Presentation Attacks: A Practitioner’s Guide to Liveness Detection and PAD

Fraud teams at regulated financial firms keep running into the same question. Is the selfie on our screen a real person, a photograph of one, or a deepfake assembled an hour ago? Answering it well decides whether onboarding scales cleanly or quietly leaks synthetic identities into production.
Presentation attacks are not new, but the attack surface has widened fast. Cheap deepfake tools, leaked datasets of real selfies, and commodity silicone masks give one attacker several ways to impersonate a customer. For compliance and fraud leaders running remote verification in Europe, that shifts the question from whether a liveness check is in place to what kinds of attacks it actually catches. This piece walks through what a presentation attack is under the governing standards, the attack types seen in live deployments, how presentation attack detection reads them, and how PAD is independently tested.
What Is A Presentation Attack?
A presentation attack is an attempt to fool a biometric system by presenting something other than a live, genuine user to its sensor. ISO/IEC 30107-3:2023 defines the term, along with the object or medium used to carry out the attack, which the standard calls a presentation attack instrument, or PAI. A printed photograph is a PAI. So is a silicone mask. So is a high-resolution video playing on a tablet held up to the camera.
The standard splits attacker intent into two patterns. Impersonation is the attacker trying to pass as a specific other person, usually someone whose identity document they already hold. Evasion is the attacker trying to avoid being recognised as themselves, for example to pass a new account check while a known alias is already flagged. Both patterns look different to a PAD model, which is why strong implementations test against a mix of the two rather than treating biometric spoofing as a single category.
Presentation layer attacks sit at the sensor itself, before the matching engine ever runs. That matters for procurement decisions, because detection has to happen in the capture pipeline. A model that only analyses the cropped face after upload loses most of the signal.
Most Common Types of Presentation Attacks
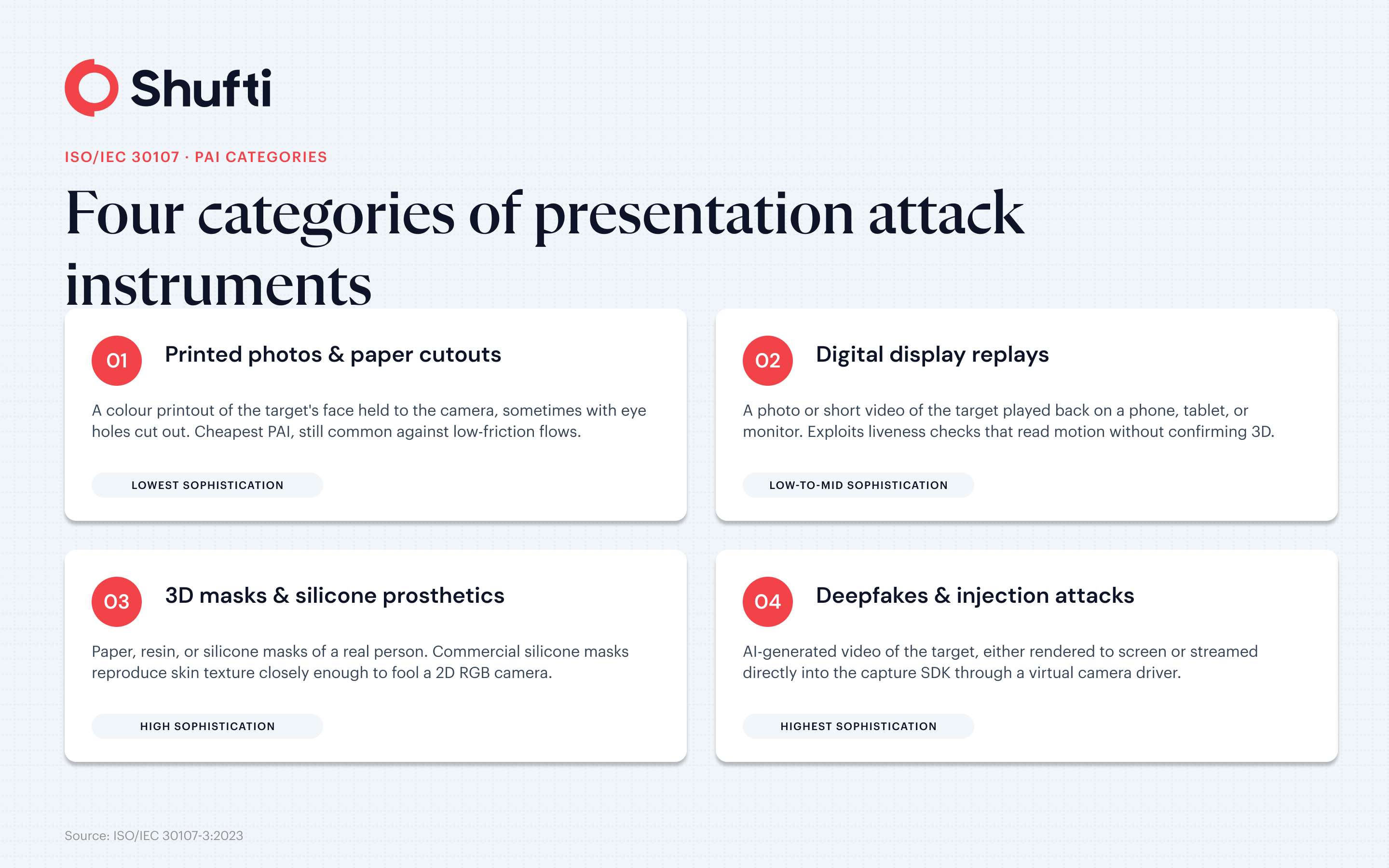
Under ISO/IEC 30107, every real-world attack maps to a PAI. In production deployments, four PAI categories dominate.
Printed Photos And Paper Cutouts
The simplest and oldest PAI. The attacker holds a colour printout of the target person’s face to the camera. A paper cutout with eye holes punched through lets the attacker blink behind it. Printed attacks cost almost nothing to produce, which is why they still show up in volume against low-friction onboarding flows.
Digital Display Replays
A photo or short video of the target person played back on a phone, tablet, or monitor. Replay attacks are more convincing than print because the screen can render texture, small head movements, and live video captured from social media. They exploit any liveness check that looks only at motion without confirming the face exists in three dimensions.
3D Masks And Silicone Prosthetics
Physical masks made from paper, resin, or silicone. Commercial silicone masks mimicking a real person now cost a few hundred dollars and reproduce skin texture closely enough to fool a 2D RGB camera. They are the PAI that accredited test labs tend to place in the hardest testing tier.
Deepfakes And Injection Attacks
AI-generated video of the target person, either rendered to screen and captured by the camera, or streamed directly into the capture SDK through a virtual camera driver. The second variant is an injection attack. It skips the camera entirely and is difficult to detect by signals that rely on how a real scene reaches a sensor. The ENISA Threat Landscape 2025 tracks rising use of AI-generated media in identity fraud across EU financial services.
These are sometimes described as presentation layer attacks, since they target the biometric system’s point of capture rather than its back-end matching or storage.
What Presentation Attack Detection Actually Looks At?
Presentation attack detection is the set of techniques a biometric system uses to decide whether what it is seeing is a live human face or a PAI. Two broad families of signal show up in most modern stacks.
Active And Passive Liveness
Active liveness asks the user to do something. A small head turn, a blink, a smile on cue. The motion cue is compared against the expected response, and the stack looks for the micro-signals real faces produce and flat PAIs do not. Passive liveness runs silently. The user holds still while the system analyses the image for depth, texture, and light reflection against what a real 3D face should produce. Passive checks add no friction, but they demand stronger models.
Multi-Spectral Sensors And Infrared
On devices that carry extra hardware, multi-spectral sensors can reveal what a visible-light camera misses. Infrared reflects differently off skin than off paper, plastic, or a display screen. That gives PAD an extra signal difficult to fake without matching hardware. Smartphone cameras without dedicated sensors still get useful signal from frame-level frequency analysis, which detects the banding and aliasing that appear when a camera records another screen.
Deep Learning Models And Training Data
Modern PAD engines run convolutional and transformer-based models trained on datasets that mix bona-fide captures with labelled PAIs. Public datasets include CASIA-FASD, Replay-Attack, and OULU-NPU, though each has known coverage gaps. The harder generalisation problem is that a model trained on yesterday’s deepfakes often under-performs on a new generator released next month, which is why production stacks combine model ensembles with frequency-domain and behavioural checks.
How PAD Systems Are Independently Tested?
Claims about PAD accuracy are easy to make. Independent testing is the layer that makes them verifiable.
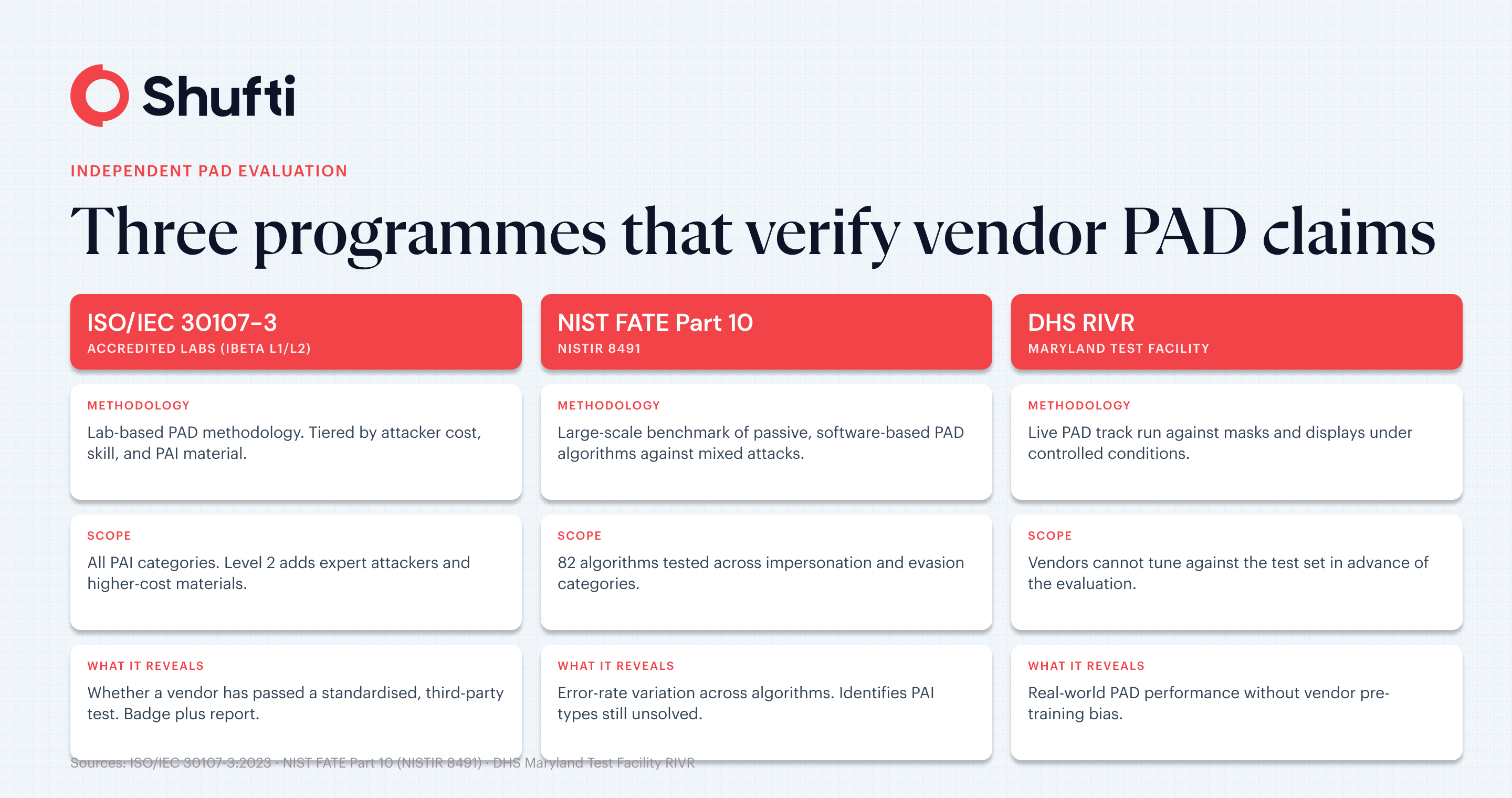
ISO/IEC 30107-3 And iBeta Levels
ISO/IEC 30107-3 defines the methodology accredited labs use to grade PAD. The widely cited iBeta Level 1 and Level 2 certifications implement that methodology. Level 1 covers lower-cost, lower-skill PAIs built within a fixed time and material budget. Level 2 raises the stakes on material cost, attacker expertise, and PAI quality. Penetration thresholds are strict, which is why Level 2 compliance meaningfully separates serious PAD implementations from marketing claims.
NIST FATE PAD
The US National Institute of Standards and Technology runs the Face Analysis Technology Evaluation, or FATE. Part 10 of the programme, reported in NISTIR 8491, evaluated 82 passive, software-based PAD algorithms against a battery of impersonation and evasion attacks. The results showed wide accuracy variation across algorithms and PAI types, with some attack categories still generating high detection error rates across every tested implementation.
DHS RIVR
The US Department of Homeland Security runs the Remote Identity Validation Rally at the Maryland Test Facility. RIVR operates a dedicated PAD track that scores systems against mask and display attacks under controlled conditions. It is one of the few publicly reported evaluations where vendors cannot tune against the test set in advance.
Practical Next Steps For Evaluating a Biometric Stack
A short checklist for procurement and internal review.
- Ask the vendor which specific PAI categories they test against. Liveness as a single undifferentiated claim is not an answer. Print, replay, 3D mask, and deepfake are different problems.
- Ask for the ISO/IEC 30107-3 test report, not just the certification badge. The report shows the attack set, attempt count, and error rates.
- Treat passive and active liveness as complementary, not alternatives. A stack that offers only one has a single failure mode.
- Check whether the vendor’s PAD is evaluated in independent programmes such as NIST FATE or DHS RIVR. Internal benchmarks do not survive regulator review at the same level as public test data.
- For remote onboarding flows exposed to deepfakes, ask about injection attack coverage specifically, since screen-level replay detection does not address a stream piped into the SDK through a virtual camera.
Presentation attacks have moved from print-and-hold demos to deepfakes and injection streams that bypass camera-based detection entirely, and older biometric stacks built against a different threat model are where most of the risk now sits. Shufti’s face verification covers over 56 anti-spoofing vectors, including deepfake and injection attacks, with active and passive liveness and independent validation at DHS RIVR 2025 and iBeta Level 1 and 2. Request a demo to run your own PAI samples through the pipeline and see the detection layer by layer.
Frequently Asked Questions
Does stronger PAD coverage affect the experience for legitimate users?
Not significantly. Passive liveness runs silently with no user action. Active liveness adds a single prompted motion taking a few seconds. Well-tuned stacks keep false rejection rates low so genuine users rarely notice the difference.
Are certain industries more exposed to presentation attacks?
Yes. Any fully remote onboarding flow with direct monetary value is a higher target — financial services, crypto platforms, and telecoms are the most frequent. Regulated sectors also face compliance consequences on top of the fraud loss itself.
How does liveness detection prevent presentation attacks?
Active liveness checks cued user motions, and passive liveness analyses texture, depth, and reflection silently. Strong stacks run both to remove single points of failure.
How does ISO/IEC 30107-3 define PAD compliance levels for biometric systems?
The standard defines the test methodology and reporting format. Accredited labs apply it as tiered levels that vary attacker time, skill, and PAI material budget, with stricter error thresholds at higher tiers.
How does ISO/IEC 30107 define a presentation attack instrument (PAI)?
A PAI is the object or medium used to carry out the attack, such as a printed photo, a replay video on a screen, or a silicone mask. Every real-world attack maps to a PAI category.