Transaction Monitoring in AML: Ultimate Guide For 2026

Between $800 billion and $2 trillion in illicit funds enter the global financial system every year, according to the UNODC. Banks, fintechs, and crypto platforms are the front line of defence against that flow, and transaction monitoring is the mechanism that keeps that defence operational. Most compliance teams already have a monitoring system in place. The harder question is whether it is calibrated precisely enough to catch layered financial crime without burying analysts in alerts that turn out to be nothing.
This guide covers how AML transaction monitoring works, which rules and thresholds actually matter, how to manage false positives without cutting corners on coverage, and what regulators expect from monitoring programmes in 2026.
What is AML transaction monitoring?
AML transaction monitoring is the continuous review of customer payment activity to detect patterns that indicate money laundering, terrorist financing, or other financial crime. Unlike a one-time identity check at onboarding, monitoring runs across the full life of a customer relationship, comparing each transaction against predefined rules and statistical models.
When activity matches a rule, such as an unusually large cash deposit, rapid fund movement across multiple accounts, or behaviour inconsistent with a customer’s stated business purpose, the system generates an alert. That alert goes to a compliance analyst for review. If the analyst cannot adequately explain the activity, the institution files a Suspicious Activity Report (SAR) with the relevant Financial Intelligence Unit.
Transaction monitoring sits within a broader AML programme alongside identity checks and customer due diligence. For more on how these layers connect, see how transaction monitoring extends beyond standard AML screening.
How does AML transaction monitoring work?
Transaction data, covering amount, counterparty, channel, geography, and timing, feeds into the monitoring engine in near-real time or on a scheduled batch cycle. The engine applies rules and models to that data. A detected anomaly produces an alert, which goes to an analyst for review, and the outcome is documented in a case management system.
FATF Recommendation 20 requires financial institutions to promptly report to their national FIU when they have reasonable grounds to suspect that funds are linked to money laundering or terrorist financing. Transaction monitoring is the system that generates those grounds and produces the documented evidence behind each SAR filing.
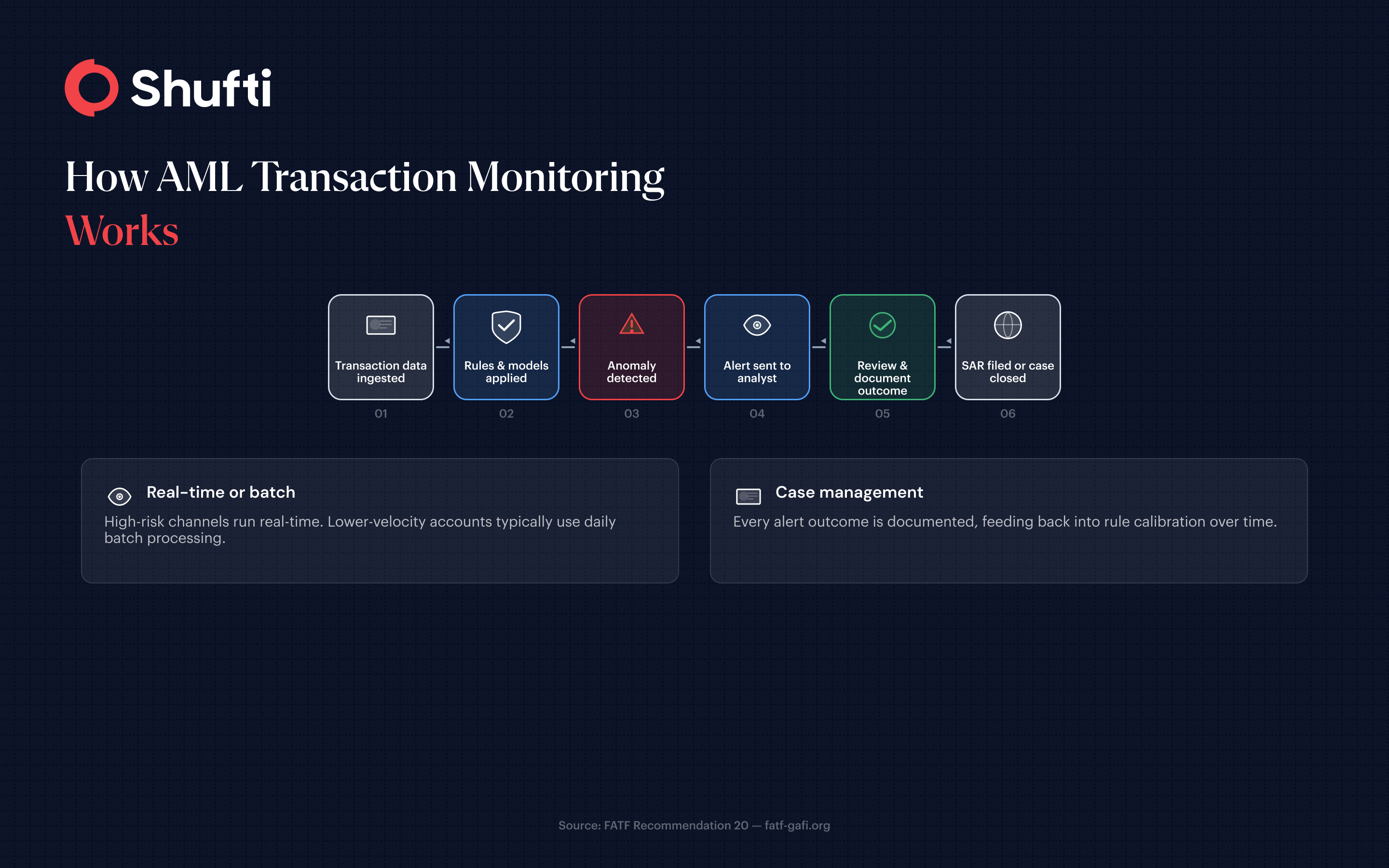
The review stage is where most programmes fail. Alert volume grows faster than analyst capacity, case notes become inconsistent across reviewers, and the same low-risk patterns get re-investigated month after month. Good monitoring design embeds triage logic into the alert workflow itself, giving analysts a pre-structured path rather than leaving all judgment to each individual reviewer.
Real-time vs batch monitoring
Real-time monitoring assesses each transaction as it occurs. Batch processing reviews groups of transactions at fixed intervals, typically daily. Many institutions run both: real-time monitoring for high-risk channels such as wire transfers and crypto, where settlement happens in seconds and a flagged transaction can still be intercepted, and batch processing for lower-velocity accounts where the economics of real-time infrastructure are harder to justify.
FATF’s June 2025 revision to Recommendation 16 on payment transparency has pushed more institutions toward real-time monitoring for cross-border wire transfers. The revised standard requires fuller originator and beneficiary data to accompany each payment. That richer data profile makes real-time anomaly detection more precise and gives analysts a clearer picture when reviewing flagged transfers. For a closer look at how screening and monitoring differ at the transaction level, see transaction screening vs. transaction monitoring.
What transaction monitoring rules should a bank have?
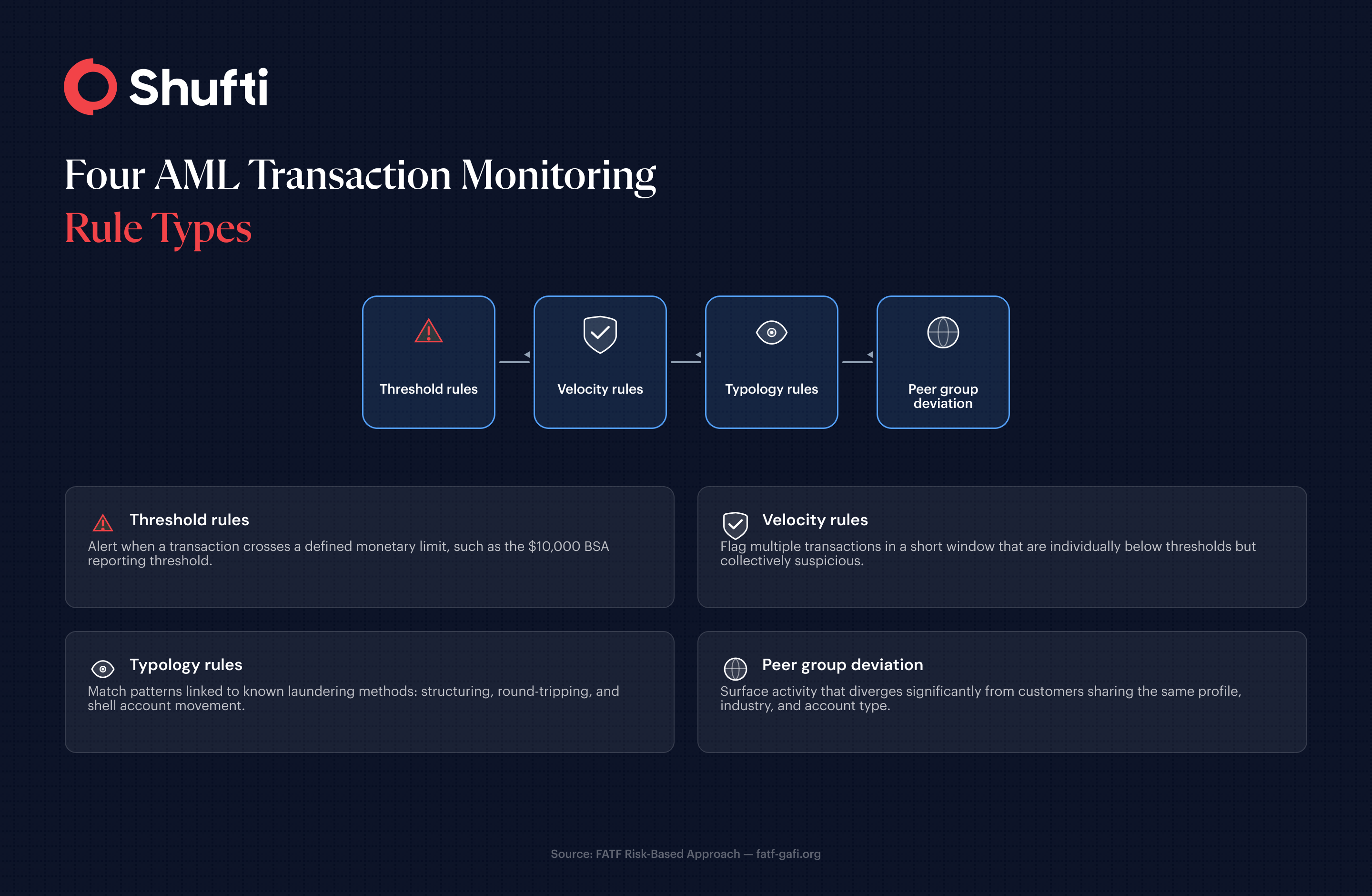
Rules are the core logic of any monitoring system. Each rule defines a pattern that, when matched, triggers an alert. The design of those rules directly determines both detection accuracy and false positive volume.
Standard rule categories cover four areas. Threshold rules generate an alert when a transaction crosses a defined monetary limit. The $10,000 cash reporting threshold under the Bank Secrecy Act is the most cited example, but institutions typically set internal thresholds below the regulatory floor to catch activity before it reaches that level. Velocity rules flag multiple transactions in a short window that are individually below thresholds but collectively suspicious. Typology rules match patterns associated with known laundering methods, including structuring, round-tripping, and rapid movement through shell accounts. Peer group deviation rules surface activity that diverges from customers with the same profile, industry, and account type.
Banks that rely almost entirely on threshold rules are straightforward to evade. Structuring, which involves breaking large sums into smaller deposits to stay below reporting limits, is designed precisely to exploit static thresholds. A rule library covering all four categories, reviewed regularly against current criminal typologies, is considerably harder to engineer around.
Setting suspicious transaction thresholds
There is no universal threshold. Institutions calibrate limits based on customer risk profiles, business model, and regulatory guidance. A payment processor handling high-frequency small-value transactions needs different velocity rules than a private bank serving high-net-worth clients.
Thresholds also need to evolve. Criminal typologies shift as networks learn what triggers alerts and adjust their patterns accordingly. Annual rule reviews, at minimum, are now a baseline expectation from regulators across every major jurisdiction.
How to reduce false positives in AML transaction monitoring
False positives are the primary operational challenge in transaction monitoring. Understanding how false positives arise in AML monitoring matters because alerts that close as non-suspicious consume analyst time, create case backlogs, and erode review quality overall when analysts start treating every alert as routine.
The root causes are usually poorly calibrated thresholds, rules that do not account for customer context, and no feedback loop between alert outcomes and rule logic. When an analyst closes an alert as non-suspicious, that finding should inform the rule. If the same rule repeatedly generates alerts that escalate no further, the rule needs adjustment.
Practical steps to cut false positives without weakening detection:
- Segment customers by risk tier before applying rules. A money services business and a professional services firm need different monitoring parameters, even if their transaction volumes look similar.
- Apply exclusion lists for persistently clean accounts where the alert pattern is predictable and the risk is genuinely low.
- Tune velocity rules to reflect seasonal business cycles. A retailer’s transaction volume in peak trading periods is not suspicious, but a monitoring system that does not account for that will generate a surge of false alerts every December.
- Run machine learning anomaly detection alongside rule-based alerts rather than in place of them. Rule-based systems are auditable and explainable to regulators. Statistical models catch complex patterns that fixed rules miss.
The FinCEN SAR filing data shows that SAR volumes continue to grow year on year. Institutions filing high-quality, actionable reports are those with monitoring systems precise enough to separate genuine risk from routine business activity.
Regulatory expectations for AML transaction monitoring in 2026
Regulators across major jurisdictions now expect a risk-based approach to monitoring, not a uniform rule set applied identically to every customer. FATF Recommendation 1 establishes that AML controls must be proportionate to risk, and transaction monitoring rules are expected to demonstrate that proportionality in practice.
For European institutions, the EBA’s July 2025 Opinion on ML/TF risks identified transaction monitoring as one of the most common areas of inadequate AML control. The opinion noted that almost half of competent authorities assess financial institutions’ AML systems as insufficient, with transaction monitoring called out as a specific gap.
The practical implication for compliance teams is clear. Treating monitoring as a static deployment that runs unmanaged in the background is now a regulatory liability. Annual rule reviews, documented rationale for threshold decisions, and evidence that alert outcomes feed back into rule calibration are the baseline expectation across EU, US, and major APAC jurisdictions. The question is not whether regulators will scrutinise transaction monitoring programmes. They already are.
When transaction monitoring generates more noise than insight, compliance analysts spend their time clearing false positives instead of investigating genuine risk, and the cases that matter get less attention than they deserve. Shufti’s AML screening integrates transaction monitoring with sanctions, PEP, and adverse media checks in a single platform, so your team works from a unified risk picture rather than stitching together outputs from separate tools. Request a demo to see how the monitoring workflow performs on your own transaction volumes and customer mix.
Frequently Asked Questions
What is a transaction monitoring rule?
A transaction monitoring rule is a defined condition that triggers a compliance alert when a customer's payment activity matches a specific pattern. Rules typically cover monetary thresholds, velocity, typologies associated with financial crime, and deviations from peer group behaviour.
What is a suspicious transaction threshold?
A suspicious transaction threshold is a monetary or behavioural limit that flags a transaction for analyst review. Institutions set their own thresholds based on customer risk profiles and business model, rather than relying on regulatory reporting limits alone.
How do banks decide which transactions to flag?
Banks apply rules and statistical models to identify activity that crosses monetary thresholds, shows unusual velocity, matches known laundering typologies, or diverges from a customer's expected behaviour. Transactions matching one or more conditions are queued for analyst review.
What happens when a transaction is flagged by AML monitoring?
The transaction generates an alert that goes to a compliance analyst. The analyst reviews the customer's full activity picture, documents the findings, and either closes the alert or escalates it to a Suspicious Activity Report filed with the relevant FIU.
What is the difference between transaction monitoring and payment screening?
Payment screening checks individual transactions against sanctions lists before processing, at the point of payment. Transaction monitoring is broader, reviewing patterns in ongoing activity over time to detect laundering schemes that no single transaction would reveal on its own.












