Cryptocurrency Market and Financial Crimes: How to Handle Transaction Monitoring

The adoption of cryptocurrencies by both individuals and businesses has exploded in the last 12 months. Institutions are now delivering cryptocurrency-related services to their clients in greater numbers than ever before. Furthermore, user engagement on cryptocurrency exchanges and platforms is also growing immensely than it has ever been. While the regulatory landscape for cryptocurrencies in different jurisdictions is far from finalized or guaranteed, one thing is obvious: institutions engaging in cryptocurrency will need to monitor their transactions and file suspicious activity reports (SARs) if unusual activity is identified.
A robust transaction monitoring solution can help businesses to overcome the risk of financial crimes associated with digital crypto money transactions. Innovative solutions have been developed to address the unique compliance problems that cryptocurrencies pose, particularly for transaction monitoring. One of the industry’s inherent risks is that no central authority can oversee or govern how blockchains operate. Businesses that conduct cryptocurrency transactions need to be aware of and comply with current cryptocurrency transaction monitoring requirements, as well as be on the lookout for potential new regulations.
Cryptocurrency Landscape and Rising Crimes
Cryptocurrencies are also known as virtual assets have emerged with new opportunities for consumers throughout the financial landscape, but they’re also upending how regulators and financial service providers deal with illicit risks like money laundering and terrorism funding.
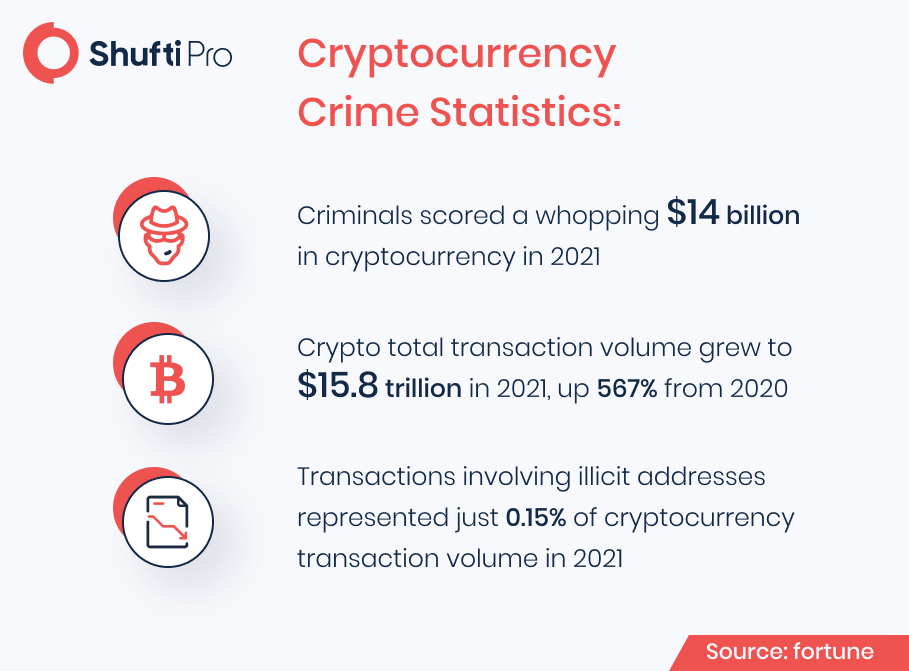
The potential threat that cryptocurrencies offer to the financial system is significant. According to studies, it was found that while total transaction volume across all cryptocurrencies grew by 567% to $15.8 trillion in 2021, illicit transactions increased by just 79%. To counteract this disruptive effect, regulators around the world have enacted new compliance rules to ensure that cryptocurrency service providers, as well as any institution dealing with cryptocurrency, can detect and prevent threats, and need to report authorities about emerging criminal methodologies.
The transaction monitoring process, which is a basis of effective Anti-Money Laundering (AML) protocol, requires organizations to examine their customers’ transactional behavior in order to detect attempts to perpetrate crimes such as money laundering. Because criminals may be able to conceal their identities and shift funds swiftly between accounts by taking advantage of the anonymity and speed of cryptocurrency services, transaction monitoring becomes both more vital and more difficult. In addition to this, financial and cryptocurrency service providers must understand how to modify and improve their AML transaction monitoring systems and measures to effectively deal with the rising risk of money laundering through cryptocurrencies and ensure that they remain compliant with the laws and standards in a shifting regulatory landscape to solve this challenge.
FATF’s Highlighted Red Flags for Cryptocurrency Money Laundering
The Financial Action Task Force (FATF) issued recommendations on the features of cryptocurrency money laundering schemes in 2020, based on internal investigations and member-state case studies. However, the regulatory body outlined a set of red flag indicators designed to help companies to enhance their transaction monitoring systems and better adapt to the changing risk landscape.
The following are some of the red flag symptoms of cryptocurrency money laundering:
- Transactional behavior: Suspicious cryptocurrency transaction patterns, such as high transaction frequency in a short period of time or quick deposits and withdrawals of funds into a newly formed account.
- Geographical risks: Cryptocurrency transactions that are carried out into or out of high-risk nations or jurisdictions, or that send currency to exchange outside of the customer’s home country.
- Structured transactions: Multiple cryptocurrency transactions that are deliberately structured in amounts that do not trigger reporting thresholds.
- Anonymous transactions: Criminals that want to take advantage of the anonymity of cryptocurrencies can utilize privacy coins, trade on unlicensed exchanges, or trade through proxies. Criminals may also try to use the same IP address to operate numerous cryptocurrency wallets anonymously.
- Inadequate CDD: Cryptocurrency transactions involving accounts with insufficient customer due diligence who have refused or avoided inquiries for identifying information.
- Money-muling: Customers who are elderly or financially vulnerable, or who appear to be unaware of the risk associated with cryptocurrencies, may be exploited as mules to carry out transactions for money launderers.
Building an Effective Transaction Monitoring Control System
Between 2018 and 2019, the FATF Recommendations were revised, and new guidance on cryptocurrency service providers was provided, bringing them under the existing AML/CFT compliance rules. Cryptocurrency companies need to implement risk-based transaction monitoring systems that capture the money laundering risk that their customers pose as part of their new obligations.
In practice, this means that businesses should conduct risk assessments on their consumers and implement continuing to Know Your Customer (KYC) practices to verify that the assessment is correct. KYC is another pillar of traditional AML transaction monitoring, and it’s just as important in the crypto world since it helps companies identify their customers and their financial history to develop risk profiles.
With that in mind, key compliance considerations for cryptocurrency transaction monitoring include:
Customer Due Diligence (CDD): Financial businesses and crypto service providers should conduct rigid customer due diligence procedures on their customers in order to develop a risk profile and enhance transaction monitoring systems. To do so, the businesses are obliged to gather personally identifiable information including government-issued identity documents or even financial statements.
Screening and monitoring: Digital crypto money service providers need to integrate anti-money laundering screening solutions into their security systems that will help them to screen customers against the global sanction lists, financial crime databases, and PEPs list. This will ensure that legit customers get on board. In addition to this, to make AML control systems more rigid, transaction monitoring measures are also needed to be placed effectively to assure that no suspicious transactions get undetected.
Smart technology: Transaction monitoring in the cryptocurrency market involves gathering and analyzing the vast amount of data that is quite impossible for humans to process. However, to maintain and process data the service providers need to integrate tech-driven verification solutions to make the transaction and onboarding experience robust, secure, and seamless. Moreover, emerging technologies are also putting value in security and verification systems.
Final Thoughts
To address financial crimes and anonymity associated with digital currencies, anti-money laundering and transaction monitoring solutions are essential. Verifying the customers’ identities while staying compliant with the AML regulations is getting the need of the hour. Thus, gathering customers’ identity information can help businesses to maintain records with high transparency.
Shufti’s state-of-the-art anti-money laundering and transaction monitoring services are considered a viable option for the cryptocurrency businesses, as it allows customers verification by screening them against 1700+ watchlists in less than a second with 98.67%.
Do you need more information on AML for the cryptocurrency industry? Talk to our experts right away!