The Role of Customer Identification Program in Compliance

Customer verification is an important first step in Know Your Customer (KYC)/Anti-Money Laundering (AML) compliance for financial service providers. If not for identification measures, individuals who exploit the financial system for terrorist financing, money laundering, and other financial crimes would be difficult to identify.
So how can financial institutions accurately identify their customers before onboarding?
This is where the Customer Identification Program (CIP) plays an important role. CIP is designed to help financial institutions verify their customers’ identities.
What is CIP?
In the United States, the CIP was introduced in 2003 under Section 326 of the USA Patriot Act to combat terrorism financing after the terrorist attack on 9/11. CIP in banking provides institutions with the foundation to verify their customers’ identities using basic personal information, through which financial institutions are able to develop a unique identity for each customer’s financial activity.
What is the Importance of CIP?
The importance of identification programs such as the CIP lies in their ability to protect financial institutions from becoming facilitators of illegal activities. With every financial activity conducted under the financial institution’s network being verified, CIP:
- Helps compliance teams with timely detection and subsequent prevention of illicit financial activity such as money laundering.
- Reduces fraud, particularly identity fraud, by verifying the customer’s identity.
- Ensures compliance with AML/CFT laws.
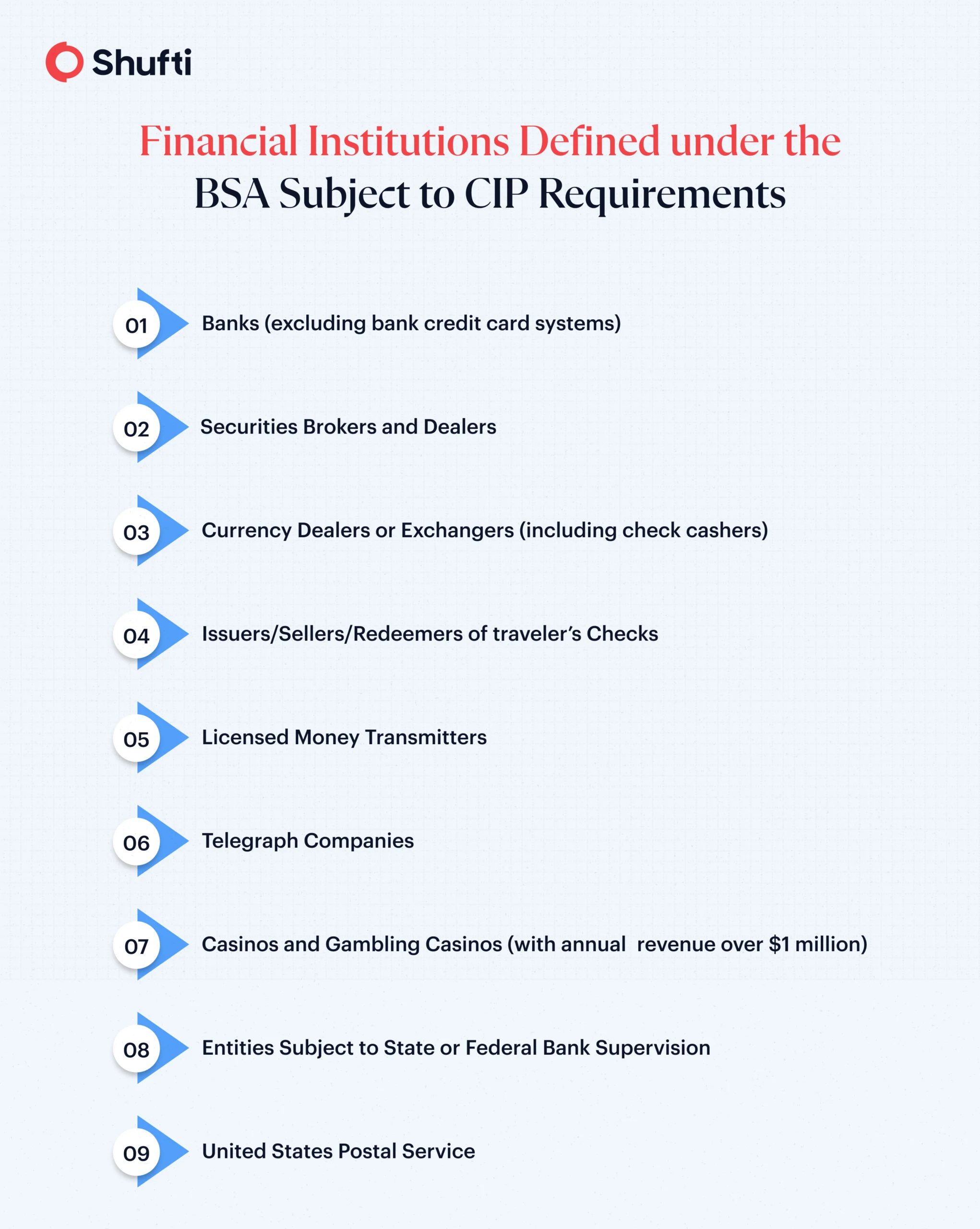
Which Institutions must follow the CIP Rule?
Every financial institution covered by the Bank Secrecy Act is legally obligated to incorporate the CIP rule into its KYC efforts. This list includes obvious examples such as traditional banks, brokers, and credit unions.
However, since the ultimate goal of the CIP is to aid financial institutions in preventing money laundering and countering terrorist financing, the CIP rule also extends to securities brokers, fintech companies, insurance companies, and even some money services businesses.
What are the CIP Requirements?
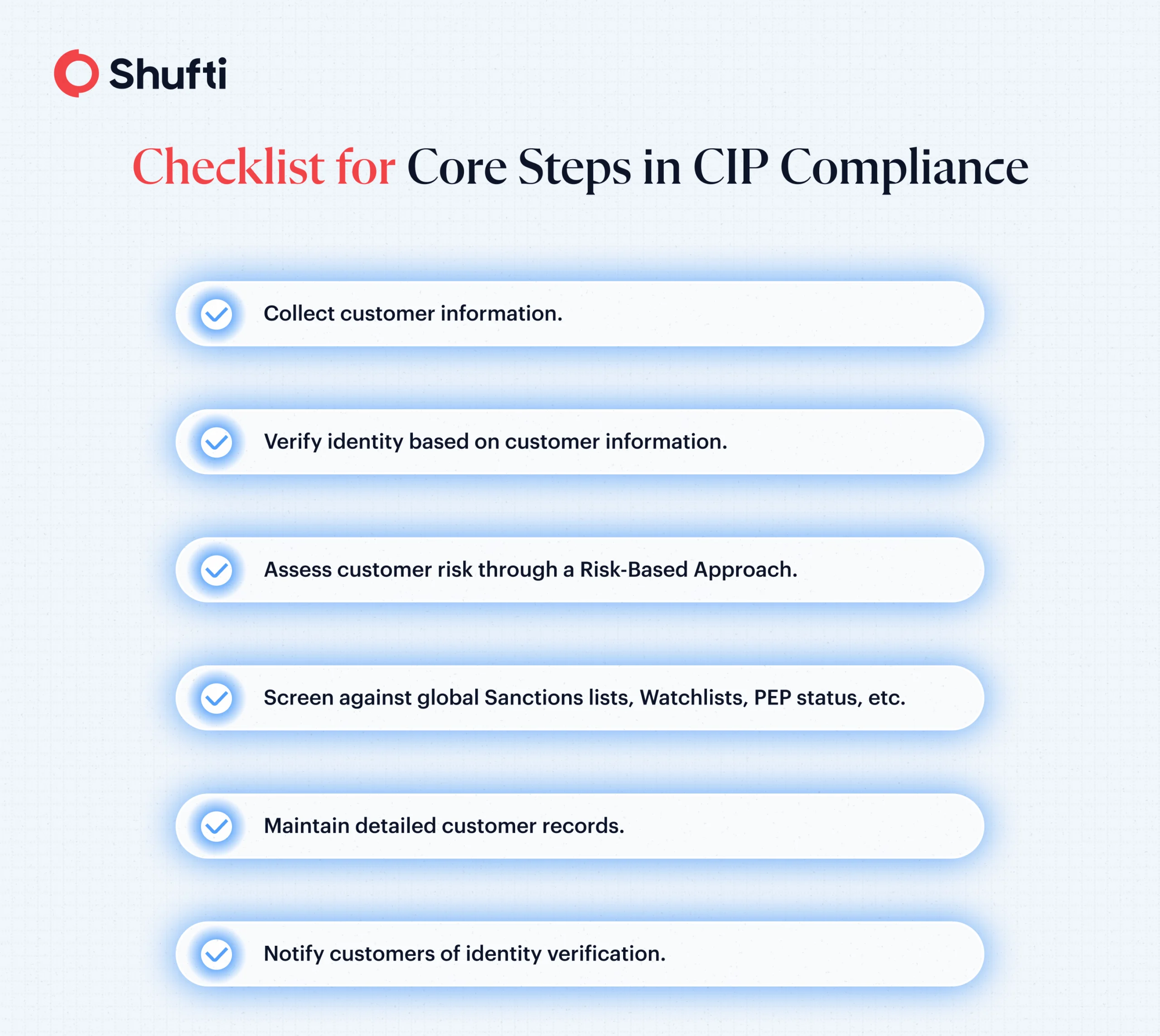
Section 236 of the USA Patriot Act sets out six main rules for CIP compliance that financial institutions must incorporate into their broader KYC efforts for verifying customer identity. These requirements include:
1. Customer Identification Procedure Document:
Institutions must have a written CIP document that outlines their CIP process, tailored to their needs and operational size.
2. Required Customer Information:
The minimum information obtained from a customer, as per FinCen, is the customer’s:
- Name
- Date of Birth
- Address
- Identification number, which shall be:
- A Taxpayer Identification Number (TIN) for a U.S. citizen
- A Passport Number and Country of Issuance, or any other government-issued document for a non-US citizen.
|
Did You Know? In June 2025, FinCEN introduced an exemption allowing financial institutions to verify Taxpayer Identification Numbers (TINs) from third-party sources rather than directly collect them from customers. This move addresses customer privacy concerns while still ensuring compliance with CIP regulations, providing a more secure and efficient customer onboarding process. |
3. Verification of Identity Procedure:
The CIP regulations require an institution to verify the identity of its customers “within a reasonable time after the account is opened.” Although FinCEN requires institutions to verify identity, it does not specify how that verification is to occur.
Therefore, financial institutions are free to choose their own procedures as long as they comply with the parameters set out by the USA Patriot Act. For instance, institutions may choose to obtain customer information through document identification or non-document ID verification measures.
4. Record-Keeping:
For the information obtained from the customer, the CIP shall include procedures for record-keeping. At a minimum, the record-keeping mechanism must include:
- Customer identification information
- Descriptions of any ID documents that were relied on, any identification number in the document, the issuing authority, and the date of issuance and expiration, if any.
- Any method that was undertaken to verify the identity of the customer.
- Description of how a substantive discrepancy was resolved, if any.
A FinCen-compliant financial institution shall keep records of customer identity information for 5 years after the account is closed.
5. Screening against Government Lists:
The CIP regulations also require financial institutions to have a procedure for screening their customers against any sanctions and terrorist watchlists issued by the U.S. government (such as OFAC). This is to ensure that the client is not a sanctioned individual and that the institution is not allowing a criminal to access the financial system.
6. Customer Notice:
To collect personal information from a customer for ID verification, the CIP shall include a customer notice mechanism that clearly explains why the customer is required to provide this information.
These six requirements form the core of the CIP, ensuring that financial institutions verify their customers’ identities effectively.
Key Components of Setting Up CIP:
To establish an effective CIP program that fulfils FinCen’s six CIP Rules, institutions may find it helpful to follow these practical steps.
- Identification processes, such as identity verification and record-keeping, make up the broader CIP procedures.
- The systems and tools that help institutions implement CIP (e.g., document scanning, third-party verification tools, and risk assessment software).
- The internal policies on how these components work cohesively, such as how customer data verification integrates with monitoring and compliance systems.
- The role of compliance officers is in overseeing CIP implementation of both CIP and broader KYC/AML regulations.
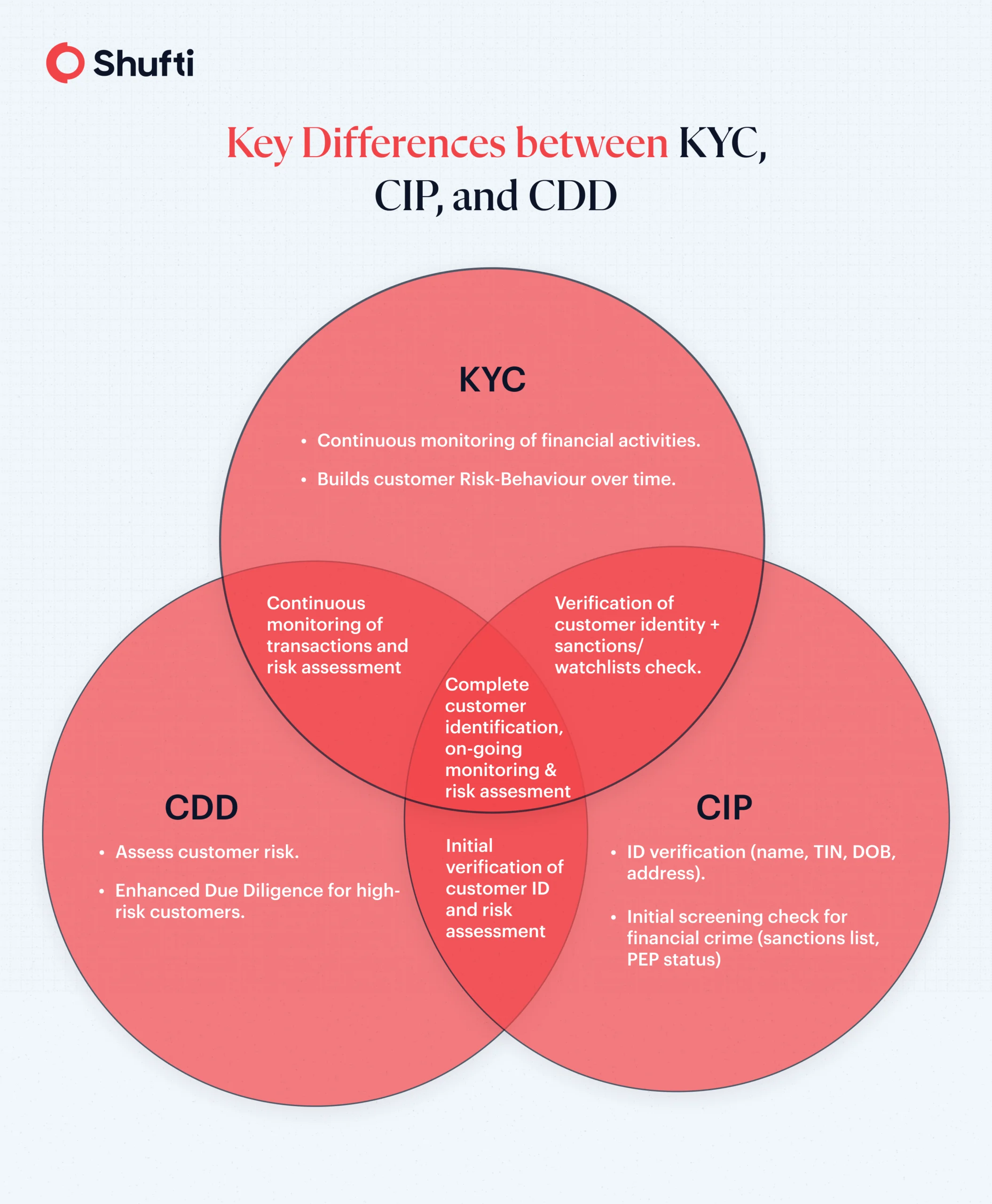
CIP vs KYC
Although CIP and KYC are often conflated, they differ in focus and scope.:
- CIP is an identity verification process carried out when a customer first opens an account. This process is used solely to verify the customer’s identity by collecting key information, such as their name, address, and TIN.
- KYC is a broader, ongoing process that not only involves CIP but also continuous risk assessments and customer due diligence.
So, what is the difference between CIP and KYC?
The CIP process is responsible for one thing only: verifying the identity of a customer. KYC refers to a long-term process that verifies customer identity (CIP) and conducts continuous risk assessments (CDD/EDD) of the customer for the time the account is open.
Thus, in the U.S., a KYC process involves:
- CIP – for verification of customer identity.
- Customer Due Diligence – for assessing customer risk over time
- Enhanced Due Diligence – for increased scrutiny of high-risk individuals, such as verification of wealth, to determine risk.
CIP vs CDD
CIP and CDD may refer to two entirely different aspects of the KYC process:
- CIP: A process focused on verifying the identity of customers when they open accounts.
- CDD: Involves perpetual monitoring of customer transactions and financial activities until the account is active. The CDD process helps assess the risk associated with a customer.
If the customer is high-risk, institutions gather further information about their financial activities, source of funds, and purpose of transactions to carry out enhanced due diligence measures.
How Shufti Makes CIP Compliance Effortless?
Without KYC solutions, establishing a CIP policy can be difficult for financial institutions. But with Shufti by your side, ensuring compliance with FinCen becomes hassle-free.
If your business falls under the BSA as a financial institution, having a thorough CIP is not only a good investment but a legal obligation.
Shufti can help your team meet CIP obligations without slowing down onboarding. Our solution system verifies identities in real time with:
- ID Document checks,
- Biometric checks (such as liveness detection)
- Non-Doc ID verification—a document-free approach built for digital banking journeys and low-friction sign-ups.
Integrate sanctions and watchlist screening into your CIP and flag risks against OFAC, UN, EU, and thousands of global lists that are kept current with high-frequency updates.
Make CIP compliance easier with Shufti. Book a demo today!
Frequently Asked Questions
What is a Customer Identification Program?
A Customer Identification Program (CIP) is a U.S regulatory process used by financial institutions to verify customers' identities when they open an account. It’s part of the KYC (Know Your Customer) process to prevent fraud, money laundering, and terrorist financing.
What is CIP due diligence?
CIP due diligence involves verifying customer identities, collecting personal information, and screening against government lists to ensure that customers are not involved in illegal activities. It’s a foundational step in the broader KYC process.
What is CIP in banking?
In banking, CIP refers to the procedures banks and financial institutions use to verify customers' identities during account setup. This is crucial for ensuring compliance with anti-money laundering (AML) and counter-terrorist financing (CTF) laws.