Fraud Detection vs Fraud Prevention: Key Differences Explained

- 01 Fraud Detection vs Fraud Prevention: The Core Difference
- 02 Why the Gap Between Detection and Prevention Is Costing Businesses
- 03 What Are Examples of Proactive vs Reactive Fraud Strategies?
- 04 How Do Fraud Detection and Prevention Work Together?
- 05 What Tools Are Used for Fraud Monitoring and Real-Time Fraud Detection?
- 06 How Shufti handles prevention and detection together
Consumers reported losing $12.5 billion to fraud in 2024, according to the Federal Trade Commission’s Consumer Sentinel Network Data Book. Business losses ran even higher. The FBI’s Internet Crime Complaint Center 2024 Annual Report counted $16.6 billion in adjusted losses the same year, spread across business email compromise, investment fraud, and identity theft.
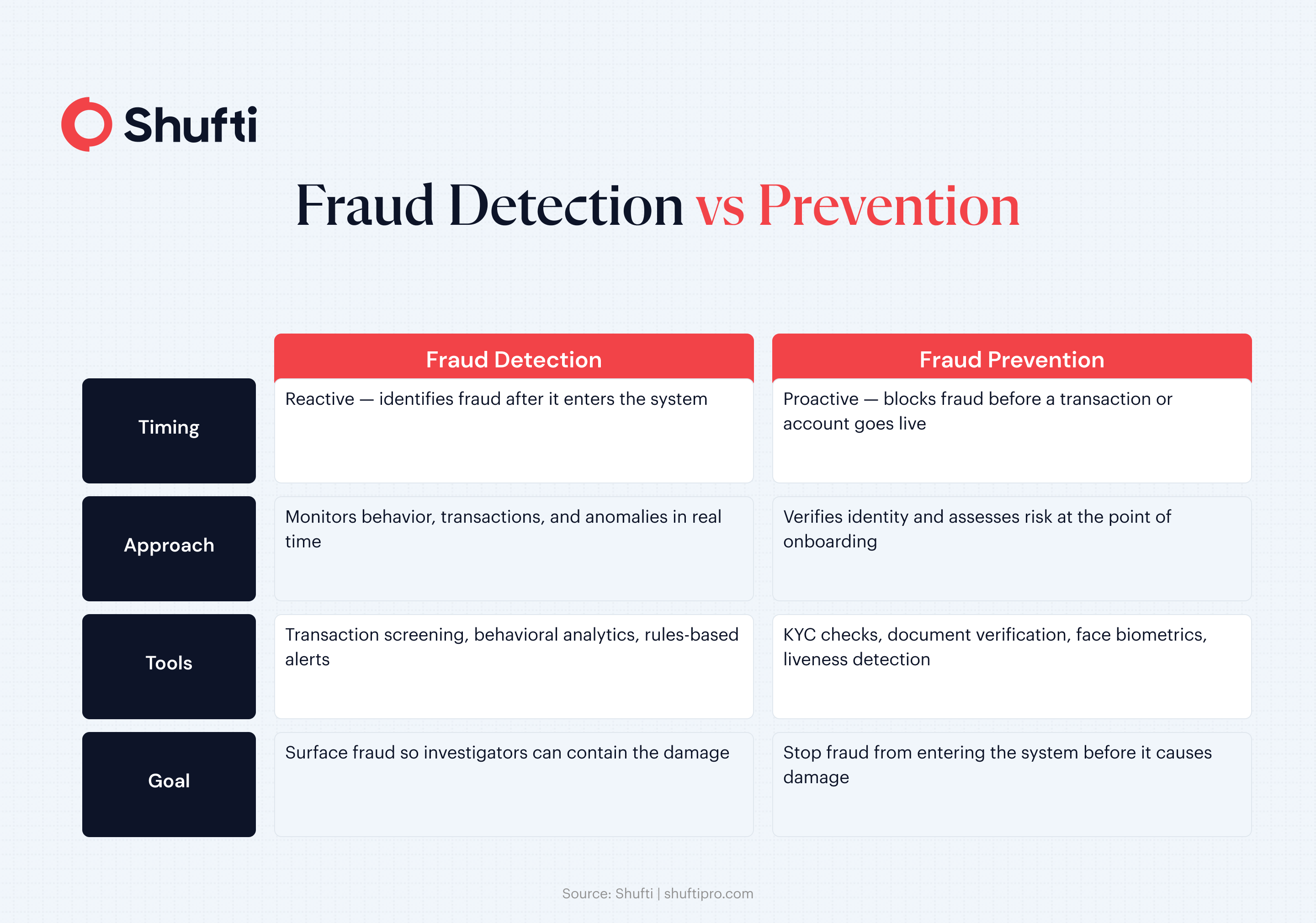
Most organizations respond to this exposure by adding more monitoring tools. What that approach misses is the distinction between two fundamentally different disciplines. Fraud detection identifies fraudulent activity after it has entered a system. Fraud prevention blocks it from entering in the first place. Treating them as interchangeable is why many fraud programs spend heavily on investigation while losses keep climbing.
A clear understanding of where each discipline starts and where it ends is the foundation of an effective fraud detection and prevention strategy.
Fraud Detection vs Fraud Prevention: The Core Difference
The two disciplines share a goal but operate at opposite ends of the fraud timeline, and that difference shapes every tool choice, team structure, and risk decision that follows.
Fraud prevention refers to controls applied before a transaction clears or an account goes live. Its purpose is to eliminate the conditions that allow fraud to occur. Know your customer (KYC) checks, document verification, and risk-based onboarding rules are all prevention mechanisms. They address whether a customer is who they claim to be before any financial relationship begins. If those controls work, a large category of fraud never reaches the system at all.
Fraud detection refers to the monitoring and analytical capabilities used to identify fraudulent activity once a customer relationship is underway. Transaction pattern analysis, device fingerprinting, and behavioral scoring fall into this category. Detection does not stop fraud at the door. It surfaces activity that slipped through so investigators can contain the damage.
The practical difference is timing. Prevention is proactive. Detection is reactive. Both are necessary, and neither is a substitute for the other. A business running strong detection with weak prevention is managing high fraud volumes rather than reducing them.
Which Comes First — Fraud Detection or Fraud Prevention?
Prevention always comes first. Fraud prevention controls screen customers before accounts are created. Fraud detection then monitors verified customers for anomalies. Reversing the sequence forces detection tools to carry the full burden of a problem prevention was designed to eliminate — raising costs and alert volumes simultaneously.
Why the Gap Between Detection and Prevention Is Costing Businesses
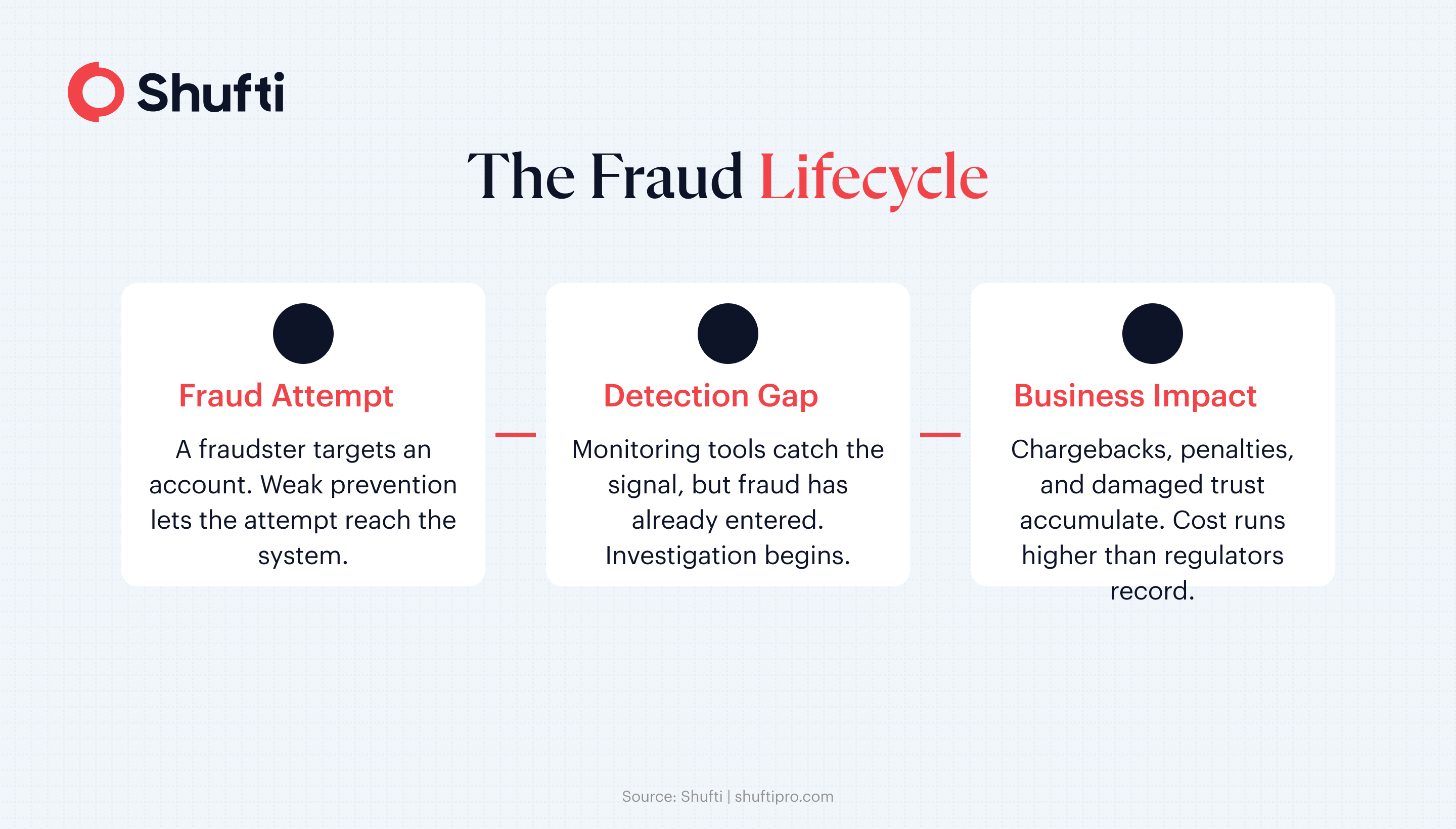
Businesses that invest heavily in post-transaction monitoring while leaving onboarding controls thin are building a fraud program that responds rather than resists. They pay for that choice in ways that rarely appear in a single report.
The $16.6 billion in adjusted losses recorded by the FBI’s Internet Crime Complaint Center in 2024 represents only what was reported and verified. Actual exposure runs higher. Businesses absorb losses that consumers never see. Chargebacks, compliance penalties, investigation costs, and account remediation expenses accumulate independently of what ends up in a regulatory filing.
The more pressing issue is what happens when the sequencing is wrong. When a fraudulent account gets through onboarding because no prevention control caught it, every subsequent transaction that account makes becomes a detection problem. Detection tools then work against a population that should have been screened out at the front door. This increases alert volume, stretches investigation teams, and raises the probability that genuine fraud signals are missed.
Real-time fraud detection helps close the response window when something gets through. It narrows the time between a fraudulent action and a business response. What it does not change is the exposure created when identity controls at onboarding are incomplete. Detection speed matters, but it is not a substitute for prevention depth.
What Are Examples of Proactive vs Reactive Fraud Strategies?
Proactive vs reactive fraud strategies differ at the point of intervention. Proactive examples include biometric onboarding, document authentication, and fraud identification methods like liveness detection. Reactive examples include chargeback investigation, account suspension after transaction flags, and post-incident forensics. Strong programs deploy both — fraud detection and prevention controls working together reduce the reactive caseload.
How Do Fraud Detection and Prevention Work Together?
When prevention and detection are designed as a connected system, each layer strengthens the other. Prevention narrows the population that detection tools need to monitor. Detection catches the cases that prevention did not stop.
A financial services company using identity verification at onboarding filters out synthetic identities and document fraud before accounts are created. Customers who clear those checks enter the system with an established identity. Monitoring tools can then focus on behavioral anomalies in a verified population rather than working against an unknown one.
Without that front-end filter, detection systems absorb the full volume of fraudulent account activity alongside legitimate customer behavior. Alert fatigue follows. Investigators are reviewing more cases with the same resources, and genuine signals get buried under lower-quality flags.
The layered model also improves investigation quality when fraud is detected. A flagged transaction tied to a verified identity gives investigators a starting point. A flagged transaction tied to a fraudulent identity from the start means every subsequent investigation is built on unreliable ground.
The FTC’s 2024 Consumer Sentinel data shows imposter scams and identity theft were the two highest-volume fraud categories by reports filed. Both have well-established prevention-layer responses at onboarding. For a closer look at how identity verification fits into this picture, see how AI-powered verification is changing fraud prevention.
What Tools Are Used for Fraud Monitoring and Real-Time Fraud Detection?
The tools divide cleanly between those that address the prevention layer and those that handle ongoing detection. Both work best when deployed in sequence rather than in isolation.
At onboarding, identity verification handles the prevention layer. Face verification with liveness detection confirms that the person opening an account is physically present and presenting genuine documents rather than a photo or a generated image. Combined with document authentication, this addresses the most common method of fraudulent account creation before the account exists.
Transaction screening shifts the focus to real-time detection once a customer is active. Each transaction is evaluated against behavioral baselines, velocity rules, and sanctions data. Payments that fall outside expected patterns for that customer and account type generate an alert or are held for review. The decision typically happens in milliseconds, before the transaction settles.
Device and behavioral analytics track how users interact with a platform across sessions. Login times, device signatures, navigation patterns, and typing cadence create a behavioral profile for each customer. When behavior deviates from that profile, an alert fires even when the credentials appear valid. This is particularly useful for detecting account takeover, where the underlying identity is legitimate but the session is not.
Rules-based alerting provides the baseline for most detection programs. Velocity limits, geographic anomalies, and transaction-size thresholds catch common fraud patterns quickly. Machine learning models complement rules by identifying patterns no rule was written to catch, adapting as fraud behavior evolves.
How Shufti handles prevention and detection together
Shufti’s identity verification platform covers the prevention layer at onboarding. Document authentication, face biometrics, and liveness detection complete in under 15 seconds, filtering fraudulent actors before they enter a business’s customer base. The platform processes over 10,000 document types across 240+ countries, covering the document diversity that cross-border fraud operations rely on.
For ongoing monitoring, Shufti’s AML screening draws on 100,000+ data sources and 3,500+ global watchlists, updated every 15 minutes. Sanctions checks, politically exposed person (PEP) screening, and adverse media monitoring run continuously against the active customer base. A customer whose risk profile changes after onboarding is caught at the next screening cycle rather than carried as undetected exposure.
When the two layers are connected, prevention and detection reinforce each other. Customers who clear onboarding enter monitoring with a verified identity. Monitoring tools flag anomalies against a confirmed baseline rather than an uncertain one. Investigation teams spend time on genuine cases rather than on sorting noise from a poorly filtered population.
Fraud losses increase when detection and prevention operate as separate programs rather than a connected system. Shufti’s platform closes that gap, providing verified identity at onboarding and continuous screening throughout the customer lifecycle. Request a demo to see how it works for your compliance and fraud teams.
Frequently Asked Questions
What is the main difference between fraud detection and fraud prevention?
Fraud prevention stops fraud before it enters a system through identity checks and onboarding controls. Fraud detection identifies fraud that is already occurring through behavioral monitoring and transaction analysis.
Which is more important for a business: fraud detection or fraud prevention?
Both are necessary. Prevention reduces the volume of fraud that reaches detection systems, and detection catches what prevention does not stop.
Can fraud detection work without fraud prevention in place?
It can, but at significantly higher cost and workload. Without prevention controls at onboarding, detection systems must process a larger share of fraudulent activity, driving up false positives and investigator burden.
What does real-time fraud detection mean in practice?
Real-time fraud detection evaluates transactions or behavioral signals as they happen, typically in milliseconds, and flags or blocks suspicious activity before it is processed or settled.
What are examples of proactive vs reactive fraud strategies?
Proactive strategies include identity verification at onboarding and liveness detection, fraud identification methods that stop fraud before it enters a system. Reactive strategies include transaction alerts, chargeback investigation, and account remediation after fraud has been identified.
What is the difference between proactive vs reactive fraud management?
Proactive vs reactive fraud management differs in timing. Proactive management uses prevention controls to stop fraud before it reaches a system. Reactive management relies on detection and response after fraudulent activity has already occurred. Effective programs run both in sequence.