarded, the later layers have less to defend. That is why identity verification anchors the modern stack. Document checks confirm that an ID is real. Face match confirms the ID belongs to the person applying. Database lookups through KYC and eIDV checks confirm the identity exists in the relevant jurisdiction. AML screening then confirms the person is not on a sanctions or watchlist.
Done well, these checks take under a minute. Run them poorly and drop-off rates push into double digits, which makes growth teams unhappy and fraud teams defensive. The goal is not maximum friction. It is the right friction for the risk, applied at the point where a fraudster is most likely to give up.

Building an effective digital fraud prevention programme
Technology alone does not make a programme. The teams that run fraud well share a set of operational habits that the tools sit inside.
Treat the customer journey as the unit of defence. Fraud signals are thin at any single step, so the programme needs checks at account opening, at login, at sensitive actions such as password resets or beneficiary changes, and at transaction time. A strong signal at one step often cools risk at the next, which means the programme should share context across layers rather than running them in silos.
Measure false positives as seriously as fraud losses. A 0.1% fraud rate with a 3% false-positive rate punishes many more good customers than it catches bad ones, and lost-revenue costs tend to dwarf fraud savings at that ratio. Tuning reviews should happen monthly, not quarterly.
Common mistakes to avoid include relying on a single vendor layer to carry the whole programme, leaving onboarding checks static while fraud patterns move, and treating fraud data as a compliance artefact rather than a growth signal. The best programmes route reviewed cases back into the model, close the loop between fraud analysts and product owners, and use the fraud dashboard to inform underwriting, collections, and customer support.
Digital fraud prevention is not a finished problem. Attackers will keep testing the stack, and defences will keep catching up. The difference between teams that stay ahead and teams that chase losses is how deliberately they connect identity, device, behaviour, and transaction signals into one picture of each customer.
Criminals now industrialise fraud with AI, synthetic identities, and automated account-opening attacks that outrun manual review. Shufti’s fraud prevention platform combines AI-driven identity checks, biometric liveness, and document verification in a single API, so fraud signals surface before a risky account opens rather than after the first chargeback lands. Request a demo to see how the full stack handles your account-opening and transaction volumes.
Frequently Asked Questions
What is digital fraud prevention?
Digital fraud prevention is the combination of controls and technologies that detect and block fraudulent activity across online channels, covering identity, device, behaviour, and transaction signals.
How is technology changing the way businesses fight online fraud?
Rules-based filters have given way to machine learning models, biometric verification, and linked identity checks that score risk in real time across the full customer journey.
What are the most common types of digital fraud in 2026?
Synthetic identity fraud, account takeover, business email compromise, investment scams, and deepfake-enabled onboarding fraud dominate reported losses across regulator data.
How does digital identity verification help prevent fraud?
Identity verification stops fraudulent accounts at the point of creation by checking the document, matching it to a live face, and screening the person against sanctions and watchlist data.
What is the role of AI in digital fraud prevention?
AI powers the pattern-detection layer of fraud prevention systems, analyzing hundreds of behavioral, device, and transaction signals simultaneously to detect anomalies and flag potential fraud in real time.