Masked face recognition: how it works, where it’s deployed, and what the law says

When face recognition was first deployed at scale, nobody designed it to work around surgical masks. Then 2020 arrived, and within months, every biometric access system, airport e-gate, and KYC flow was confronted with exactly that scenario. Systems that performed well on unmasked images suddenly struggled. Error rates climbed. Security teams were left deciding whether to lower thresholds, add manual review queues, or replace their vendor entirely.
The situation has changed since then. Architects specifically trained on partial occlusion scenarios have narrowed the accuracy gap. Liveness detection has adapted to work alongside masked subjects. But the technology is now moving faster than the regulations governing it, and that gap is creating real compliance exposure for organisations that deploy biometric verification at scale.
This article covers how masked face recognition works technically, what liveness detection contributes to masked contexts, where the technology is being adopted today, and how the EU AI Act and GDPR shape what you can actually deploy.
What is Masked Face Recognition?
Masked face recognition is the ability of a biometric system to verify or identify an individual when part of their face, typically the lower half, is covered by a physical mask. The intersection of face mask and facial recognition creates a fundamental geometry problem: where standard face recognition relies on full facial geometry, masked systems must infer identity from the visible region only.
How Modern Systems Handle Partial Occlusion
NIST tested 89 commercial facial recognition algorithms against digitally applied face masks in 2020. The best algorithms, which normally failed to match a face about 0.3% of the time, saw error rates climb to between 5% and 50% under mask conditions. Mask shape mattered. Black masks and deeper nose coverage degraded performance most. Round masks produced fewer errors than irregular ones.
A December 2020 follow-up from NIST told a different story. Among 65 newly submitted algorithms, some developers had built what NIST called “mask-agnostic” systems, producing comparable performance on both masked and unmasked inputs. The field had moved quickly once the problem was framed precisely.
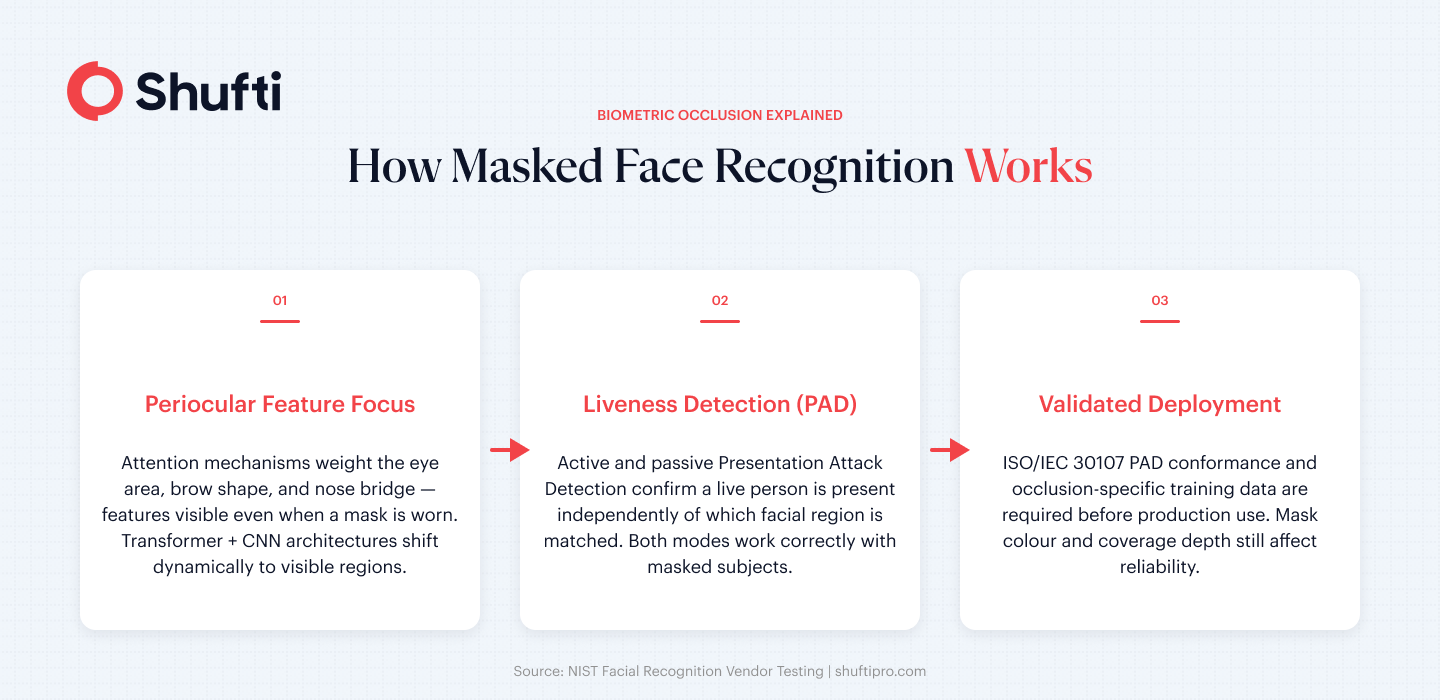
Attention Mechanisms and Periocular Focus
Contemporary masked face recognition models use attention mechanisms to weight the periocular region, the area around and between the eyes, far more heavily than lower-face features. Transformer-based architectures combined with convolutional networks can shift feature extraction dynamically toward visible facial regions, rather than returning a low-confidence score when expected geometry is absent.
ResNet-50 backbone models adapted for partial occlusion consistently outperform general-purpose face recognition models in masked test scenarios, according to peer-reviewed research in this area. A well-trained system can produce a reliable identity match from the eye area and brow structure alone.
Demographic Bias in Masked Face Recognition
Masked face recognition inherits the demographic gaps of its training data, then amplifies them. Studies show higher false rejection rates for darker skin tones and women when occlusion removes lower-face anchors. Organisations deploying masked biometric systems must audit error rates across demographic groups, not just headline accuracy figures.
Face Reconstruction and Unmasking
Some systems go beyond working with visible features they attempt to infer or reconstruct the occluded lower face using generative models. While this can improve match confidence, it introduces synthetic data into a verification decision, raising questions about reliability, explainability, and whether reconstructed geometry constitutes legitimate biometric evidence.
What Masks Cannot Hide
Eye geometry, iris texture, and brow shape remain highly discriminative biometric signals. Systems retrained for occlusion can match on these features with accuracy approaching, though not yet equalling, full-face performance. Mask colour and coverage depth still affect reliability, which is why procurement decisions for masked-face applications require attention to the specific training conditions of the model being deployed.
What Liveness Detection Adds in Masked Contexts
Identity matching and presence verification solve different problems. Face recognition answers who someone claims to be. Liveness detection answers whether a live person is actually present, rather than a static photo, video replay, silicone mask, or AI-generated face.
In masked contexts this distinction matters more than it does in full-face scenarios. A system that identifies a face through a mask using periocular features also creates a more specific spoofing surface. An attacker could in theory present a physical mask over the lower face while displaying a photograph of another person’s eyes and brow region above it.
Active and Passive Liveness in Masked Scenarios
Active liveness detection asks the subject to perform a gesture, such as a blink, a slight head turn, or a nod. These movements do not depend on lower-face features, so they remain reliable when a mask is present. Passive liveness detection analyses the live camera feed for depth, texture irregularities, and anti-spoofing signals without requiring any user action. Both modes function correctly with masked subjects when they have been validated in that configuration.
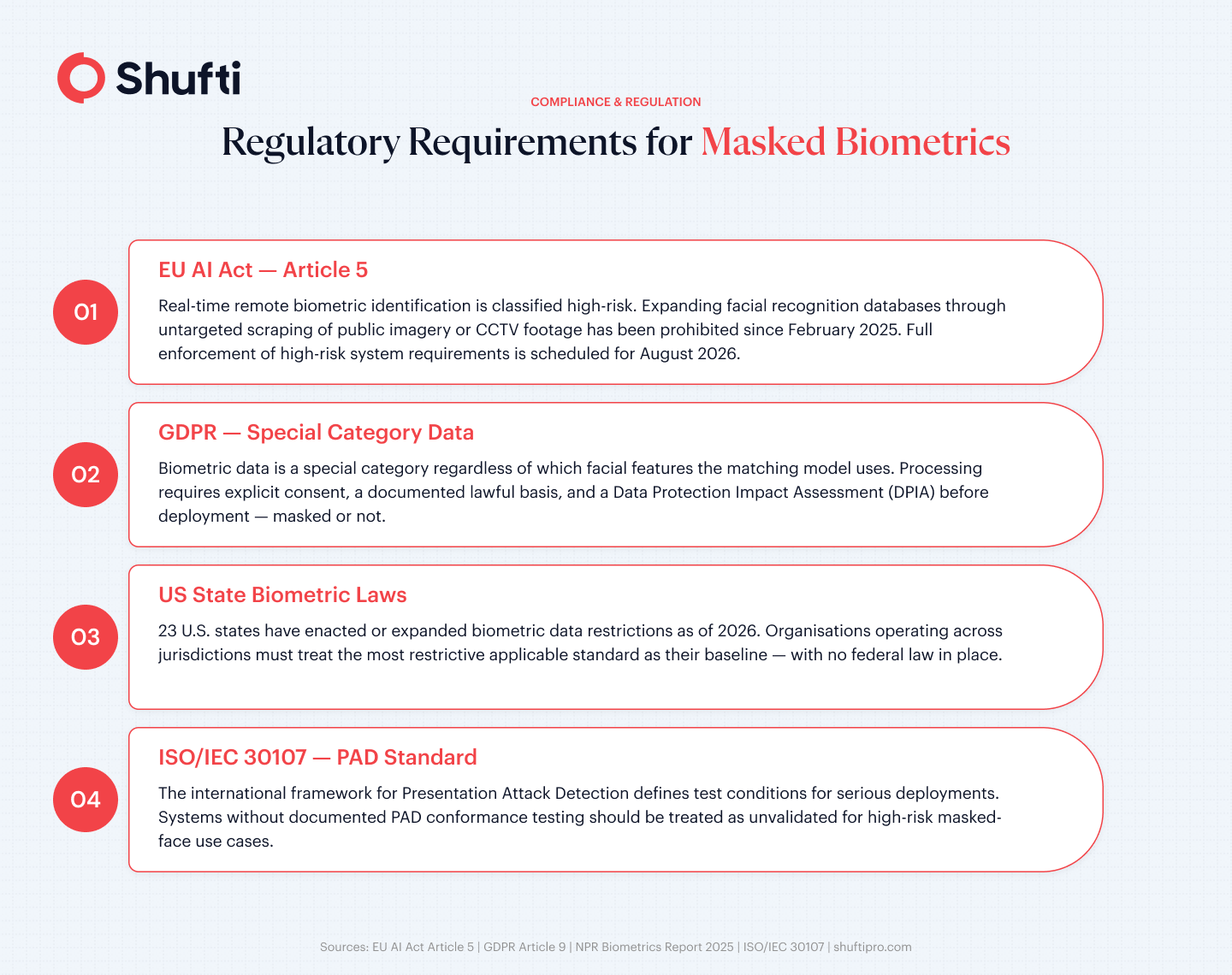
ISO/IEC 30107 defines the international framework for Presentation Attack Detection (PAD) and provides the test conditions that serious deployments measure against. A masked-face-capable system without documented PAD conformance testing should be treated as unvalidated for high-risk use cases.
The relationship between liveness and deepfake defence is directly relevant here. Generative face-swap attacks have begun targeting the periocular region specifically, since that is where masked recognition systems concentrate their feature extraction.
Where Masked Face Recognition is Being Deployed Today
Aviation
Airport e-gates and boarding flows have moved aggressively toward biometric-first processing. The TSA expanded its facial recognition program to 80 U.S. airports by December 2024, with a nationwide rollout planned. IATA data for 2024 shows 46% of passengers used biometrics at airports that year. 73% said they prefer biometric identification over presenting physical documents. Modern airport systems are built to accommodate passengers in normal clothing, including religious face coverings, medical masks, and personal protective equipment. Contactless processing has moved from an edge case to a design requirement.
Healthcare and Access Control
Healthcare facilities adopted masked face recognition for staff access control during the pandemic, driven by a hygiene case that made touch-based authentication impractical. Badge taps and PIN entry shifted to contactless facial recognition, with mask compatibility becoming a procurement requirement rather than a bonus capability.
The face recognition use case in remote identity verification flows is closely related. As regulated industries accept selfie-based onboarding, what happens when a user’s face is partially covered becomes a direct reliability question for fraud and compliance teams, not a theoretical one.
Regulations Governing Masked Face Recognition
The EU AI Act classifies real-time remote biometric identification as high-risk. The prohibition on building or expanding facial recognition databases through untargeted scraping of public imagery or CCTV footage came into effect in February 2025 under Article 5. Full enforcement of high-risk system requirements, including those covering law enforcement biometric identification, is scheduled for August 2026.
GDPR classifies biometric data as a special category regardless of which facial features the matching model uses. Processing it requires explicit consent, a documented lawful basis, and a data protection impact assessment before deployment. Masked face recognition does not reduce that obligation. The capture event processes biometric data whether or not the full face is visible.
In the United States, no federal facial recognition law exists as of 2026, but 23 states have enacted or expanded biometric data restrictions. Organisations operating across jurisdictions need to treat the most restrictive applicable standard as their baseline.
The practical upshot for any organisation deploying masked face recognition for identity verification is that a legal basis, DPIA, and data retention policy must all be in place before the system processes its first live capture.
How Shufti Enables Secure Masked Face Recognition
Masked face recognition has matured from an emergency workaround into a production-grade capability, but getting it right still requires deliberate validation of which liveness approach is in scope, what spoofing vectors the system has been tested against, and whether the deployment meets the data protection requirements of every jurisdiction it operates in. Shufti’s face verification covers 56+ anti-spoofing attack vectors, operates across cloud, on-premises, and hybrid deployments, and holds iBeta Level 1 and 2 certification. Request a demo to run masked-face scenarios through the liveness stack and see the detection output directly.
Frequently Asked Questions
How does face recognition work when someone wears a mask?
Modern systems use attention mechanisms to extract identity features from the periocular region, around the eyes and brow, when lower-face geometry is unavailable. Performance is lower than full-face matching but remains usable when the model has been trained and validated on occluded-face datasets.
How do liveness detection systems complement masked face recognition?
Liveness detection runs independently of which facial region is used for identity matching and confirms that a live person is present. Both active and passive liveness modes work correctly with masked subjects because the presence signals they rely on, depth, texture, micro-movement, are not dependent on lower-face geometry.
Do airport e-gates use face recognition that works with masks?
Yes. Airport systems across the US, EU, and APAC are built to accommodate face coverings as standard. The TSA expanded its biometric program to 80 U.S. airports by December 2024, with masked subjects part of the operational reality those systems must handle.
Can criminals use masks to evade face recognition surveillance cameras?
A standard mask reduces recognition accuracy but does not defeat systems trained on periocular features. Accuracy is lower than in unmasked conditions, so surveillance outputs in masked scenarios should not be treated as forensically conclusive without corroborating evidence.
Are there laws that restrict masked face recognition by governments?
Yes. The EU AI Act prohibits expanding facial recognition databases through untargeted scraping of public images or CCTV footage, effective February 2025. GDPR requires explicit consent and a documented DPIA for any biometric processing, masked or not, and similar rules apply in an increasing number of US states.











