What is AML Identity Verification and how it works

- 01 What AML identity verification actually means
- 02 The regulatory mandate: what the rules actually require
- 03 How AML identity verification works, step by step
- 04 When AML identity verification applies in the customer journey
- 05 What happens when a customer fails AML identity verification
- 06 How Shufti handles AML identity verification
Every year, an estimated 2–5% of global GDP moves through money laundering channels, anywhere from $800 billion to $2 trillion, according to the UNODC’s money laundering overview. The starting point for stopping it isn’t a watchlist check. It’s knowing, with confidence, who you’re actually dealing with. The gap between who a customer claims to be and who they actually are is precisely where financial crime takes root.
AML identity verification closes that gap. It’s not a single checkbox. It’s the process that ties a verifiable identity to a real person before any compliance decision can be made.
The problem most compliance teams face isn’t a lack of AML tools. It’s that identity verification and AML screening run through separate systems, creating reconciliation work and leaving gaps in the audit trail. Merging both into a single, sequential process is what modern AML identity verification means in practice, and what regulators now expect.
What AML identity verification actually means
AML identity verification is the process of confirming that a customer is who they claim to be, using reliable and independent sources, as part of anti-money laundering due diligence. It sits at the intersection of identity verification and AML screening: you cannot meaningfully check a person against a sanctions list if you haven’t first confirmed who that person is.
Regulators draw this distinction carefully. The FinCEN Customer Due Diligence Final Rule requires covered financial institutions to collect and verify identifying information, including full legal name, date of birth, address, and an identification number, before a business relationship is formed. That verification step is what gives downstream AML checks their legal and operational weight.
The term “AML identity verification” covers both layers: the identity-confirmation step and the AML screening that immediately follows, including sanctions lists, PEP databases, adverse media, and ongoing monitoring. Treating them as separate processes is the compliance gap that regulators keep finding.
The regulatory mandate: what the rules actually require
Across jurisdictions, the requirements share a common structure. FATF’s 40 Recommendations, adopted by more than 200 countries, established under Recommendation 10 that regulated entities must identify customers using reliable, independent source documents and verify that identity before or during a business relationship. The standard is risk-based: higher-risk customers face more thorough checks, but no customer escapes the identification step.
In the United States, the FinCEN Customer Due Diligence Rule extends this obligation to the beneficial owners of legal entity customers, not just the account holder. The April 2026 OCC notice of proposed rulemaking on AML/CFT program requirements signals a further shift toward effectiveness-driven compliance, placing more weight on institutions to demonstrate that their identification and screening processes produce results, not just that they exist on paper.
In the EU, the 6th Anti-Money Laundering Directive and the incoming EU AMLA authority extend these obligations to a wider range of obliged entities: crypto asset service providers, letting agents, high-value goods dealers, and company formation agents. Verification isn’t optional for any of them.
The AML compliance landscape in 2025 now covers more business types and regions than at any earlier point, making the identity step harder to defer or fragment.
How AML identity verification works, step by step
A compliant AML identity verification process follows five stages. Each one builds on the confirmation produced by the one before it.
Document verification. The customer presents a government-issued identity document, such as a passport, national ID card, or driver’s licence. Automated optical character recognition extracts the data fields, while AI forensic checks confirm the document is genuine, unaltered, and consistent with the issuing country’s template. Modern document verification systems cover more than 10,000 document types from 230+ countries.
Biometric matching. A real-time selfie is compared against the photo on the identity document. A liveness check confirms the image comes from a live person rather than a printed photo or synthetic video. This step prevents impersonation attacks that document checks alone wouldn’t catch.
Sanctions and watchlist screening. Once the identity is confirmed, the customer’s name, date of birth, and nationality are screened against global sanctions lists, including OFAC, UN consolidated, EU, UK, and national designations. With more than 3,500 watchlists in scope, matching algorithms run in real time and flag both exact and fuzzy-name matches for review.
PEP and adverse media checks. The confirmed identity is cross-referenced against politically exposed persons databases and screened against news sources for adverse media flagging financial crime, bribery, or reputational risk. These checks go beyond a binary pass/fail: context matters, and a PEP match that goes unexplained is itself a risk signal.
Risk scoring. The combined output of all four prior stages feeds into a risk score. High-risk results trigger enhanced due diligence. Low-risk results clear the customer for onboarding. The score is evidence, not a verdict. The compliance team retains the decision.

When AML identity verification applies in the customer journey
Verification isn’t a one-time event at account opening. Regulators require it at several defined points across the customer relationship.
At onboarding. Customer due diligence must be completed before a business relationship is established, or at the latest at the time of the first transaction. For banks, fintechs, and payment services, this means verification before an account is activated, not after the customer has already transacted.
On trigger events. A material change in a customer’s circumstances, such as an address update, a beneficial ownership change, or a transaction pattern that deviates from the established profile, triggers re-verification of the relevant data. The trigger is specific. It’s not an invitation to re-run the full onboarding flow unnecessarily.
Periodically. High-risk customers are subject to review at defined intervals. What counts as sufficient depends on the jurisdiction and the customer’s risk classification, but annual or biannual re-checks are common in regulated sectors. Ongoing AML monitoring is now largely automated at scale. Platforms surface risk-profile changes in real time rather than waiting for the scheduled review cycle.
What happens when a customer fails AML identity verification
A failed identity verification doesn’t mean the customer is a criminal. It means the process couldn’t confirm identity to the required standard. The correct response depends on what failed and why.
If the identity document is rejected for reasons such as expiry, an unsupported issuing country, or a failed forensic check, the institution typically permits a second attempt with a different document before escalating to manual review.
If a sanctions match is returned, onboarding must pause. The institution conducts a manual review, and in most jurisdictions a confirmed match requires a Suspicious Activity Report (SAR) to be filed with the relevant financial intelligence unit. Proceeding while a sanctions match is unresolved is a compliance failure, not a judgment call.
If a PEP match is returned, enhanced due diligence applies. The customer isn’t automatically declined, but the approval threshold rises. Additional documentation on source of funds, business purpose, and beneficial ownership may be required before the relationship can proceed.
What institutions cannot do is activate the account while a verification is unresolved. The same principle applies in digital financial services: KYC/AML compliance for e-wallets requires verification to gate the relationship, not follow it.
How Shufti handles AML identity verification
The compliance pain that comes up most consistently in regulated sectors matches what the CRM data shows: teams performing checks manually, running identity verification and sanctions screening through separate portals, and reconciling results by hand. The process works until volume or geography creates a gap that manual workflows can’t close.
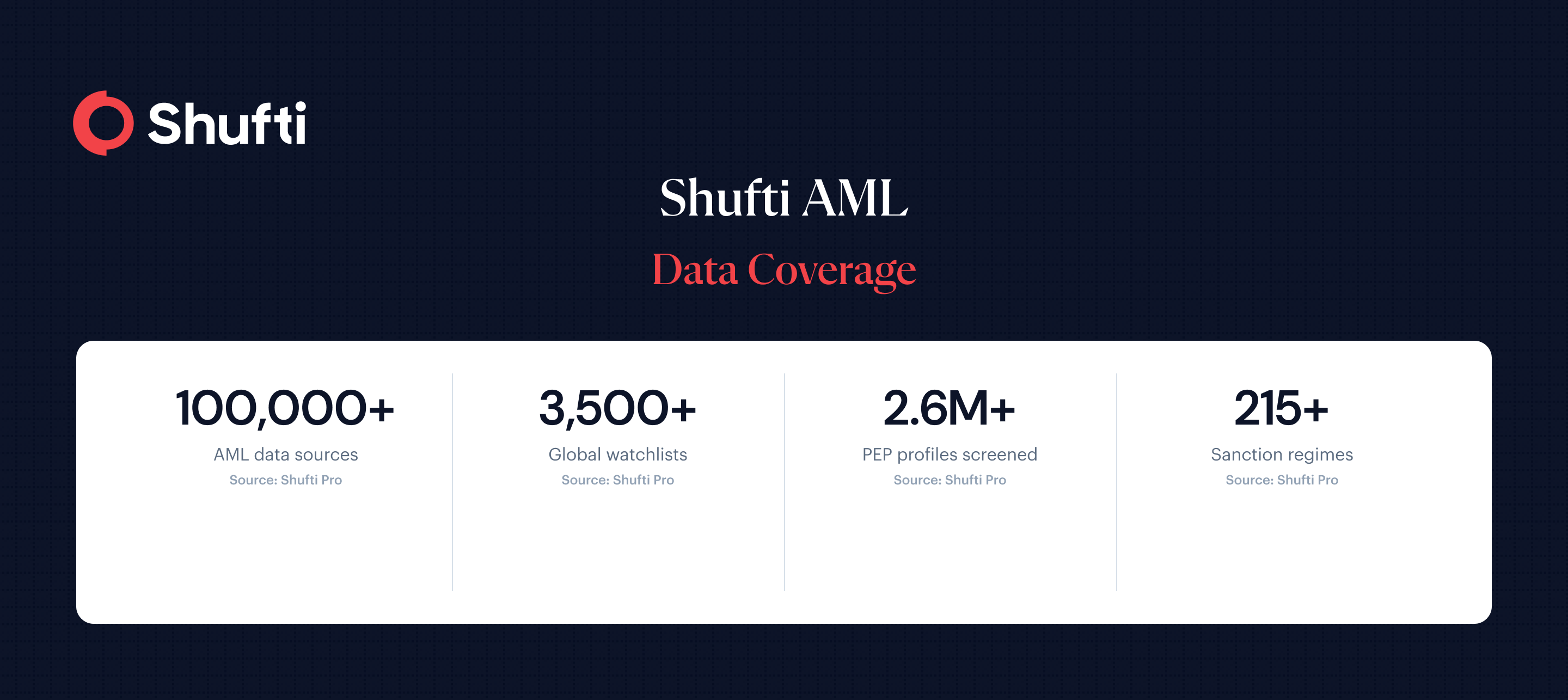
Shufti AML screening platform runs the full five-stage process through a single API. Document verification, biometric liveness detection, sanctions screening across 3,500+ global watchlists, PEP checks against 2.6 million profiles across 215+ sanction regimes, and adverse media monitoring across 50,000+ news sources all execute within the same workflow. The identity verification step and the AML screening step are not separate integrations. They produce a combined risk signal from a single check, with a unified audit trail.
Configurable risk rules let compliance teams set thresholds by industry and region. A crypto exchange facing FATF Travel Rule obligations sits in a different risk context than a retail payment platform operating under UK FCA rules, even when reviewing the same customer profile. The platform supports both in the same instance without requiring separate configurations or separate vendor contracts.
Compliance teams running identity verification and AML screening through separate tools spend more time reconciling results than acting on them. Shufti’s AML screening platform combines document verification, biometric checks, and sanctions and PEP screening into one unified workflow, so your analysts have a single audit trail and no gaps to close. Request a demo to see the full AML identity verification flow running on your own onboarding volumes.
Frequently Asked Questions
What identity documents are required for AML identity verification?
Most regulated sectors accept any current government-issued photo ID, such as a passport, national ID card, or driver's licence. The document must be machine-readable and from a covered issuing country. High-risk customers may be asked to provide a second form of identity.
How often should financial institutions re-verify customer identity under AML rules?
There's no single universal interval. High-risk customers are typically reviewed annually or when a material change occurs. Lower-risk customers may be re-verified every three to five years, with trigger-based re-checks applying regardless of the scheduled cycle.
At what point in the customer journey must AML identity verification be completed?
FATF Recommendation 10 and most national implementations require verification before the business relationship is established, or at the time of the first transaction at the latest. For digital onboarding, this means before account activation.
What happens when a customer fails AML identity verification during onboarding?
A document rejection typically allows a second attempt with a different document. A sanctions or PEP match pauses onboarding, triggers manual review, and may require a Suspicious Activity Report. The relationship cannot proceed while a match is unresolved.
How long does AML identity verification take?
Automated AML identity verification typically returns a combined identity and screening result in under 60 seconds from document submission. Manual reviews for complex cases or enhanced due diligence take longer, from a few hours to several days depending on the documentation required.












