Business Identity Verification Explained: How It Works & Why It Matters

- 01 What Is Business Identity Verification?
- 02 What does business identity verification actually check?
- 03 What data sources does verification draw on?
- 04 How Business Identity Verification Works?
- 05 Why Business Identity Verification Is Important?
- 06 Building a reliable verification process
- 07 How Shufti helps you reduce reliance on manual business identity verification
When businesses onboard corporate clients without a complete identity check, the exposure is immediate. TransUnion’s H2 2025 Global Fraud Report found that companies globally lost the equivalent of 7.7% of annual revenues to fraud last year. For many, that exposure started at onboarding, when a fraudulent or shell entity passed a surface-level review.
This article explains what the verification process involves, what regulators now require, and how to build a reliable check in practice.
What Is Business Identity Verification?
Business identity verification is the process of confirming that a legal entity is what it claims to be. It covers legal existence, ownership structure, beneficial owners, director identities, and real-time screening against sanctions databases, all completed before the business relationship begins.
What does business identity verification actually check?
Business identity verification or company identity verification answers three questions about a prospective corporate counterparty. The first is whether the entity legally exists and is in good standing. The second is who owns and controls it. The third is whether those individuals or entities carry any financial crime risk.
A single registration document answers only the first question. The other two require structured ownership queries, beneficial owner identification, and live lookups against AML databases. That is why know your business verification has become a multi-stage process rather than a single document review.
What is the difference between business identity verification and KYB?
The two terms are used interchangeably in most compliance contexts, and the overlap is deliberate. KYB (know your business) is the regulatory framework that defines what must be checked. Business identity verification describes the technical process of executing those checks. In practice, a complete KYB check includes UBO discovery and AML screening. A process that verifies only a registration number and stops there does not meet the full regulatory definition of KYB.
What data sources does verification draw on?
The process to verify business identity involves three layers of information, each serving a different purpose.
Corporate registry data confirms legal existence. This covers the certificate of incorporation, the registered address, the registration number, and the current status of the entity. For regulated industries, a trade or financial services licence number may also be required.
Ownership and control records map the structure above the registered entity. This means identifying every individual who owns or controls 25% or more of the business, as well as directors, authorised signatories, and any intermediate holding structures. Under EU Regulation 2024/1624 on anti-money laundering, obliged entities must verify this ownership data from multiple independent sources and report discrepancies in central registers within 14 days of detection.
AML and sanctions data screens the identified principals. A business can hold clean registration paperwork while a sanctioned individual sits on its board. Ownership records alone do not catch that. Live lookups against sanctions lists, PEP registers, and adverse media sources are what close the gap.
How Business Identity Verification Works?
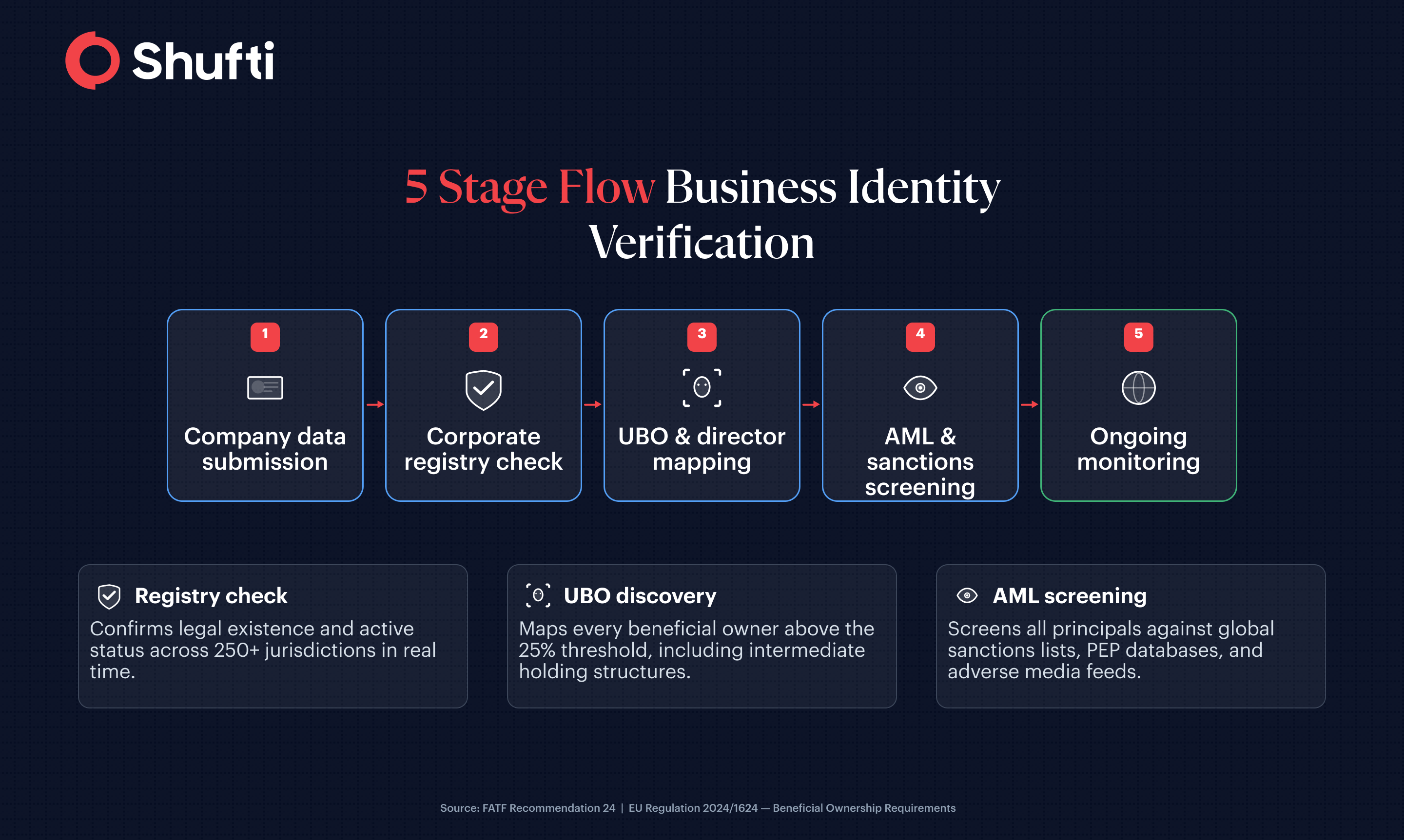
A complete business identity verification flow covers five stages.
Collecting Business Information
Stage one is company data collection. The business submits its registration number, jurisdiction, and legal name. Automated flows trigger a registry lookup at this point, with no document upload required in most major jurisdictions.
Verifying Company Registration
The second stage is the corporate registry check. The system queries the official registry to confirm the entity is active and has no dissolution or suspension notices in effect.
Identifying Ultimate Beneficial Owners (UBOs)
Ownership and director mapping come third. The system pulls ownership chains and cross-references them against shareholder registers and beneficial ownership registries. When holding companies sit between the registered entity and its ultimate owners, each intermediate layer is queried separately.
Conducting AML Screening
The fourth stage is AML and sanctions screening. Every identified UBO, director, and authorised signatory is screened against global sanctions lists, PEP databases, adverse media feeds, and watchlists. This step surfaces the financial crime risk that document verification alone cannot detect.
Ongoing Monitoring and Risk Updates
Ongoing monitoring closes the flow. Ownership structures change, sanctions lists update, and adverse media emerge after onboarding. A one-time check at the start of the relationship does not satisfy current regulatory expectations. Continuous monitoring across KYC, KYB, and transaction screening is now the standard for regulated firms.
Why Business Identity Verification Is Important?
The compliance bar for corporate identity verification has risen across most major jurisdictions in the last two years.
Business identity verification is essential to meet regulatory requirements and AML obligations. In the EU, Regulation 2024/1624 lowers the beneficial ownership identification threshold to 25% or more, with a 15% threshold applying in high-risk counterparty situations. Obligated entities must verify ownership from multiple independent data sources. The regulation takes full effect in 2027, but firms relying on document-only processes today will need to rebuild their flows before then.
Globally, the Financial Action Task Force (FATF) has identified fraud as a major money laundering risk in 90% of the jurisdictions it has assessed. Shell companies remain one of the primary vehicles for moving illicit funds, which is why UBO transparency requirements now appear in AML frameworks across North America, Europe, APAC, and the Middle East.
Synthetic identity document fraud in North America grew 311% in Q1 2025 compared to the same period the previous year. A verification process that cannot distinguish a synthetic entity from a genuine one leaves regulated businesses exposed on two fronts: financial crime liability and regulatory non-compliance.

A business identity verification built on industry best practices and regulatory guidance not only helps to avoid financial losses, but it also protects you from reputational crises involved in dealing with shell companies or those carrying out illegitimate activities.
Building a reliable verification process
The practical challenge is not knowing what to check. It is building a flow that covers all required business identity checks without adding days to the onboarding timeline.
Three principles apply across industries.
Cover every jurisdiction where you onboard business clients, not just the ones with well-known registries. A process that works in Germany but cannot query a registry in the Gulf or Southeast Asia creates coverage gaps that fraudulent entities will find.
Automate the ownership mapping step. Manual UBO discovery is the primary bottleneck in business verification processes, slowing onboarding and introducing inconsistency between cases. Automated registry queries with structured ownership output remove that bottleneck without reducing accuracy.
Treat ongoing monitoring as part of the original verification scope, not an add-on. A corporate client whose principals were clean at onboarding may have a sanctioned director added six months later. Point-in-time checks do not meet the monitoring requirements now embedded in most regulated-industry frameworks.
Remote verification is possible and expected. Jurisdictions with digital corporate registries support automated remote checks without requiring physical document submission. For markets where digital registry infrastructure is less developed, automated document upload with structured data extraction and live AML screening provides a comparable alternative.
How Shufti helps you reduce reliance on manual business identity verification
Compliance solutions, where document checks, UBO discovery, and AML screening run in separate tools, are the biggest source of onboarding delays and coverage gaps in business identity verification.
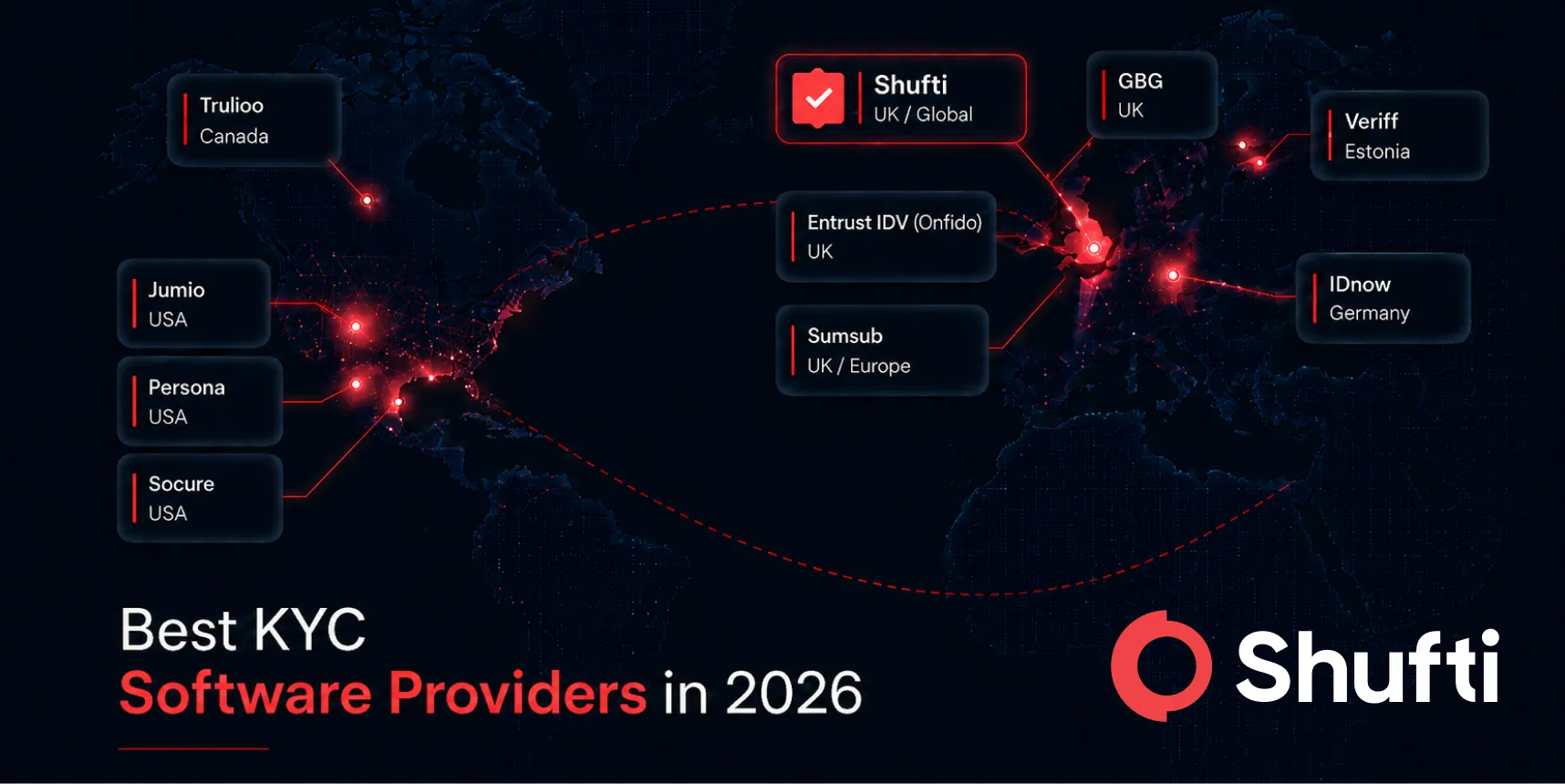
Shufti queries corporate registries across 250+ jurisdictions, maps UBO structures automatically, and runs real-time AML screening in a single flow, so your team gets a complete picture before a business relationship begins.
Request a demo to see how the full verification process works on your own use case.
Frequently Asked Questions
How do you verify a business's identity?
The process starts with a corporate registry check to confirm the entity exists and is active. It then maps ownership to identify UBOs and directors, and screens those individuals against AML databases, sanctions lists, and PEP registers. Automated solutions query multiple data sources simultaneously and return a consolidated verification result in a single workflow.
What documents are needed for business identity verification?
Standard requirements include a certificate of incorporation, the registered address, and the registration number. Ownership verification requires director information and shareholder registers, which automated systems pull directly from registries in most jurisdictions. Regulated industries may also require a trade licence or a financial services authorisation number.
Is business identity verification the same as KYB?
KYB defines what regulators require you to check. Business identity verification is the technical execution of those checks. The terms overlap in practice, but a complete KYB process includes UBO discovery and AML screening, not only a company registration lookup. A process that stops at registration does not meet the full KYB definition.
Can business identity verification be done remotely?
Yes. Most major jurisdictions now maintain digital corporate registries that support automated remote queries. For markets without fully digital registries, document upload with automated data extraction and live AML screening is the standard alternative. Both approaches meet current regulatory expectations for remote business onboarding.
What are the risks of not verifying business identity?
Regulatory fines are the most visible consequence, but operational risk runs alongside them. Onboarding a fraudulent or sanctioned entity can trigger account freezes, transaction monitoring alerts, and AML enforcement. Under EU Regulation 2024/1624, failing to report beneficial ownership discrepancies within 14 days of detection is a standalone compliance failure.