11 Common Mistakes End-Users Commit During KYC – Shufti

KYC identity verification is one big challenge for end-users. Your customers might be making a lot of mistakes during the process and a little hassle can increase the abandonment rate. Not so much of good news for the company. Well, we know how bad it can be when customers do not understand your process and leave a bad review. KYC may be a cumbersome process for many, Shufti ensures the easiest yet robust process. Over the years, we have encountered many problems and various reasons for declined verification. To make sure end-users do not commit the same mistake, here is a brief overview of the general mistakes end-users commit during KYC.
What is KYC?
KYC or Know Your Customer is an identity verification system that allows businesses to verify the identities of their customers. This allows legitimate customer onboarding and effective compliance with the customer due diligence protocols. Previously, traditional methods were used for the job but thanks to digital advancements, KYC verifies individuals in real-time.
Top 11 Consumer Mistakes Highlighted by Team Shufti
Thanks to Shufti’s synergised efforts of Human and Artificial Intelligence, our KYC experts have shared the top 11 mistakes that have repeatedly declined verification of many end-users.
Blurry Photos of the ID Document
The most common of all is shaky or blurry images of ID documents. Consumers fail to upload clear pictures of the required government-issued ID document. Ultimately, our system cannot verify the identity.
Photoshopped Images of the ID Document
To enhance the quality of the image, customers edit the image and our system does not accept photoshopped images. The authenticity checks will identify it as a tampered identity document and onboarding will fail.
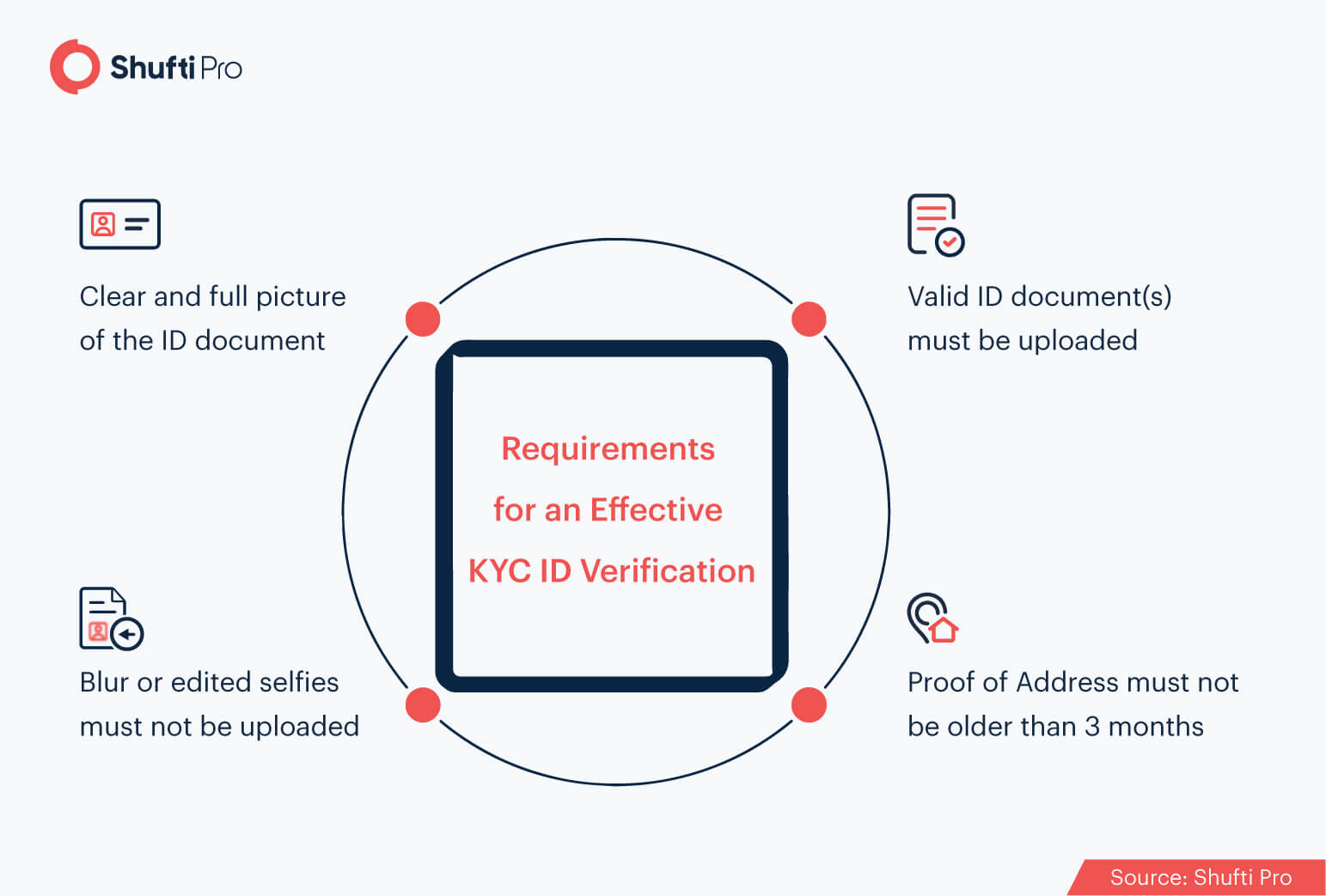
Scanned Copies of ID Documents
Shufti’s KYC identity verification accepts photos of original government-issued ID documents. Scanned images are not acceptable and end-users frequently commit this mistake. Ultimately, their verification is declined leading to the loss of a customer for the company.
Wrong ID Document Type Submitted for Verification
Merchants get the option of choosing the ID document type. In case the end-user does not submit the same identity document of client’s choice, the verification is unsuccessful. For instance, if the merchant (our client) has opted for a driver’s license for identity verification and the customer uploads a passport, the verification will decline.
*Shufti offers services in more than 150 languages supporting 3000+ ID document types
Expired ID Document
Punched and expired identity documents do not count as valid identity documents. Unfortunately, some end-users submit ID documents that are expired or punched making them an unacceptable document for KYC.
Suggested: A complete guide to understanding KYC compliance regulations
Cropped Images of the ID Document Uploaded
While uploading the ID document customers fail to submit the complete picture of the document. Sometimes the bottom of the document is visible or maybe the end-user cropped the rainbow print while uploading the document. In either case, Shufti will mark it as a declined verification.
Address on ID Document and Proof of Address Do Not Match
Address verification is another important part of identity verification, especially for e-commerce and financial institutions. For this, a secondary identity document (proof of address) is uploaded and the address on the ID document is cross-matched with the one on the address proof. The difference in both leads to declined identity verification.
Distorted Photos Submitted for Face Verification
Pictures uploaded for face verification must be clear and distorted images are one of the biggest mistakes that result in declined verifications. This attempt is generally considered as a spoof attack.
*Shufti’s face verification takes only 5 to 10 seconds
Edited Selfies Uploaded
In the selfie world, people prefer filtered images over their natural self. However, these attempts result in negative identity verification results. Our face verification system does not accept any filters, masks, glasses, etc. The picture has to be clear and original for face verification.
Face is not Clear in the Selfie
Apart from all other issues, this is the most common problem during face verification. Failure to provide a clear selfie is the major reason behind the majority of failed face verifications. For face verification with Shufti, the selfie must be clear so that all the AI-powered checks can be performed.
Picture on the ID Document and Selfie Don’t Match
Face verification is an integral part of identity verification. As per our method, the consumer has to submit a selfie during the verification. Previously captured photos, cropped images, pictures with filters, and any other edited version of pictures is not acceptable. The selfie is matched with the picture on the government-issued ID document. In case of a mismatch for whatsoever reason, verification results are unfavourable.
How Does Shufti Avoid All These Issues?
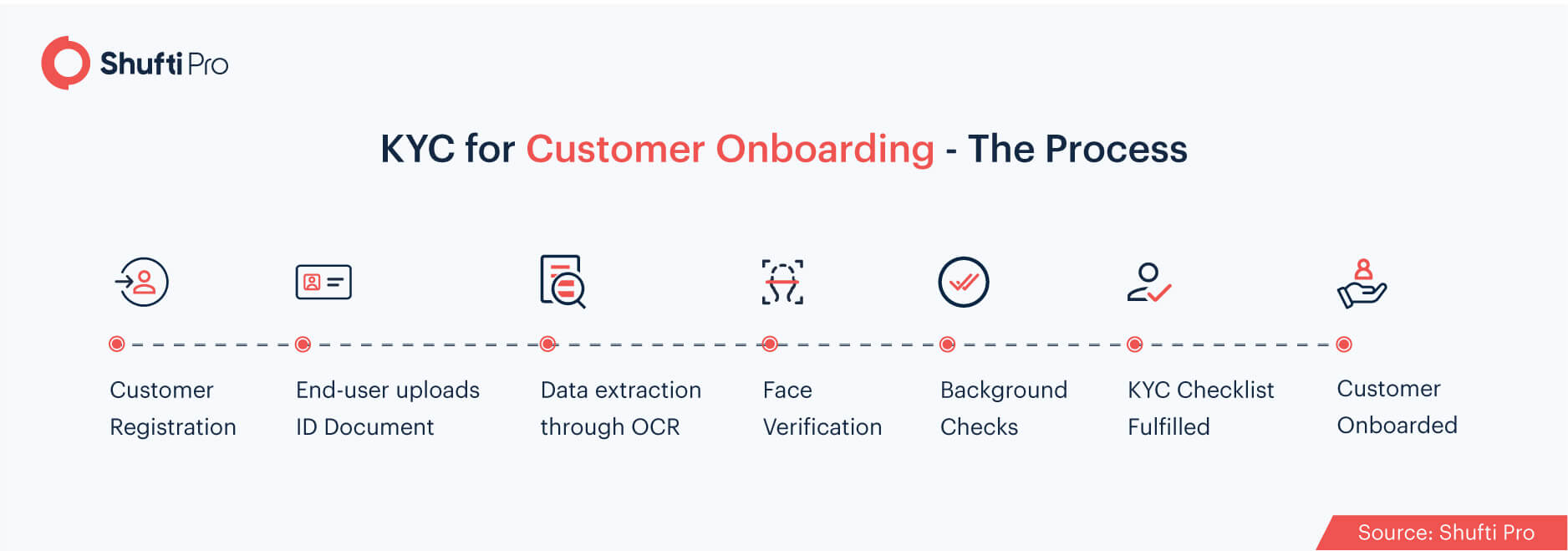
Shufti’s back office is designed to attract end-users. All the steps are clearly mentioned at each step. First, the consent for acquiring personal information is taken and then, identity verification checks begin. Shufti’s identity verification is pretty simple.
- The end-user registers for KYC
- Government-issued ID document is uploaded
- The information on the document is validated and the template is verified for forgery, tampering, etc.
- Selfie is obtained for face verification to check the remote presence of the user at time of verification.
- Background checks are performed against 1700+ global watchlists
- Identity verification results are delivered in real-time and the proof of verification is stored in the back-office.
- Customer is onboarded
To Sum Up…
End-users have a lot of ambiguity when it comes to performing KYC verification. Uploading scanned or photoshopped images, wrong document type for identity verification, expired documents, and distorted images are some of the common mistakes our team has encountered over time. Sadly, these errors result in declined identity verification. From providing AI-powered instructions to 24/7 customer support, Shufti makes sure the end-user performs KYC in the most effective way possible.
Have more questions about KYC? Get in touch with our customer support team and share all your concerns right away!












